Basic Administration
This section contains information about basic FortiGate administration that can be done after you have installed the unit in your network.
While this section mainly focuses on tasks done using the web-based manager, some tasks include instructions to use the command line interface (CLI). You can connect to the CLI using the CLI widget, FortiExplorer, or by connecting using a SSH or Telnet connection. For more information about the CLI, see the System Administration handbook.
The following topics are included in this section:
Registration
In order to have full access to Fortinet Support and FortiGuard Services, you must register your FortiGate unit.
Registering your FortiGate:
- Go to System > Dashboard > Status and locate the License Information widget.
- Select Register.
- In the pop-up window, either use an existing Fortinet Support account or create a new one. Select your Country and Reseller.
- Select OK.
System Settings
There are several system settings that should be configured once your FortiGate is installed.
Default administrator password
By default, your FortiGate has an administrator account set up with the username admin and no password. In order to prevent unauthorized access to the FortiGate, it is highly recommended that you add a password to this account.
To change the default password:
- Go to System > Admin > Administrators.
- Edit the admin account.
- Select Change Password.
- Leave Old Password blank, enter the New Password and re-enter the password for confirmation.
- Select OK.
For details on selecting a password and password best practices, see Passwords.
Language
The default language of the web-based manager is English. To change the language, go to System > Admin > Settings. In the Display Settings section, select the language you want from the Language drop-down list. For best results, you should select the language that is used by the management computer.
Time and date
For effective scheduling and logging, the FortiGate system date and time should be accurate. You can either manually set the system date and time or configure the FortiGate unit to automatically keep its time correct by synchronizing with a Network Time Protocol (NTP) server.
The Network Time Protocol enables you to keep the FortiGate time in sync with other network systems. By enabling NTP on the FortiGate unit, FortiOS will check with the NTP server you select at the configured intervals. This will also ensure that logs and other time-sensitive settings on the FortiGate unit are correct.
The FortiGate unit maintains its internal clock using a built-in battery. At startup, the time reported by the FortiGate unit will indicate the hardware clock time, which may not be accurate. When using NTP, the system time might change after the FortiGate has successfully obtained the time from a configured NTP server.
|
|
By default, FortiOS has the daylight savings time configuration enabled. The system time must be manually adjusted after daylight saving time ends. To disable DST, enter the following command in the CLI:config system global set dst disableend |
To set the date and time
- Go to System > Dashboard > Status and locate the System Information widget.
- Beside System Time, select Change.
- Select your Time Zone.
- Either select Set Time and manually set the system date and time, or select Synchronize with NTP Server. If you select synchronization, you can either use the default FortiGuard servers or specify a different server. You can also set the Sync Interval.
- Select OK.
If you use an NTP server, you can identify a specific port/IP address for this self-originating traffic. The configuration is performed in the CLI with the command set source-ip. For example, to set the source IP of NTP to be on the DMZ1 port with an IP of 192.168.4.5, the commands are:
config system ntp
set ntpsyn enable
set syncinterval 5
set source-ip 192.168.4.5
end
Idle timeout
By default, the web-based manager disconnects administrative sessions if no activity occurs for five minutes. This prevents someone from using the web‑based manager if the management PC is left unattended.
To change the idle timeout
- Go to System > Admin > Settings.
- In the Administration Settings section, enter the time in minutes in the Idle Timeout field
- Select Apply.
Administrator password retries and lockout time
By default, the FortiGate unit includes set number of three password retries, allowing the administrator a maximum of three attempts to log into their account before they are locked out for a set amount of time (by default, 60 seconds).
The number of attempts can be set to an alternate value, as well as the default wait time before the administrator can try to enter a password again. You can also change this to further sway would-be hackers. Both settings are must be configured with the CLI
To configure the lockout options:
config system global
set admin-lockout-threshold <failed_attempts>
set admin-lockout-duration <seconds>
end
For example, to set the lockout threshold to one attempt and a five minute duration before the administrator can try again to log in enter the commands”
config system global
set admin-lockout-threshold 1
set admin-lockout-duration 300
end
Administrative port settings
In order to improve security, you can change the default port configurations for administrative connections to the FortiGate. When connecting to the FortiGate unit when the port has changed, the port must be included, such as https://<ip_address>:<port>. For example, if you are connecting to the FortiGate unit using port 99, the url would be https://192.168.1.99:99.
To configure the lockout options:
- Go to System > Admin > Settings.
- Under Administrative Settings, change the port numbers for HTTP, HTTPS, Telnet, and/or SSH as needed. You can also select Redirect to HTTPS in order to avoid HTTP being used for the administrators.
When you change to the default port number for HTTP, HTTPS, Telnet, or SSH, ensure that the port number is unique. If a conflict exists with a particular port, a warning message will appear.
Changing the host name
The host name of your FortiGate unit appears in the Host Name row, in the System Information widget. The host name also appears at the CLI prompt when you are logged in to the CLI and as the SNMP system name.
To change the host name on the FortiGate unit, in the System Information widget, select Change in the Host Name row. The only administrators that can change a FortiGate unit’s host name are administrators whose admin profiles permit system configuration write access. If the FortiGate unit is part of an HA cluster, you should use a unique host name to distinguish the FortiGate unit from others in the cluster.
RAID disk configuration
The RAID disk is configured from the Disk Configuration page.
| RAID level | Select the level of RAID. Options include: • RAID-0 — (striping) better performance, no redundancy • RAID-1 — (mirroring) half the storage capacity, with redundancy • RAID-5 — striping with parity checking, and redundancy Available RAID level options depend on the available number of hard disks. Two or more disks are required for RAID 0 or RAID 1. Three or more disks are required for RAID 5. Changing the RAID level will erase any stored log information on the array, and reboot the FortiGate unit. The FortiGate unit will remain offline while it reconfigures the RAID array. When it reboots, the array will need to synchronize before being fully operational. |
| Status | The status, or health, of RAID array. This status can be one of: • OK — standard status, everything is normal. • OK (Background-Synchronizing) (%) — synchronizing the disks after changing RAID level, Synchronizing progress bar shows percent complete. • Degraded — One or more of the disks in the array has failed, been removed, or is not working properly. A warning is displayed about the lack of redundancy in this state. Also, a degraded array is slower than a healthy array. Select Rebuild RAID to fix the array. • Degraded (Background-Rebuilding) (%) — The same as degraded, but the RAID array is being rebuilt in the background. The array continues to be in a fragile state until the rebuilding is completed. |
| Size | The size of the RAID array in gigabytes (GB). The size of the array depends on the RAID level selected, and the number of disks in the array. |
| Rebuild RAID | Select to rebuild the array after a new disk has been added to the array, or after a disk has been swapped in for a failed disk. If you try to rebuild a RAID array with too few disks you will get a rebuild error. After inserting a functioning disk, the rebuild will start. This button is only available when the RAID array is in a degraded state and has enough disks to be rebuilt. You cannot restart a rebuild once a rebuild is already in progress. Note: If a disk has failed, the number of working disks may not be enough for the RAID level to function. In this case, replace the failed disk with a working disk to rebuild the RAID array. |
| Disk# | The disk’s position in the array. This corresponds to the physical slot of the disk. If a disk is removed from the FortiGate unit, the disk is marked as not a member of the array and its position is retained until a new disk is inserted in that drive bay. |
| Status | The status of this disk. Options include OK, and unavailable. A disk is unavailable if it is removed or has failed. |
Firmware
Fortinet periodically updates the FortiGate firmware to include new features and resolve important issues. After you have registered your FortiGate unit, you can download firmware updates from the support web site, https://support.fortinet.com.
Before you install any new firmware, be sure to follow the steps below:
- Review the Release Notes for a new firmware release.
- Review the Supported Upgrade Paths document to make sure the upgrade from your current image to the desired new image is supported.
- Backup the current configuration, including local certificates. For more information, see Configuration Backups.
- Test the new firmware until you are satisfied that it applies to your configuration.
Installing new firmware without reviewing release notes or testing the firmware may result in changes to settings or unexpected issues.
Only FortiGate admin users and administrators whose access profiles contain system read and write privileges can change the FortiGate firmware.
Backing up the current configuration
In case you need to restore your FortiGate configuration, you should always back up the configuration before installing new firmware.
To create a local backup:
- Go to System > Dashboard > Status and locate the System Information widget.
- Select Backup beside System Configuration.
