Endpoint Protection
This section describes the Endpoint Protection feature and how to configure it.
The following topics are included in this section:
- Endpoint Protection overview
- Configuration overview
- Creating a FortiClient profile
- Enabling Endpoint Protection in security policies
- Configuring endpoint registration over a VPN
- Monitoring endpoints
- Modifying the Endpoint Protection replacement messages
Endpoint Protection overview
Endpoint Protection enforces the use of up-to-date FortiClient Endpoint Security software on endpoints (workstation computers and mobile devices). It pushes a FortiClient profile to the FortiClient application, specifying security settings, including:
- Real-time antivirus protection - on or off
- FortiClient web category filtering based on web filters defined in a FortiGate web filter profile
- FortiClient application control (application firewall) using application sensors defined in the FortiGate application control feature
The FortiClient profile can also specify:
- VPN configurations
- Configuration profile (.mobileconfig file for iOS)
- Dashboard banner
You enable Endpoint Security in security policies by enabling Compliant with FortiClient Profile. The policy must specify at least one device type.
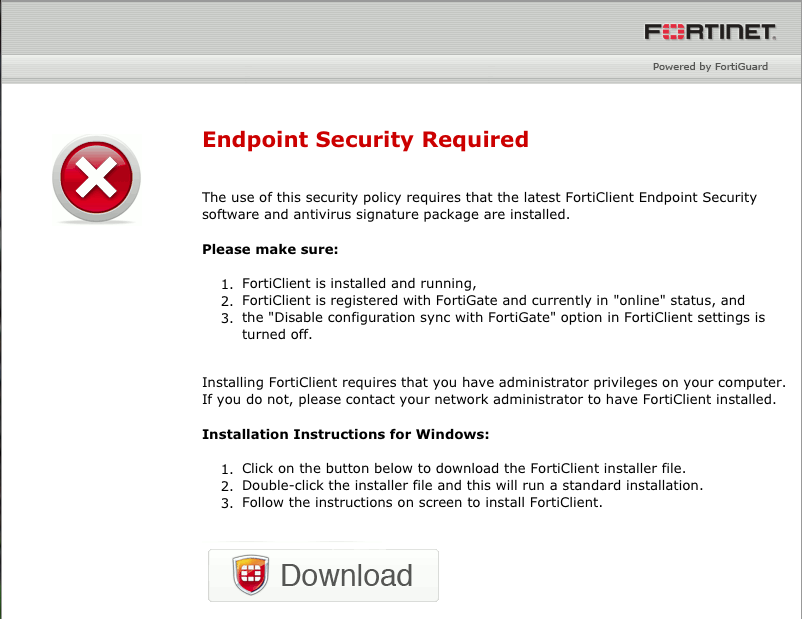
User experience
When using a web browser, the user of a non-compliant endpoint receives a replacement message HTML page from the FortiGate unit. The message explains that the user needs to install FortiClient Endpoint Security and provides a link to do so. The user cannot continue until the FortiClient software is installed.
For information about modifying the replacement page, see Modifying the Endpoint Protection replacement messages.
Default FortiClient non-compliance message for Windows
After installing FortiClient Endpoint Security, the user will receive an invitation to register with the FortiGate unit. If the user accepts the invitation, the FortiClient profile is sent to the device's FortiClient application. Now the user is compliant with the security policy and can connect to the network. FortiClient Endpoint Security registered with a FortiGate unit does not need to be separately licensed with FortiGuard.
The FortiGate unit can also register endpoints who connect over the Internet through a VPN. The user can accept an invitation to register with the FortiGate unit. See Configuring endpoint registration over a VPN.
FortiGate endpoint registration limits
To view the number of endpoints that are registered and the total that can be registered, go to System > Dashboard > Status. Under License Information, find FortiClient. You will see a line like “Registered/Allowed 4 of 10”. This means that there are four registered endpoints and a total of ten are allowed.
When the registration limit is reached, the next FortiClient-compatible device will not be able to register with the FortiGate unit. The user sees a message in FortiClient application about this. The FortiClient profile is not sent to client and the client cannot connect through the FortiGate unit.
For all FortiGate models, the maximum number of registered endpoints is ten. For all models except 20C, you can purchase an endpoint license to increase this capacity:
To add an endpoint license - web-based manager
- Go to System > Dashboard > Status.
- In the License Information widget, under FortiClient, select Enter License, enter the license key, and select OK.
Maximum registered endpoints with endpoint license
| Model type | Max Registered Endpoints |
|---|---|
| 30 to 90 series | 200 |
| 100 to 300 series | 600 |
| 500 to 800 series, VM1, VM2 | 2 000 |
| 1000 series, VM4 | 8 000 |
| 3000 to 5000 series, VM8 | 20 000 |
Configuration overview
Endpoint Protection requires that all hosts using the firewall policy have the FortiClient Endpoint Security application installed. Make sure that all hosts affected by this policy are able to install this application. Currently, FortiClient Endpoint Security is available for Microsoft Windows (2000 and later) and Apple Mac OSX only.
