Configuration overview
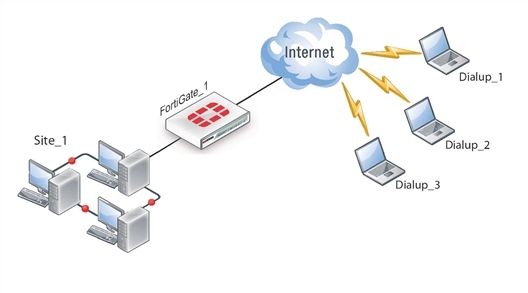
Dialup users typically obtain dynamic IP addresses from an ISP through Dynamic Host Configuration Protocol (DHCP) or Point-to-Point Protocol over Ethernet (PPPoE). Then, the FortiClient Endpoint Security application initiates a connection to a FortiGate dialup server.
By default the FortiClient dialup client has the same IP address as the host PC on which it runs. If the host connects directly to the Internet, this is a public IP address. If the host is behind a NAT device, such as a router, the IP address is a private IP address. The NAT device must be NAT traversal (NAT-T) compatible to pass encrypted packets (see Phase 1 parameters). The FortiClient application also can be configured to use a virtual IP address (VIP). For the duration of the connection, the FortiClient application and the FortiGate unit both use the VIP address as the IP address of the FortiClient dialup client.
For a faster and easier method of configuring a FortiGate-to-FortiClient VPN, see One button FortiGate-to-FortiClient Phase 1 VPN.
The FortiClient application sends its encrypted packets to the VPN remote gateway, which is usually the public interface of the FortiGate unit. It also uses this interface to download VPN settings from the FortiGate unit. See Automatic configuration of FortiClient dialup clients.
Example FortiClient dialup-client configuration
Peer identification
The FortiClient application can establish an IPsec tunnel with a FortiGate unit configured to act as a dialup server. When the FortiGate unit acts as a dialup server, it does not identify the client using the Phase 1 remote gateway address. The IPsec tunnel is established if authentication is successful and the IPsec security policy associated with the tunnel permits access. If configured, the FortiGate unit could also require FortiClient registration, that is, the remote user would be required to have FortiClient installed before connection is completed.
There are several different ways to authenticate dialup clients and restrict access to private networks based on client credentials. For more information, see Phase 1 parameters.
Automatic configuration of FortiClient dialup clients
The FortiClient application can obtain its VPN settings from the FortiGate VPN server. FortiClient users need to know only the FortiGate VPN server IP address and their user name and password on the FortiGate unit.
The FortiGate unit listens for VPN policy requests from clients on TCP port 8900. When the dialup client connects:
- The client initiates a Secure Sockets Layer (SSL) connection to the FortiGate unit.
- The FortiGate unit requests a user name and password from the FortiClient user. Using these credentials, it authenticates the client and determines which VPN policy applies to the client.
- Provided that authentication is successful, the FortiGate unit downloads a VPN policy to the client over the SSL connection. The information includes IPsec Phase 1 and Phase 2 settings, and the IP addresses of the private networks that the client is authorized to access.
- The client uses the VPN policy settings to establish an IPsec Phase 1 connection and
Phase 2 tunnel with the FortiGate unit.
One button FortiGate-to-FortiClient Phase 1 VPN
On the FortiOS VPN IKE page there is a method to create a Phase 1 portion of a VPN tunnel between the FortiGate and FortiClient. Very little information is required for this configuration. No encryption or authentication method is required. This feature is ideal for setting up quick VPN connections with basic settings.
On the Phase 1 screen is the option Create a FortiClient VPN. When selected, the FortiGate uint requires a few basic VPN configuration related questions. Once all the information is added, select OK. This will create a new dial-up IPsec-interface mode tunnel. Phase 1 and Phase 2 will be added using the default IKE settings.
The following Settings will be used when creating a one-button FortiClient VPN Phase 1 object:
- Remote Gateway: Dialup User
- Mode: Aggressive
- Default setting for Phase 1 and 2 Proposals
- XAUTH Enable as Server (Auto)
- IKE mode-config will be enabled
- Peer Option set to “Any peer ID”
- Rest of the setting use the current defaults (Default value needs to be the same on FCT side)
Once the completed, you need tocreate a default Phase 2 configuration. This only requires a name for the Phase 2 object, and select the FortiClient connection Phase 1 name.
How the FortiGate unit determines which settings to apply
The FortiGate unit follows these steps to determine the configuration information to send to the FortiClient application:
- Check the virtual domain associated with the connection to determine which VPN policies might apply.
- Select the VPN policy that matches the dialup client’s user group and determine which tunnel (Phase 1 configuration) is involved.
- Check all IPsec security policies that use the specified tunnel to determine which private networks the dialup clients may access.
- Retrieve the rest of the VPN policy information from the existing IPsec Phase 1 and Phase 2 parameters in the dialup-client configuration.