- Choose either Local PC or USB Disk to save the configuration file.
- If desired, select Encrypt configuration file.
- Select Backup.
Downloading firmware
Firmware images for all FortiGate units is available on the Fortinet Customer Support website, https://support.fortinet.com.
To download firmware
- Log into the site using your user name and password.
- Go to Download > Firmware Images.
- A list of Release Notes is shown. If you have not already done so, download and review the Release Notes for the firmware you wish to upgrade your FortiGate unit to.
- Select HTTPS Download.
|
|
Firmware can also be downloaded using FTP; however, as FTP is not an encrypted file transferring protocol, HTTPS downloading is recommended. |
- Navigate to find the folder for the firmware version you wish to use.
- Select your FortiGate model from the list. If your unit is a FortiWiFi, be sure to get the appropriate firmware, which will have a filename starting with FWF.
- Save the firmware image to your computer.
Testing new firmware before installing
FortiOS enables you to test a new firmware image by installing the firmware image from a system reboot and saving it to system memory. After completing this procedure, the FortiGate unit operates using the new firmware image with the current configuration. This new firmware image is not permanently installed. The next time the FortiGate unit restarts, it operates with the originally installed firmware image using the current configuration. If the new firmware image operates successfully, you can install it permanently using the procedure Upgrading the firmware - web-based manager .
To use this procedure, you must connect to the CLI using the FortiGate console port and a RJ-45 to DB-9 or null modem cable. This procedure temporarily installs a new firmware image using your current configuration.
For this procedure, you must install a TFTP server that you can connect to from the FortiGate internal interface. The TFTP server should be on the same subnet as the internal interface.
To test the new firmware image
- Connect to the CLI using a RJ-45 to DB-9 or null modem cable.
- Make sure the TFTP server is running.
- Copy the new firmware image file to the root directory of the TFTP server.
- Make sure the FortiGate unit can connect to the TFTP server using the
execute pingcommand. - Enter the following command to restart the FortiGate unit:
execute reboot
- As the FortiGate unit reboots, press any key to interrupt the system startup. As the FortiGate unit starts, a series of system startup messages appears.
When the following messages appears:
Press any key to display configuration menu....
- Immediately press any key to interrupt the system startup.
|
|
You have only 3 seconds to press any key. If you do not press a key soon enough, the FortiGate unit reboots and you must login and repeat the execute reboot command. |
If you successfully interrupt the startup process, the following messages appears:
[G]: Get firmware image from TFTP server.
[F]: Format boot device.
[B]: Boot with backup firmware and set as default
[C]: Configuration and information
[Q]: Quit menu and continue to boot with default firmware.
[H]: Display this list of options.
Enter G, F, Q, or H:
- Type G to get the new firmware image from the TFTP server.
The following message appears:
Enter TFTP server address [192.168.1.168]:
- Type the address of the TFTP server and press Enter.
The following message appears:
Enter Local Address [192.168.1.188]:
- Type an IP address of the FortiGate unit to connect to the TFTP server.
The IP address must be on the same network as the TFTP server.
|
|
Make sure you do not enter the IP address of another device on this network. |
The following message appears:
Enter File Name [image.out]:
- Enter the firmware image file name and press Enter.
The TFTP server uploads the firmware image file to the FortiGate unit and the following appears.
Save as Default firmware/Backup firmware/Run image without saving: [D/B/R]
- Type
R.
The FortiGate image is installed to system memory and the FortiGate unit starts running the new firmware image, but with its current configuration.
You can test the new firmware image as required. When done testing, you can reboot the FortiGate unit, and the FortiGate unit will resume using the firmware that was running before you installed the test firmware.
Upgrading the firmware - web-based manager
Installing firmware replaces your current antivirus and attack definitions, along with the definitions included with the firmware release you are installing. After you install new firmware, make sure that antivirus and attack definitions are up to date.
|
|
Always remember to back up your configuration before making any changes to the firmware. |
To upgrade the firmware
- Log into the web-based manager as the admin administrative user.
- Go to System > Dashboard > Status and locate the System Information widget.
- Beside Firmware Version, select Update.
- Type the path and filename of the firmware image file, or select Browse and locate the file.
- Select OK.
The FortiGate unit uploads the firmware image file, upgrades to the new firmware version, restarts, and displays the FortiGate login. This process takes a few minutes.
Upgrading the firmware - CLI
Installing firmware replaces your current antivirus and attack definitions, along with the definitions included with the firmware release you are installing. After you install new firmware, make sure that antivirus and attack definitions are up to date. You can also use the CLI command execute update-now to update the antivirus and attack definitions. For more information, see the System Administration handbook.
Before you begin, ensure you have a TFTP server running and accessible to the FortiGate unit.
|
|
Always remember to back up your configuration before making any changes to the firmware. |
To upgrade the firmware using the CLI
- Make sure the TFTP server is running.
- Copy the new firmware image file to the root directory of the TFTP server.
- Log into the CLI.
- Make sure the FortiGate unit can connect to the TFTP server.
You can use the following command to ping the computer running the TFTP server. For example, if the IP address of the TFTP server is 192.168.1.168:
execute ping 192.168.1.168
- Enter the following command to copy the firmware image from the TFTP server to the FortiGate unit:
execute restore image tftp <filename> <tftp_ipv4>
Where
<name_str>is the name of the firmware image file and<tftp_ip4>is the IP address of the TFTP server. For example, if the firmware image file name isimage.outand the IP address of the TFTP server is 192.168.1.168, enter:
execute restore image tftp image.out 192.168.1.168
The FortiGate unit responds with the message:
This operation will replace the current firmware version!
Do you want to continue? (y/n)
- Type
y. - The FortiGate unit uploads the firmware image file, upgrades to the new firmware version, and restarts. This process takes a few minutes.
- Reconnect to the CLI.
- Update antivirus and attack definitions, by entering:
execute update-now
Installing firmware from a system reboot using the CLI
There is a possibility that the firmware upgrade does not load properly and the FortiGate unit will not boot, or continuously reboots. If this occurs, it is best to perform a fresh install of the firmware from a reboot using the CLI.
This procedure installs a firmware image and resets the FortiGate unit to default settings. You can use this procedure to upgrade to a new firmware version, revert to an older firmware version, or re-install the current firmware.
To use this procedure, you must connect to the CLI using the FortiGate console port and a RJ-45 to DB-9, or null modem cable. This procedure reverts the FortiGate unit to its factory default configuration.
For this procedure you install a TFTP server that you can connect to from the FortiGate internal interface. The TFTP server should be on the same subnet as the internal interface.
Before beginning this procedure, ensure you back up the FortiGate unit configuration.
If you are reverting to a previous FortiOS version, you might not be able to restore the previous configuration from the backup configuration file.
Installing firmware replaces your current antivirus and attack definitions, along with the definitions included with the firmware release you are installing. After you install new firmware, make sure that antivirus and attack definitions are up to date.
To install firmware from a system reboot
- Connect to the CLI using the RJ-45 to DB-9 or null modem cable.
- Make sure the TFTP server is running.
- Copy the new firmware image file to the root directory of the TFTP server.
- Make sure the internal interface is connected to the same network as the TFTP server.
- To confirm the FortiGate unit can connect to the TFTP server, use the following command to ping the computer running the TFTP server. For example, if the IP address of the TFTP server is 192.168.1.168:
execute ping 192.168.1.168
- Enter the following command to restart the FortiGate unit.
execute reboot
The FortiGate unit responds with the following message:
This operation will reboot the system!
Do you want to continue? (y/n)
- Type
y.
As the FortiGate unit starts, a series of system startup messages appears. When the following messages appears:
Press any key to display configuration menu..........
Immediately press any key to interrupt the system startup.
|
|
You have only 3 seconds to press any key. If you do not press a key soon enough, the FortiGate unit reboots and you must log in and repeat the execute reboot command. |
If you successfully interrupt the startup process, the following messages appears:
[G]: Get firmware image from TFTP server.
[F]: Format boot device.
[B]: Boot with backup firmware and set as default
[C]: Configuration and information
[Q]: Quit menu and continue to boot with default firmware.
[H]: Display this list of options.
Enter G, F, Q, or H:
- Type G to get to the new firmware image form the TFTP server.
The following message appears:
Enter TFTP server address [192.168.1.168]:
- Type the address of the TFTP server and press Enter.