To set up Endpoint Protection, you need to:
- By default, the FortiGuard service provides the FortiClient installer. If you prefer to host it on your own server, see Changing the FortiClient installer download location, below.
- In Security Profiles, configure application sensors and web filter profiles as needed to monitor or block applications. See the Security Profiles Guide for details.
- Create a FortiClient profile or use the default profile. See Creating a FortiClient profile. Enable the application sensor and web category filtering profiles that you want to use.
- Enable Compliant with FortiClient Profile in the security policies that the endpoints will use.
- Create the registration key for users to register their device with the FortiGate unit.
- Optionally, configure the FortiGate unit to support endpoint registration by IPsec or SSL VPN.
- Optionally, modify the Endpoint NAC Download Portal replacement messages (one per platform).
Changing the FortiClient installer download location
By default, FortiClient installers are downloaded from the FortiGuard network. You can also host these installers on a server for your users to download. In that case, you must configure FortiOS with this custom download location. For example, to set the download location to a customer web server with address custom.example.com, enter the following command:
config endpoint-control settings
set download-location custom
set download-custom-link "http://custom.example.com"
end
Creating a FortiClient profile
There is a default FortiClient profile for Windows and Mac OS that enables only AntiVirus, Web Filtering, and VPN. You can modify this profile or create your own FortiClient profiles.
Except for the default profile, each FortiClient profile is assigned to particular device groups, and optionally to particular users and user groups. If no other FortiClient profile is assigned to a particular device type, the default profile applies. It is possible for more than one profile to be assigned to a device type. As with security policies, clients are matched to FortiClient profiles in the order that the profiles appear in the list.
When Compliant with FortiClient Profile is selected in the security policy, all users of that policy must have FortiClient Endpoint Security installed. The FortiGate unit pushes the FortiClient profile settings to the FortiClient application on the client.
To create a FortiClient profile - web-based manager
- If you will use the Application Firewall feature, go to Security Profiles > Application Control to create the Application Sensors that you will need.
- If you will use Web Category Filtering, go to Security Profiles > Web Filter to create the web filter profile that you will need.
- Go to User & Device > FortiClient Profiles.
If there is only the default FortiClient profile, it is displayed, ready to edit. At the top right of the page you can select or create other profiles. - Select Create New or select an existing profile and Edit it.
- In Assign Profile To, select the device groups, user groups, and users to which this FortiClient profile applies. This is not available for the default profile.
- Enter the FortiClient Configuration Deployment settings for Windows and Mac:
| Antivirus Protection | ON — enable the FortiClient realtime AntiVirus feature. | |
| Web Category Filtering | ON — enable web category filtering. Select the web filter profile to use. | |
| Client Web Filtering when On-Net | Enable to use FortiClient web filtering. | |
| VPN | ON - enable VPN use by FortiClient. | |
| Client VPN Provisioning | Enable to configure the FortiClient VPN client. Enter the VPN configuration details. | |
| Application Firewall | ON — enable application control. Select the application sensor to use. | |
| Upload Logs to FortiAnalyzer / FortiManager | ON — enable log upload. Specify log device and select schedule. | |
| Use FortiManager for client software/signature update | ON — FortiClient software obtain AV signatures and software updates from the specified FQDN or IP address. Failover to FDN when FortiManager is not available is enabled by default. | |
| Dashboard Banner | ON — Display dashboard banner. | |
| Client-based Logging when On-Net |
ON — FortiClient will continue to log even when its traffic is flowing through a FortiGate unit. | |
- Enter the FortiClient Configuration Deployment settings for iOS:
| Web Category Filtering | ON — enable web category filtering. Select the web filter profile to use. | |
| Client Web Filtering when On-Net |
Enable to use FortiClient web filtering. | |
| Client VPN Provisioning | Enable to configure the FortiClient VPN client. You can enter multiple VPN configurations by selecting the “+” button. | |
| VPN Name | Enter a name to identify this VPN configuration in the FortiClient application. | |
| Type | Select IPsec or SSL-VPN. If you select IPsec, select a VPN Configuration File that contains the required IPsec VPN configuration. The Apple iPhone Configuration Utility produces .mobileconfig files which contain configuration information for an iOS device. If you select SSL-VPN, enter the VPN configuration details. |
|
| Distribute Configuration Profile | ON — Distribute configuration information to iOS devices running FortiClient Endpoint Security. Select Browse and locate the file to be distributed. The Apple iPhone Configuration Utility produces .mobileconfig files which contain configuration information for an iOS device. |
|
- Enter the FortiClient Configuration Deployment settings for Android:
| Web Category Filtering | ON — enable web category filtering. Select the web filter profile to use. | |
| Client Filtering when On-Net | Disables FortiClient web category filtering when client traffic is filtered by the FortiGate unit. Selected by default. | |
| Client VPN Provisioning | Enable to configure the FortiClient VPN client. You can enter multiple VPN configurations by selecting the “+” button. | |
| VPN Name | Enter a name to identify this VPN configuration in the FortiClient application. | |
| Type | Select IPsec or SSL-VPN. Enter the VPN configuration details. | |
- Select OK.