Using virtual IP addresses
When the FortiClient host PC is located behind a NAT device, unintended IP address overlap issues may arise between the private networks at the two ends of the tunnel. For example, the client’s host might receive a private IP address from a DHCP server on its network that by co-incidence is the same as a private IP address on the network behind the FortiGate unit. A conflict will occur in the host’s routing table and the FortiClient Endpoint Security application will be unable to send traffic through the tunnel. Configuring virtual IP (VIP) addresses for FortiClient applications prevents this problem.
Using VIPs ensures that client IP addresses are in a predictable range. You can then define security policies that allow access only to that source address range. If you do not use VIPs, the security policies must allow all source addresses because you cannot predict the IP address for a remote mobile user.
The FortiClient application must not have the same IP address as any host on the private network behind the FortiGate unit or any other connected FortiClient application. You can ensure this by reserving a range of IP addresses on the private network for FortiClient users. Or, you can assign FortiClient VIPs from an uncommonly used subnet such as 10.254.254.0/24 or 192.168.254.0/24.
You can reserve a VIP address for a particular client according to its device MAC address and type of connection. The DHCP server then always assigns the reserved VIP address to the client. For more information about this feature, see the “dhcp reserved-address” section in the “system” chapter of the FortiGate CLI Reference.
|
|
On the host computer, you can find out the VIP address that the FortiClient Endpoint Security application is using. For example, in Windows command prompt, type ipconfig /allOn Linux or Mac OS X, type ifconfig in a terminal window. The output will also show the IP address that has been assigned to the host Network Interface Card (NIC). |
It is best to assign VIPs using DHCP over IPsec. The FortiGate dialup server can act as a DHCP server or relay requests to an external DHCP server. You can also configure VIPs manually on FortiClient applications, but it is more difficult to ensure that all clients use unique addresses.
|
|
If you assign a VIP on the private network behind the FortiGate unit and enable DHCP-IPsec (a Phase 2 advanced option), the FortiGate unit acts as a proxy on the local private network for the FortiClient dialup client. Whenever a host on the network behind the dialup server issues an ARP request for the device MAC address of the FortiClient host, the FortiGate unit answers the ARP request on behalf of the FortiClient host and forwards the associated traffic to the FortiClient host through the tunnel. For more information, see Phase 2 parameters. |
FortiGate units fully support RFC 3456. The FortiGate DHCP over IPsec feature can be enabled to allocate VIP addresses to FortiClient dialup clients using a FortiGate DHCP server.
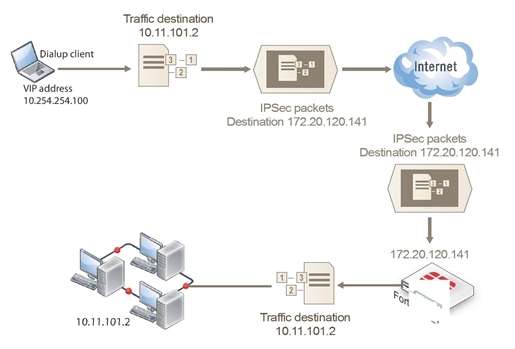
The figure below shows an example of a FortiClient-to-FortiGate VPN where the FortiClient application is assigned a VIP on an uncommonly used subnet. The diagram also shows that while the destination for the information in the encrypted packets is the private network behind the FortiGate unit, the destination of the IPsec packets themselves is the public interface of the FortiGate unit that acts as the end of the VPN tunnel.
IP address assignments in a FortiClient dialup-client configuration
Assigning VIPs by RADIUS user group
If you use XAuth authentication, you can assign users the virtual IP address stored in the Framed‑IP‑Address field of their record on the RADIUS server. (See RFC 2865 and RFC 2866 for more information about RADIUS fields.) To do this:
- Set the DHCP server IP Assignment Mode to User-group defined method. This is an Advanced setting. See Configuration overview.
- Create a new firewall user group and add the RADIUS server to it.
- In your Phase 1 settings, configure the FortiGate unit as an XAuth server and select from User Group the new user group that you created. For more information, see Phase 1 parameters.
- Configure the FortiClient application to use XAuth. See Configuration overview.
FortiClient dialup-client infrastructure requirements
- To support policy-based VPNs, the FortiGate dialup server may operate in either NAT mode or transparent mode. NAT mode is required if you want to create a route-based VPN.
- If the FortiClient dialup clients will be configured to obtain VIP addresses through FortiGate DHCP relay, a DHCP server must be available on the network behind the FortiGate unit and the DHCP server must have a direct route to the FortiGate unit.
- If the FortiGate interface to the private network is not the default gateway, the private network behind the FortiGate unit must be configured to route IP traffic destined for dialup clients back (through an appropriate gateway) to the FortiGate interface to the private network. As an alternative, you can configure the IPsec security policy on the FortiGate unit to perform inbound NAT on IP packets. Inbound NAT translates the source addresses of inbound decrypted packets into the IP address of the FortiGate interface to the local private network.