The following message appears:
Enter Local Address [192.168.1.188]:
- Type an IP address the FortiGate unit can use to connect to the TFTP server. The IP address can be any IP address that is valid for the network the interface is connected to.
|
|
Make sure you do not enter the IP address of another device on this network. |
The following message appears:
Enter File Name [image.out]:
- Enter the firmware image filename and press Enter.
The TFTP server uploads the firmware image file to the FortiGate unit and a message similar to the following appears:
Save as Default firmware/Backup firmware/Run image without saving: [D/B/R]
- Type
D.
The FortiGate unit installs the new firmware image and restarts. The installation might take a few minutes to complete.
Reverting to a previous firmware version - web-based manager
The following procedures revert the FortiGate unit to its factory default configuration and deletes any configuration settings. If you are reverting to a previous FortiOS version, you might not be able to restore the previous configuration from the backup configuration file.
|
|
Always remember to back up your configuration before making any changes to the firmware. |
To revert to a previous firmware version
- Go to System > Dashboard > Status and locate the System Information widget.
- Beside Firmware Version, select Update.
- Type the path and filename of the firmware image file, or select Browse and locate the file.
- Select OK.
The FortiGate unit uploads the firmware image file, reverts to the old firmware version, resets the configuration, restarts, and displays the FortiGate login. This process takes a few minutes.
Reverting to a previous firmware version - CLI
This procedure reverts the FortiGate unit to its factory default configuration and deletes IPS custom signatures, web content lists, email filtering lists, and changes to replacement messages.
Before beginning this procedure, it is recommended that you:
- back up the FortiGate unit system configuration using the command
execute backup config - back up the IPS custom signatures using the command
execute
backup ipsuserdefsig - back up web content and email filtering lists
To use the following procedure, you must have a TFTP server the FortiGate unit can connect to.
To revert to a previous firmware version using the CLI
- Make sure the TFTP server is running
- Copy the firmware image file to the root directory of the TFTP server.
- Log into the FortiGate CLI.
- Make sure the FortiGate unit can connect to the TFTP server execute by using the
execute pingcommand. - Enter the following command to copy the firmware image from the TFTP server to the FortiGate unit:
execute restore image tftp <name_str> <tftp_ipv4>
Where
<name_str>is the name of the firmware image file and<tftp_ip4>is the IP address of the TFTP server. For example, if the firmware image file name isimagev28.outand the IP address of the TFTP server is 192.168.1.168, enter:
execute restore image tftp image28.out 192.168.1.168
The FortiGate unit responds with this message:
This operation will replace the current firmware version!
Do you want to continue? (y/n)
- Type
y.
The FortiGate unit uploads the firmware image file. After the file uploads, a message similar to the following appears:
Get image from tftp server OK.
Check image OK.
This operation will downgrade the current firmware version!
Do you want to continue? (y/n)
- Type
y. - The FortiGate unit reverts to the old firmware version, resets the configuration to factory defaults, and restarts. This process takes a few minutes.
- Reconnect to the CLI.
- To restore your previous configuration, if needed, use the command:
execute restore config <name_str> <tftp_ip4>
- Update antivirus and attack definitions using the command:
execute update-now.
Restore from a USB key - CLI
To restore configuration using the CLI
- Log into the CLI.
- Enter the following command to restore an unencrypted configuration file:
exec restore image usb <filename>
If your configuration file was encrypted, enter the following command:
execute restore config usb-mode <password>
The FortiGate unit responds with the following message:
This operation will replace the current firmware version!
Do you want to continue? (y/n)
- Type
y.
Configuration revision
The Configuration Revisions menu enables you to manage multiple versions of configuration files on models that have a 512 flash memory and higher. Revision control requires either a configured central management server or the local hard drive. The central management server can either be a FortiManager unit or FortiCloud.
If central management is not configured on your FortiGate unit, a message appears to tell you to do one of the following:
- enable central management
- obtain a valid license.
When revision control is enabled on your FortiGate unit, and configurations backups have been made, a list of saved revisions of those backed-up configurations appears.
Configuration revisions are viewed in the System Information widget on the Dashboard.
Controlled upgrade
Using a controlled upgrade, you can upload a new version of the FortiOS firmware to a separate partition in the FortiGate memory for later upgrade. The FortiGate unit can also be configured so that when it is rebooted, it will automatically load the new firmware (CLI only). Using this option, you can stage a number of FortiGate units to do an upgrade simultaneously to all devices using FortiManager or script.
To load the firmware for later installation - web-based manager
- Go to System > Dashboard > Status.
- Under System Information > Firmware Version, select Update.
- Type the path and filename of the firmware image file, or select Browse and locate the file.
- Deselect the Boot the New Firmware option.
- Select OK.
To load the firmware for later installation - CLI
execute restore secondary-image {ftp | tftp | usb}
To set the FortiGate unit so that when it reboots, the new firmware is loaded, use the CLI command...
execute set-next-reboot {primary | secondary}
... where {primary | secondary} is the partition with the preloaded firmware.
To trigger the upgrade using the web-based manager
- Go to System > Dashboard > Status.
- Under System Information > Firmware Version, select Details.
- Select the check box for the new firmware version.
The Comments column indicates which firmware version is the current active version. - Select Upgrade icon.
FortiGuard
The FortiGuard Distribution Network (FDN) of servers provides updates to antivirus, antispam and IPS definitions to your FortiGate unit. Worldwide coverage of FortiGuard services is provided by FortiGuard service points. FortiGuard Subscription Services provide comprehensive Unified Threat Management (UTM) security solutions to enable protection against content and network level threats.
The FortiGuard team can be found around the globe, monitoring virus, spyware and vulnerability activities. As vulnerabilities are found, signatures are created and pushed to the subscribed FortiGate units. The Global Threat Research Team enables Fortinet to deliver a combination of multi-layered security intelligence and provide true zero-day protection from new and emerging threats.The FortiGuard Network has data centers around the world located in secure, high availability locations that automatically deliver updates to the Fortinet security platforms to and protect the network with the most up-to-date information.
The FortiGuard services provide a number of services to monitor world-wide activity and provide the best possible security:
- Intrusion Prevention System (IPS)- The FortiGuard Intrusion Prevention System (IPS) uses a customizable database of more than 4000 known threats to stop attacks that evade conventional firewall defenses. It also provides behavior-based heuristics, enabling the system to recognize threats when no signature has yet been developed. It also provides more than 1000 application identity signatures for complete application control.
- Application Control - Application Control allows you to identify and control applications on networks and endpoints regardless of port, protocol, and IP address used. It gives you unmatched visibility and control over application traffic, even traffic from unknown applications and sources.
- AntiVirus -The FortiGuard AntiVirus Service provides fully automated updates to ensure protection against the latest content level threats. It employs advanced virus, spyware, and heuristic detection engines to prevent both new and evolving threats from gaining access to your network and protects against vulnerabilities.
- Web Filtering - Web Filtering provides Web URL filtering to block access to harmful, inappropriate, and dangerous web sites that may contain phishing/pharming attacks, malware such as spyware, or objectionable content that can expose your organization to legal liability. Based on automatic research tools and targeted research analysis, real-time updates enable you to apply highly-granular policies that filter web access based on 78 web content categories, over 45 million rated web sites, and more than two billion web pages - all continuously updated.
- Vulnerability Scanning - FortiGuard Services provide comprehensive and continuous updates for vulnerabilities, remediation, patch scan, and configuration benchmarks.
- Email Filtering - The FortiGuard Antispam Service uses both a sender IP reputation database and a spam signature database, along with sophisticated spam filtering tools on Fortinet appliances and agents, to detect and block a wide range of spam messages. Updates to the IP reputation and spam signature databases are provided continuously via the FDN.
- Messaging Services - Messaging Services allow a secure email server to be automatically enabled on your FortiGate unit to send alert email or send email authentication tokens. With the SMS gateway, you can enter phone numbers where the FortiGate unit will send the SMS messages. Note that depending on your carrier, there may be a slight time delay on receiving messages.
- DNS and DDNS - The FortiGuard DNS and DDNS services provide an efficient method of DNS lookups once subscribed to the FortiGuard network. This is the default option. The FortiGate unit connects automatically to the FortiGuard DNS server. If you do not register, you need to configure an alternate DNS server.