To create a FortiClient profile - CLI:
This example creates a profile for Windows and Mac computers.
config endpoint-control profile
edit ep-profile1
set device-groups mac windows-pc
config forticlient-winmac-settings
set forticlient-av enable
set forticlient-wf enable
set forticlient-wf-profile default
end
end
Creating the registration key
To register their endpoint devices with the FortiGate unit, users must enter a registration key that you create and provide to them.
To create the FortiClient Endpoint Registration key
- Go to System > Config > Advanced.
- Enable FortiClient Endpoint Registration and enter the key.
You can create a key containing up to 127 alphanumeric characters. - Select Apply.
Enabling Endpoint Protection in security policies
Endpoint Protection is applied to any traffic where the controlling firewall policy has Endpoint Security enabled. The device group to which the device belongs determines which FortiClient profile is applied. The policy searches the list of FortiClient profiles starting from the top and applies the first profile assigned to the device group.
To enable Endpoint Protection - web-based manager:
- Go to Policy & Objects > Policy > IPv4 and edit the security policy where you want to enable Endpoint Protection.
The policy must specify at least one Source Device Type. - Select Compliant with FortiClient profile.
- Select OK.
To configure the firewall policy - CLI:
In this example, the LAN connects to Port 2 and the Internet is connected to Port 1. a FortiClient profile is applied.
config firewall policy
edit 0
set srcintf port2
set dstintf port1
set srcaddr LANusers
set dstaddr all
set devices employee\ laptop
set schedule always
set service ALL
set devices all
set action accept
set nat enable
set endpoint-compliance enable
end
Configuring endpoint registration over a VPN
FortiGate units can register FortiClient-equipped endpoints over either an interface-based IPsec VPN or a tunnel-mode SSL VPN. After the user authenticates, the FortiGate unit sends the FortiClient application the IP address and port to be used for registration. If the user accepts the FortiGate invitation to register, registration proceeds and the FortiClient profile is downloaded to the client.
Users without FortiClient Endpoint Security connecting to the SSL VPN through a browser are redirected to a captive portal to download and install the FortiClient software.
Endpoint registration on an IPsec VPN
You can enable endpoint registration when you configure the FortiClient VPN or you can enable it on an existing FortiClient VPN.
To enable endpoint registration while configuring the VPN
- Enable Allow Endpoint Registration on the Policy & Routing page of the VPN Wizard when creating the FortiClient VPN.
To enable endpoint registration on an existing VPN
- Go to System > Network > Interfaces and edit the VPN’s tunnel interface.
The tunnel is a subinterface of the physical network interface. - In Administrative Access, make sure that FCT-Access is enabled.
- Select OK.
Endpoint registration on an SSL VPN
To enable endpoint registration on the SSL VPN
- Go to VPN > SSL > Settings.
- In Tunnel Mode Client Settings, make sure Allow Endpoint Registration is enabled.
- Select Apply.
This procedure does not include all settings needed to configure a working SSL VPN.
Synchronizing endpoint registrations
To support roaming users in a network with multiple FortiGate units, you need to configure synchronization of the endpoint registration databases between the units. The registered endpoints are then recognized on all of the FortiGate units. This is configured in the CLI. For example, to synchronize this FortiGate unit’s registered endpoint database with another unit named other1 at IP address 172.20.120.4, enter:
config endpoint-control forticlient-registration-sync
edit other1
set peer-ip 172.20.120.4
end
Monitoring endpoints
Go to User & Device > Monitor > FortiClient to monitor endpoints.
Modifying the Endpoint Protection replacement messages
If the security policy has Redirect all non-compliant/unregistered FortiClient compatible devices to a captive portal enabled, users of non-compliant devices are redirected to a captive portal that is defined by the Endpoint NAC Download Portal replacement message. There are different portals for Android, iOS, Mac, Windows, and “other” devices. Optionally, you can modify them.
To modify the Endpoint NAC Download Portal
- Go to System > Config > Replacement Message Group and select Extended View.
- In the Endpoint Control section select the message that you want to edit.
The replacement message and its HTML code appear in a split screen in the lower half of the page. - Modify the text as needed and select Save.