Configure the DDNS server settings using the CLI commands:
config system fortiguard
set ddns-server-ip
set ddns-server-port
end
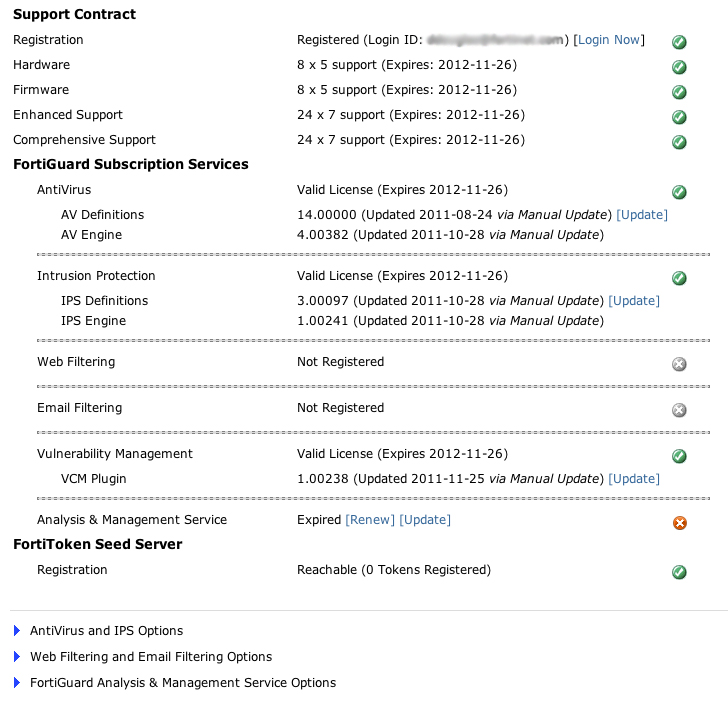
Support Contract and FortiGuard Subscription Services
The Support Contract and FortiGuard Subscription Services sections are displayed in abbreviated form within the License Information widget. A detailed version is available by going to System > Config > FortiGuard.
The Support Contract area displays the availability or status of your FortiGate unit’s support contract. The status displays can be either Unreachable, Not Registered, or Valid Contract.
The FortiGuard Subscription Services area displays detailed information about your FortiGate unit’s support contract and FortiGuard subscription services. On this page, you can also manually update the antivirus and IPS engines.
The status icons for each section Indicates the state of the subscription service. The icon corresponds to the availability description.
- Gray (Unreachable) – the FortiGate unit is not able to connect to service.
- Orange (Not Registered) – the FortiGate unit can connect, but not subscribed.
- Yellow (Expired) – the FortiGate unit had a valid license that has expired.
- Green (Valid license) – the FortiGate unit can connect to FDN and has a registered support contract. If the Status icon is green, the expiry date also appears.
Verifying your Connection to FortiGuard
If you are not getting FortiGuard web filtering or antispam services, there are a few things to verify communication to the FortiGuard Distribution Network (FDN) is working. Before any troubleshooting, ensure that the FortiGate unit has been registered and you or your company, has subscribed to the FortiGuard services.
Verification - web-based manager
The simplest method to check that the FortiGate unit is communicating with the FDN, is to check the License Information dashboard widget. Any subscribed services should have a green check mark beside them indicating that connections are successful. Any other icon indicates a problem with the connection, or you are not subscribed to the FortiGuard services.
License Information widget showing FortiGuard availability
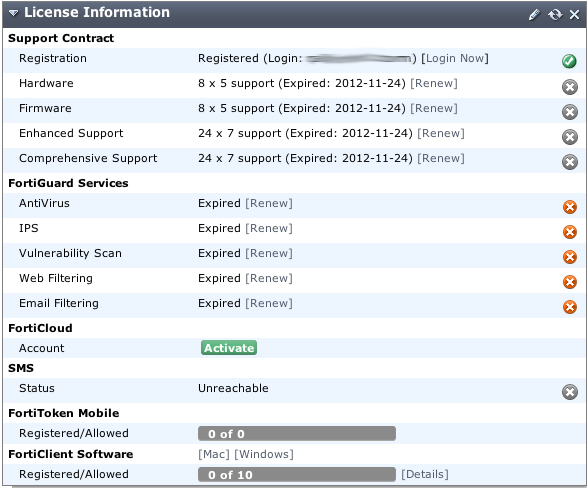
You can also view the FortiGuard connection status by going to System > Config > FortiGuard.
FortiGuard availability
Verification - CLI
You can also use the CLI to see what FortiGuard servers are available to your FortiGate unit. Use the following CLI command to ping the FDN for a connection:
ping guard.fortinet.net
You can also use diagnose command to find out what FortiGuard servers are available:
diagnose debug rating
From this command, you will see output similar to the following:
Locale : english
License : Contract
Expiration : Sun Jul 24 20:00:00 2011
Hostname : service.fortiguard.net
-=- Server List (Tue Nov 2 11:12:28 2010) -=-
IP Weight RTT Flags TZ Packets Curr Lost Total Lost
69.20.236.180 0 10 -5 77200 0 42
69.20.236.179 0 12 -5 52514 0 34
66.117.56.42 0 32 -5 34390 0 62
80.85.69.38 50 164 0 34430 0 11763
208.91.112.194 81 223 D -8 42530 0 8129
216.156.209.26 286 241 DI -8 55602 0 21555
An extensive list of servers are available. Should you see a list of three to five available servers, the FortiGuard servers are responding to DNS replies to service.FortiGuard.net, but the INIT requests are not reaching FDS services on the servers.
The rating flags indicate the server status:
| D | Indicates the server was found via the DNS lookup of the hostname. If the hostname returns more than one IP address, all of them will be flagged with 'D' and will be used first for INIT requests before falling back to the other servers. |
| I | Indicates the server to which the last INIT request was sent |
| F | The server has not responded to requests and is considered to have failed. |
| T | The server is currently being timed. |
The server list is sorted first by weight and then the server with the smallest RTT is put at the top of the list, regardless of weight. When a packet is lost, it will be resent to the next server in the list.
The weight for each server increases with failed packets and decreases with successful packets. To lower the possibility of using a faraway server, the weight is not allowed to dip below a base weight, which is calculated as the difference in hours between the FortiGate unit and the server multiplied by 10. The further away the server is, the higher its base weight and the lower in the list it will appear.
Port assignment
FortiGate units contact the FortiGuard Distribution Network (FDN) for the latest list of FDN servers by sending UDP packets with typical source ports of 1027 or 1031, and destination ports of 53 or 8888. The FDN reply packets have a destination port of 1027 or 1031.
If your ISP blocks UDP packets in this port range, the FortiGate unit cannot receive the FDN reply packets. As a result, the FortiGate unit will not receive the complete FDN server list.
If your ISP blocks the lower range of UDP ports (around 1024), you can configure your FortiGate unit to use higher-numbered ports, using the CLI command…
config system global
set ip-src-port-range <start port>-<end port>
end
…where the <start port> and <end port> are numbers ranging of 1024 to 25000.
For example, you could configure the FortiGate unit to not use ports lower than 2048 or ports higher than the following range:
config system global
set ip-src-port-range 2048-20000
end
Trial and error may be required to select the best source port range. You can also contact your ISP to determine the best range to use. Push updates might be unavailable if:
- there is a NAT device installed between the unit and the FDN
- your unit connects to the Internet using a proxy server.
FortiCloud is a hosted security management and log retention service for FortiGate products. It gives you a centralized reporting, traffic analysis, configuration and log retention without the need for additional hardware and software.
Configuring Antivirus and IPS Options
Go to System > Config > FortiGuard, and expand the AV and IPS Options section to configure the antivirus and IPS options for connecting and downloading definition files.
| Use override server address | Select to configure an override server if you cannot connect to the FDN or if your organization provides updates using their own FortiGuard server. |
| Allow Push Update | Select to allow updates sent automatically to your FortiGate unit when they are available |
| Allow Push Update status icon | The status of the FortiGate unit for receiving push updates: • Gray (Unreachable) - the FortiGate unit is not able to connect to push update service • Yellow (Not Available) - the push update service is not available with your current support license • Green (Available) - the push update service is allowed. |
| Use override push IP and Port | Available only if both Use override server address and Allow Push Update are enabled. Enter the IP address and port of the NAT device in front of your FortiGate unit. FDS will connect to this device when attempting to reach the FortiGate unit. The NAT device must be configured to forward the FDS traffic to the FortiGate unit on UDP port 9443. |
| Schedule Updates | Select this check box to enable updates to be sent to your FortiGate unit at a specific time. For example, to minimize traffic lag times, you can schedule the update to occur on weekends or after work hours. Note that a schedule of once a week means any urgent updates will not be pushed until the scheduled time. However, if there is an urgent update required, select the Update Now button. |
| Update Now | Select to manually initiate an FDN update. |
| Submit attack characteristics… (recommended) |
Select to help Fortinet maintain and improve IPS signatures. The information sent to the FortiGuard servers when an attack occurs and can be used to keep the database current as variants of attacks evolve. |
Manual updates
To manually update the signature definitions file, you need to first go to the Support web site at https://support.fortinet.com. Once logged in, select FortiGuard Service Updates from the Download area of the web page. The browser will present you the most current antivirus and IPS signature definitions which you can download.
Once downloaded to your computer, log into the FortiGate unit to load the definition file.
To load the definition file onto the FortiGate unit
- Go to System > Config > FortiGuard.
- Select the Update link for either AV Definitions or IPS Definitions.
- Locate the downloaded file and select OK.
The upload may take a few minutes to complete.
Automatic updates
The FortiGate unit can be configured to request updates from the FortiGuard Distribution Network. You can configure this to be on a scheduled basis, or with push notifications.
Scheduling updates
Scheduling updates ensures that the virus and IPS definitions are downloaded to your FortiGate unit on a regular basis, ensuring that you do not forget to check for the definition files yourself. As well, by scheduling updates during off-peak hours, such as evenings or weekends, when network usage is minimal, ensures that the network activity will not suffer from the added traffic of downloading the definition files.
If you require the most up-to-date definitions as viruses and intrusions are found in the wild, the FortiGuard Distribution Network can push updates to the FortiGate units as they are developed. This ensures that your network will be protected from any breakouts of a virus within the shortest amount of time, minimizing any damaging effect that can occur. Push updates require that you have registered your FortiGate unit.
Once push updates are enabled, the next time new antivirus or IPS attack definitions are released, the FDN notifies all the FortiGate unit that a new update is available. Within 60 seconds of receiving a push notification, the unit automatically requests the update from the FortiGuard servers.
To enable scheduled updates - web-based manager
- Go to System > Config > FortiGuard.
- Click the Expand Arrow for AV and IPS Options.
- Select the Scheduled Update check box.
- Select the frequency of the updates and when within that frequency.
- Select Apply.
To enable scheduled updates - CLI
config system autoupdate schedule
set status enable
set frequency {every | daily | weekly}
set time <hh:mm>
set day <day_of_week>
end
Push updates
Push updates enable you to get immediate updates when new virus or intrusions have been discovered and new signatures are created. This ensures that when the latest signature is available it will be sent to the FortiGate.
When a push notification occurs, the FortiGuard server sends a notice to the FortiGate unit that there is a new signature definition file available. The FortiGate unit then initiates a download of the definition file, similar to the scheduled update.
To ensure maximum security for your network, you should have a scheduled update as well as enable the push update, in case an urgent signature is created, and your cycle of the updates only occurs weekly.
To enable push updates - web-based manager
- Go to System > Config > FortiGuard.
- Click the Expand Arrow for AV and IPS Options.
- Select Allow Push Update.
- Select Apply.
To enable push updates - CLI
config system autoupdate push-update
set status enable
end
Push IP override
If the FortiGate unit is behind another NAT device (or another FortiGate unit), to ensure it receives the push update notifications, you need to use an override IP address for the notifications. To do this, you create a virtual IP to map to the external port of the NAT device.
Generally speaking, if there are two FortiGate devices as in the diagram below, the following steps need to be completed on the FortiGate NAT device to ensure the FortiGate unit on the internal network receives the updates:
- Add a port forwarding virtual IP to the FortiGate NAT device that connects to the Internet by going to Firewall Objects > Virtual IP.
- Add a security policy to the FortiGate NAT device that connects to the Internet that includes the port forwarding virtual IP.
- Configure the FortiGate unit on the internal network with an override push IP and port.
On the FortiGate internal device, the virtual IP is entered as the Use push override IP address.
To enable push update override- web-based manager
- Go to System > Config > FortiGuard.
- Click the Expand Arrow for AV and IPS Options.
- Select Allow Push Update.
- Select Use push override IP.
- Enter the virtual IP address configured on the NAT device.
- Select Apply.
To enable push updates - CLI
config system autoupdate push-update
set status enable
set override enable
set address <vip_address>
end
Configuring Web Filtering and Email Filtering Options
Go to System > Config > FortiGuard, and expand arrow to view Web Filtering and Email Filtering Options for setting the size of the caches and ports used.
| Web Filter cache TTL | Set the Time To Live value. This is the number of seconds the FortiGate unit will store a blocked IP or URL locally, saving time and network access traffic, checking the FortiGuard server. Once the TTL has expired, the FortiGate unit will contact an FDN server to verify a web address. The TTL must be between 300 and 86400 seconds. |
| Antispam cache TTL | Set the Time To Live value. This is the number of seconds the FortiGate unit will store a blocked IP or URL locally, saving time and network access traffic, checking the FortiGuard server. Once the TTL has expired, the FortiGate unit will contact an FDN server to verify a web address. The TTL must be between 300 and 86400 seconds. |
| Port Section | Select the port assignments for contacting the FortiGuard servers. Select the Test Availability button to verify the connection using the selected port. |
| To have a URL's category rating re-evaluated, please click here | Select to re-evaluate a URL’s category rating on the FortiGuard Web Filter service. |
Email filtering
The FortiGuard data centers monitor and update email databases of known spam sources. With FortiGuard Antispam enabled, the FortiGate unit verifies incoming email sender address and IPs against the database, and take the necessary action as defined within the antivirus profiles.
Spam source IP addresses can also be cached locally on the FortiGate unit, providing a quicker response time, while easing load on the FortiGuard servers, aiding in a quicker response time for less common email address requests.
By default, the antispam cache is enabled. The cache includes a time-to-live value, which is the amount of time an email address will stay in the cache before expiring. You can change this value to shorten or extend the time between 300 and 86400 seconds.
To modify the antispam filter cache size - web-based manager
- Go to System > Config > FortiGuard.
- Click the Expand Arrow for Web Filtering and Email Filtering Options.
- Enter the TTL value for the antispam cache.
- Select Apply.
To modify the web filter cache size - CLI
config system fortiguard
set antispam-cache-ttl <integer>
end
Further antispam filtering options can be configured to block, allow or quarantine, specific email addresses. These configurations are available through the Security Profiles > Antispam menu. For more information, see the Security Profiles handbookchapter.
Online Security Tools
The FortiGuard online center provides a number of online security tools that enable you to verify or check ratings of web sites, email addresses as well as check file for viruses:
- URL lookup - By entering a web site address, you can see if it has been rated and what category and classification it is filed as. If you find your web site or a site you commonly go to has been wrongly categorized, you can use this page to request that the site be re-evaluated.
https://www.fortiguard.com/webfiltering/webfiltering.html - IP and signature lookup - The IP and signature lookup enables you to check whether an IP address is blacklisted in the FortiGuard IP reputation database or whether a URL or email address is in the signature database.
https://www.fortiguard.com/antispam/antispam.html - Online virus scanner - If you discover a suspicious file on your machine, or suspect that a program you downloaded from the Internet might be malicious you can scan it using the FortiGuard online scanner. The questionable file can be uploaded from your computer to a dedicated server where it will be scanned using FortiClient Antivirus. Only one file of up to 1 MB can be checked at any one time. All files will be forwarded to our research labs for analysis.
https://www.fortiguard.com/antivirus/virus_scanner.html - Malware removal tools - Tools have been developed by FortiGuard Labs to disable and remove the specific malware and related variants. Some tools have been developed to remove specific malware, often tough to remove. A universal cleaning tool, FortiCleanup, is also available for download.
The FortiCleanup is a tool developed to identify and cleanse systems of malicious rootkit files and their associated malware. Rootkits consist of code installed on a system with kernel level privileges, often used to hide malicious files, keylog and thwart detection / security techniques. The aim of this tool is to reduce the effectiveness of such malware by finding and eliminating rootkits. The tool offers a quick memory scan as well as a full system scan. FortiCleanup will not only remove malicious files, but also can cleanse registry entries, kernel module patches, and other tricks commonly used by rootkits - such as SSDT hooks and process enumeration hiding.
A license to use these applications is provided free of charge, courtesy of Fortinet.
https://www.fortiguard.com/antivirus/malware_removal.html
FortiCloud
FortiCloud (formerly known as FAMS) is a hosted security management and log retention service for FortiGate devices. It gives you centralized reporting, traffic analysis, configuration management and log retention without the need for additional hardware and software.
|
|
FortiGate models 800 and above do not support the FortiCloud service. |
FortiCloud offers a wide range of features:
- Simplified central management - FortiCloud provides a central web-based management console to manage individual or aggregated FortiGate and FortiWiFi devices. Adding a device to the FortiCloud management subscription is straightforward and provides detailed traffic and application visibility across the whole network.
- Hosted log retention with large default storage allocated - Log retention is an integral part of any security and compliance program but administering a separate storage system is burdensome. FortiCloud takes care of this automatically and stores the valuable log information in the cloud. Each device is allowed up to 200Gb of log retention storage. Different types of logs can be stored including Traffic, System Events, Web, Applications and Security Events.
- Monitoring and alerting in real time - Network availability is critical to a good end-user experience. FortiCloud enables you to monitor your FortiGate network in real time with different alerting mechanisms to pinpoint potential issues. Alerting mechanisms can be delivered via email.
- Customized or pre-configured reporting and analysis tools - Reporting and analysis are your eyes and ears into your network’s health and security. Pre-configured reports are available, as well as custom reports that can be tailored to your specific reporting and compliance requirements. For example, you may want to look closely at application usage or web site violations. The reports can be emailed as PDFs and can cover different time periods.
- Maintain important configuration information uniformly - The correct configuration of the devices within your network is essential to maintaining an optimum performance and security posture. In addition, maintaining the correct firmware (operating system) level allows you to take advantage of the latest features.
- Service security - All communication (including log information) between the devices and the clouds is encrypted. Redundant data centers are always used to give the service high availability. Operational security measures have been put in place to make sure your data is secure — only you can view or retrieve it.
Registration and Activation
|
|
Before you can activate a FortiCloud account, you must first register your device. |
FortiCloud accounts can be registered manually through the FortiCloud website, https://www.forticloud.com, but you can easily register and activate your account directly within your FortiGate unit. Your registration process will vary somewhat, depending on which firmware version and device you have.
FortiGate models 300 and below, all FortiWiFi units
- On your device’s dashboard, in the License Information widget, select the green Activate button in the FortiCloud section.
- A dialogue asking you to register your FortiCloud account will appear. Enter your information, view and accept the Terms and Conditions and select Create Account.
- A second dialogue window will appear, asking you to enter your information to confirm your account. This will send a confirmation email to your registered email. The dashboard widget will update to show that confirmation is required.
- Open your email, and follow the confirmation link contained in it.
A FortiCloud page will open, stating that your account has been confirmed. The Activation Pending message on the dashboard will change to state the type of account you have (‘1Gb Free’ or ‘200Gb Subscription’), and will now provide a link to the FortiCloud portal.
FortiGate models 600 to 800
For 600 through 800, FortiCloud registration must be done through the FortiGate CLI Console.
Enabling logging to FortiCloud
- Go to Log & Report > Log Config > Log Settings.
- Enable Send Logs to FortiCloud.
- Select Test Connectivity to ensure that your FortiGate can connect to the registered FortiCloud account.
Logging into the FortiCloud portal
Once logging has been configured and you have registered your account, you can log into the FortiCloud portal and begin viewing your logging results. There are two methods to reach the FortiCloud portal:
- If you have direct networked access to the FortiGate unit, you can simply open your Dashboard and check the License Information widget. Next to the current FortiCloud connection status will be a link to reach the FortiCloud Portal.
- If you do not currently have access to the FortiGate’s interface, you can visit the FortiCloud website (https://forticloud.com) and log in remotely, using your email and password. It will ask you to confirm the FortiCloud account you are connecting to and then you will be granted access. Connected devices can be remotely configured using the Scripts page in the Management Tab, useful if an administrator may be away from the unit for a long period of time.
Upgrading to a 200Gb subscription
Upgrading your subscription is simple but must be done through the FortiGate unit, as the storage contract is allocated based on devices rather than user accounts.
- Open the FortiGate Dashboard.
- In the License Information widget, select Upgrade next to ‘Type’ in the FortiCloud section.
- A new window will open, showing the Fortinet Support portal. Follow the on-screen instructions to register your contract.
- Wait approximately 10 minutes for the contract to be applied and then visit your Dashboard.
In the License Information widget, Type will have changed from ‘Free’ to ‘Subscribed’. Your maximum listed storage will also have updated.
Cloud Sandboxing
FortiCloud can be used for automated sample tracking, or sandboxing, for files from a FortiGate unit. This allows suspicious files to be sent to be inspected without risking network security. If the file exhibits risky behavior, or is found to contain a virus, a new virus signature is created and added to the FortiGuard antivirus signature database. This feature was formerly known as FortiGuard Analytics.
Cloud sandboxing is configured by going to System > Config > FortiSandbox. After enabling FortiSandbox, select Cloud Sandbox (FortiCloud).
Sandboxing results will be shown in a new tab called AV Submissions in the FortiCloud portal. This tab will only appear after a file has been sent for sandboxing.
Administrators
By default, the FortiGate unit has a super administrator called “admin”. This user login cannot be deleted and always has ultimate access over the FortiGate unit. Additional administrators can be added for various functions, each with a unique username, password, and set of access privileges.
There are two levels of administrator accounts; regular administrators and system administrators. Regular administrators are administrators with any admin profile other than the default super_admin. System administrators are administrators that are assigned the super_admin profile, which has the highest level of access.
Adding administrators
|
|
The name of the administrator should not contain the characters <>()#"'. Using these characters in the administrator account name can result in a cross site scripting (XSS) vulnerability. |
Only the default ”admin” account or an administrator with read-write access control to add new administrator accounts and control their permission levels can create a new administrator account. If you log in with an administrator account that does not have the super_admin admin profile, the administrators list will show only the administrators for the current virtual domain.
When adding administrators, you are setting up the administrator’s user account. An administrator account comprises of an administrator’s basic settings as well as their access profile. The access profile is a definition of what the administrator is capable of viewing and editing.
To add an administrator - web-based manager
- Go to System > Admin > Administrators.
- Select Create New.
- Enter the administrator name.
- Select the type of account it will be. If you select Remote, the FortiGate unit can reference a RADIUS, LDAP or TACAS+ server.
- When selecting Remote or PKI accounts, select the User Group the account will access.
For information on logging in using remote authentication servers, see the User Authentication Guide. For an example of setting up a user with LDAP, see LDAP Admin Access and Authorization - Enter the password for the user.
This may be a temporary password that the administrator can change later. Passwords can be up to 256 characters in length. For more information on passwords, see Passwords. - Select OK.
To add an administrator - CLI
config system admin
edit <admin_name>
set password <password>
set accprofile <profile_name>
end
LDAP Admin Access and Authorization
You can use the LDAP server as a means to add administrative users, saving the time to add users to the FortiGate unit administrator list. After configuring, any user within the selected LDAP group server can automatically log into the FortiGate unit as an adm i st rat or. Ensure that the admin profile is the correct level of access, or the users within the LDAP group are the only ones authorized to configure or modify the configuration of the FortiGate unit.
To do this, requires three steps:
- configure the LDAP server
- add the LDAP server to a user group
- configure the administrator account
Configure the LDAP server
First set up the LDAP server as you normally would, and include a group to bind to.
To configure the LDAP server - web-based manager
- Go to User & Device > Remote > LDAP and select Create New.
- Enter a Name for the server.
- Enter the Server IP address or name.
- Enter the Common Name Identifier and Distinguished Name.
- Set the Bind Type to Regular and enter the User DN and Password.
- Select OK.
To configure the LDAP server - CLI
config user ldap
edit <ldap_server_name>
set server <server_ip>
set cnid cn
set dn DC=XYZ,DC=COM
set type regular
set username CN=Administrator,CN=Users,DC=XYZ,DC=COM
set password <password>
set member-attr <group_binding>
end
Add the LDAP server to a user group
Next, create a user group that will include the LDAP server that was created above.
To create a user group - web-based manager
- Go to User & Device > User Group > User Group and select Create New.
- Enter a Name for the group.
- In the section labelled Remote authentication servers, select Add.
- Select the Remote Server from the drop-down list.
- Select OK.
To create a user group - CLI
config user group
edit <group_name>
config match
edit 1
set server-name <LDAP_server>
set group-name <group_name>
end
end
Configure the administrator account
Now you can create a new administrator, where rather than entering a password, you will use the new user group and the wildcard option for authentication.
To create an administrator - web-based manager
- Go to System > Admin > Administrators and select Create New.
- In the Administrator field, enter the name for the administrator.
- For Type, select Remote.
- Select the User Group created above from the drop-down list.
- Select Wildcard.
- The Wildcard option allows for LDAP users to connect as this administrator.
- Select an Admin Profile.
- Select OK.
To create an administrator - CLI
config system admin
edit <admin_name>
set remote-auth enable
set accprofile super_admin
set wildcard enable
set remote-group ldap
end
Monitoring administrators
You can view the administrators logged in using the System Information widget on the Dashboard. On the widget is the Current Administrator row that shows the administrator logged in and the total logged in. Selecting Details displays the administrators), where they are logging in from and how (CLI, web-based manager) and when they logged in.
You are also able to monitor the activities the administrators perform on the FortiGate unit using the logging of events. Event logs include a number of options to track configuration changes.
To set logging - web-based manager
- Go to Log & Report > Log Config > Log Settings.
- Under Event Logging, ensure System activity event is selected.
- Select Apply.
To set logging - CLI
config log eventfilter
set event enable
set system enable
end
To view the logs go to Log & Report > Event Log.
Administrator profiles
Administer profiles define what the administrator user can do when logged into the FortiGate unit. When you set up an administrator user account, you also assign an administrator profile, which dictates what the administrator user will see. Depending on the nature of the administrator’s work, access level or seniority, you can allow them to view and configure as much, or as little, as required.
super_admin profile
The super_admin administrator is the administrative account that the primary administrator should have to log into the FortiGate unit. The profile can not be deleted or modified to ensure there is always a method to administer the FortiGate unit.This user profile has access to all components of FortiOS, including the ability to add and remove other system administrators. For some administrative functions, such as backing up and restoring the configuration using SCP, super_admin access is required.
Creating profiles
To configure administrator profiles go to System > Admin > Admin Profiles. You can only assign one profile to an administrator user.
On the New Admin Profile page, you define the components of FortiOS that will be available to view and/or edit. For example, if you configure a profile so that the administrator can only access the firewall components, when an administrator with that profile logs into the FortiGate unit, they will only be able to view and edit any firewall components including policies, addresses, schedules and any other settings that directly affect security policies.
The view of an administrator with firewall-only access
Global and vdom profiles
By default, when you add a new administrative profile, it is set to have a vdom scope. That is, only the super_admin has a global profile that enables configuration of the entire FortiGate unit.
There may be instances where additional global administrative profiles may be required. To add more global profiles, use the following CLI command to set or change an administrative profile to be global.
config system accprofile
set scope global
...
end
Once the scope is set, you can enable the read and read/write settings.
Regular (password) authentication for administrators
You can use a password stored on the local FortiGate unit to authenticate an administrator. When you select Regular for Type, you will see Local as the entry in the Type column when you view the list of administrators.
Management access
Management access defines how administrators are able to log on to the FortiGate unit to perform management tasks such as configuration and maintenance. Methods of access can include local access through the console connection or remote access over a network or modem interface using various protocols including Telnet and HTTPS.
You can configure management access on any interface in your VDOM. In NAT mode, the interface IP address is used for management access. In transparent mode, you configure a single management IP address that applies to all interfaces in your VDOM that permit management access. The FortiGate unit also uses this IP address to connect to the FDN for virus and attack updates.
The system administrator (admin) can access all VDOMs, and create regular administrator accounts. A regular administrator account can access only the VDOM to which it belongs and the management computer must connect to an interface in that VDOM. In both cases, the management computer must connect to an interface that permits management access and its IP address must be on the same network. Management access can be via HTTP, HTTPS, Telnet, or SSH sessions, if those services are enabled on the interface. HTTPS and SSH are preferred as they are more secure.
You can allow remote administration of the FortiGate unit. However, allowing remote administration from the Internet could compromise the security of the FortiGate unit. You should avoid this unless it is required for your configuration. The following precautions can be taken to improve the security of a FortiGate unit that allows remote administration from the Internet:
- Use secure administrative user passwords.
- Change these passwords regularly.
- Enable two-factor authentication for administrators.
- Enable secure administrative access to this interface using only HTTPS or SSH.
- Use Trusted Hosts to limit where the remote access can originate from.
- Do not change the system idle timeout from the default value of 5 minutes.
Security Precautions
One potential point of a security breach is at the management computer. Administrators who leave their workstations for a prolonged amount of time while staying logged into the web-based manager or CLI leave the firewall open to malicious intent.
Preventing unwanted login attempts
Setting trusted hosts for an administrator limits what computers an administrator can log in from, causing the FortiGate unit to only accept the administrator’s login from the configured IP address. Any attempt to log in with the same credentials from any other IP address will be dropped.
Trusted hosts are configured when adding a new administrator by going to System > Admin > Administrators in the web-based manager or config system admin in the CLI.
To ensure the administrator has access from different locations, you can enter up to ten IP addresses, though ideally this should be kept to a minimum. For higher security, use an IP address with a net mask of 255.255.255.255, and enter an IP address (non-zero) in each of the three default trusted host fields. Also ensure all entries contain actual IP addresses, not the default 0.0.0.0.
The trusted hosts apply to the web-based manager, ping, SNMP, and the CLI when accessed through Telnet or SSH. CLI access through the console port is not affected.
Prevent multiple admin sessions
Multiple admin sessions can occur when multiple users access the FortiGate using the same admin account. By default, the FortiGate unit enables multiple logins of administrators using the same login credentials from different locations. To control admin log ins, and minimize the potential of configuration collisions, you can disable concurrent admin sessions. When disabled, only one user can use the admin account at a time. When a second admin attempts to connect, connection is denied with a message that the login attempt failed.
To disable concurrent admin sessions, enter the following command in the CLI:
config system global
set admin-concurrent disable
end
On 2U FortiGate units, this option is also available in the Web-Based Manager by going to System > Admin > Settings and select Allow each admin to log in with multiple sessions.
Segregated administrative roles
To minimize the effect of an administrator causing errors to the FortiGate configuration and possibly jeopardizing the network, create individual administrative roles where none of the administrators have super-admin permissions. For example, one admin account is used solely to create security policies, another for users and groups, another for VPN, and so on.
Disable admin services
On untrusted networks, turn off the weak administrative services such as Telnet and HTTP. With these services, passwords are passed in the clear, not encrypted. These services can be disabled by going to System > Network > Interface and unselecting the required check boxes.
SSH login time out
When logging into the console using SSH, the default time of inactivity is 120 seconds (2 minutes) to successfully log into the FortiGate unit. To enhance security, you can configure the time to be shorter. Using the CLI, you can change the length of time the command prompt remains idle before the FortiGate unit will log the administrator out. The range can be between 10 and 3600 seconds.
To set the logout time enter the following commands:
config system global
set admin-ssh-grace-time <number_of_seconds>
end
Idle time-out
To avoid the possibility of an administrator walking away from the management computer and leaving it exposed to unauthorized personnel, you can add an idle time-out that will automatically log the user out if the web-based manager is not used for a specified amount of time. This will cause the administrator to log in to the device again in order to continue their work.
The time-out can be set as high as 480 minutes, or eight hours, although this is not recommend.
To set the idle time out - web-based manager
- Go to System > Admin > Settings.
- In the Administration Settings, enter the amount of time the Administrator login can remain idol in the Idle Timeout field.
- Select Apply.
To set the idle time out - CLI
config system global
set admintimeout <minutes>
end
HTTPS redirect
When selecting port numbers for various protocols, you can also enable or disable the Redirect to HTTPS option. When enabled, if you select the Administrative Access for an interface to be only HTTP, HTTPS will automatically be enabled, allowing the administrator access with either HTTP or HTTPS. The administrator can then log in using HTTPS for better security.
Note that if an SSL VPN is also configured for the same port, the SSL connection is over the HTTPS protocol. In these situations, the FortiGate unit will not redirect an HTTP address to the SSL VPN HTTPS address. Ideally, the administrator should not have the management address and an SSL VPN portal on the same interface.
Log in/out warning message
For administrators logging in and out of the FortiGate unit, you can include a login disclaimer. This disclaimer provides a statement that must be accepted or declined where corporations are governed by strict usage policies for forensics and legal reasons.
The disclaimer is enabled through the CLI.
To disable an interface:
config system global
set pre-login-banner enable
set post-login-banner enable
end
When set, once the administrator enters their user name and password, the disclaimer appears. They must select either Accept or Decline to proceed. When the post login is enabled, once the administrator logs out they are presented with the same message.
The banner is a default message that you can customize by going to System > Config > Replacement Messages. Select Extended View to see the Admin category and messages.
Disable the console interface
To prevent any unwanted login attempts using the COM communication port, you can disable login connections to the FortiGate unit.
This command is specifically for the COM port. You can still use FortiExplorer to connect and configure the FortiGate unit if required.
To disable an interface:
config system console
set login disable
end
Disable interfaces
If any of the interfaces on the FortiGate unit are not being used, disable traffic on that interface. This avoids someone plugging in network cables and potentially causing network bypass or loop issues.
To disable an interface - web-based manager
- Go to System > Network > Interface.
- Select the interface from the list and select Edit.
- For Administrative Access, select Down.
- Select OK.
To disable an interface - CLI
config system interface
edit <inerface_name>
set status down
end
RADIUS authentication for administrators
Remote Authentication and Dial-in User Service (RADIUS) servers provide authentication, authorization, and accounting functions. FortiGate units use the authentication and authorization functions of the RADIUS server. To use the RADIUS server for authentication, you must configure the server before configuring the FortiGate users or user groups that will need it.
If you have configured RADIUS support and a user is required to authenticate using a RADIUS server, the FortiGate unit sends the user’s credentials to the RADIUS server for authentication. If the RADIUS server can authenticate the user, the user is successfully authenticated with the FortiGate unit. If the RADIUS server cannot authenticate the user, the FortiGate unit refuses the connection.
If you want to use a RADIUS server to authenticate administrators in your VDOM, you must configure the authentication before you create the administrator accounts. To do this you need to:
- configure the FortiGate unit to access the RADIUS server
- create the RADIUS user group
- configure an administrator to authenticate with a RADIUS server.
Configuring LDAP authentication for administrators
Lightweight Directory Access Protocol (LDAP) is an Internet protocol used to maintain authentication data that may include departments, people, groups of people, passwords, email addresses, printers, etc.
If you have configured LDAP support and an administrator is required to authenticate using an LDAP server, the FortiGate unit contacts the LDAP server for authentication. If the LDAP server cannot authenticate the administrator, the FortiGate unit refuses the connection.
If you want to use an LDAP server to authenticate administrators in your VDOM, you must configure the authentication before you create the administrator accounts. To do this you need to:
- configure an LDAP server
- create an LDAP user group
- configure an administrator to authenticate with an LDAP server.
To view the LDAP server list, go to User & Device > Remote > LDAP.
For more information, see LDAP Admin Access and Authorization .
TACACS+ authentication for administrators
Terminal Access Controller Access-Control System (TACACS+) is a remote authentication protocol that provides access control for routers, network access servers, and other network computing devices via one or more centralized servers.
If you have configured TACACS+ support and an administrator is required to authenticate using a TACACS+ server, the FortiGate unit contacts the TACACS+ server for authentication. If the TACACS+ server cannot authenticate the administrator, the connection is refused by the FortiGate unit.
If you want to use an TACACS+ server to authenticate administrators in your VDOM, you must configure the authentication before you create the administrator accounts. To do this you need to:
- configure the FortiGate unit to access the TACACS+ server
- create a TACACS+ user group
- configure an administrator to authenticate with a TACACS+ server.
PKI certificate authentication for administrators
Public Key Infrastructure (PKI) authentication uses a certificate authentication library that takes a list of peers, peer groups, and user groups and returns authentication successful or denied notifications. Users only need a valid certificate for successful authentication; no username or password is necessary.
To use PKI authentication for an administrator, you must configure the authentication before you create the administrator accounts. To do this you need to:
- configure a PKI user
- create a PKI user group
- configure an administrator to authenticate with a PKI certificate.
Passwords
Using secure admin passwords are vital for preventing unauthorized access to your FortiGate unit. When changing the password, consider the following to ensure better security:
- Do not make passwords that are obvious, such as the company name, administrator names, or other obvious word or phrase.
- Use numbers in place of letters, for example,
passw0rd. Alternatively, spell words with extra letters, for example, password. - Administrative passwords can be up to 64 characters.
- Include a mixture of letters, numbers, and upper and lower case.
- Use multiple words together, or possibly even a sentence, for example keytothehighway.
- Use a password generator.
- Change the password regularly and always make the new password unique and not a variation of the existing password, such as changing from
passwordtopassword1. - Write the password down and store it in a safe place away from the management computer, in case you forget it or ensure that at least two people know the password in the event that one person becomes ill, is away on vacation or leaves the company. Alternatively, have two different admin logins.
Password policy
The FortiGate unit includes the ability to enforce a password policy for administrator login. With this policy, you can enforce regular changes and specific criteria for a password including:
- minimum length between 8 and 64 characters.
- if the password must contain uppercase (A, B, C) and/or lowercase (a, b, c) characters.
- if the password must contain numbers (1, 2, 3).
- if the password must contain non-alphanumeric characters (!, @, #, $, %, ^, &, *, ().
- where the password applies (admin or IPsec or both).
- the duration of the password before a new one must be specified.
To apply a password policy - web-based manager
- Go to System > Admin > Settings.
- Select Enable Password Policy and configure the settings as required.
To apply a password policy - CLI
config system password-policy
set status enable
Configure the other settings as required.
If you add a password policy or change the requirements on an existing policy, the next time that administrator logs into the FortiGate unit, they are prompted to update their password to meet the new requirements before proceeding to log in.
Password policy dialog box
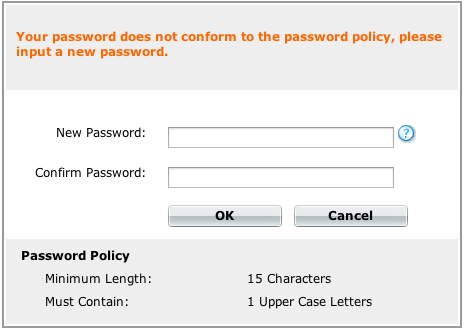
Lost Passwords
If an administrator password has been lost, refer to the SysAdmin’s Notebook article “Resetting a lost admin password,” found at docs.fortinet.com/p/sysadmin-s-notebook-and-tech-notes.
Configuration Backups
Once you configure the FortiGate unit and it is working correctly, it is extremely important that you backup the configuration. In some cases, you may need to reset the FortiGate unit to factory defaults or perform a TFTP upload of the firmware, which will erase the existing configuration. In these instances, the configuration on the device will have to be recreated, unless a backup can be used to restore it. You should also backup the local certificates, as the unique SSL inspection CA and server certificates that are generated by your FortiGate by default are not saved in a system backup.
It is also recommended that once any further changes are made that you backup the configuration immediately, to ensure you have the most current configuration available. Also, ensure you backup the configuration before upgrading the FortiGate unit’s firmware. Should anything happen during the upgrade that changes the configuration, you can easily restore the saved configuration.
Always backup the configuration and store it on the management computer or off-site. You have the option to save the configuration file to various locations including the local PC, USB key, FTP and TFTP site.The latter two are configurable through the CLI only.
If you have VDOMs, you can back up the configuration of the entire FortiGate unit or only a specific VDOM. Note that if you are using FortiManager or FortiCloud, full backups are performed and the option to backup individual VDOMs will not appear.
Backing up the configuration using the web-based manager
- Go to System > Dashboard > Status.
- On the System Information widget, select Backup for the System Configuration.
- Select to backup to your Local PC or to a USB key.
The USB Disk option will be grayed out if no USB drive is inserted in the USB port. You can also backup to the FortiManager using the CLI. - If VDOMs are enabled, select to backup the entire FortiGate configuration (Full Config) or only a specific VDOM configuration (VDOM Config).
- If backing up a VDOM configuration, select the VDOM name from the list.
- Select Encrypt configuration file.
Encryption must be enabled on the backup file to back up VPN certificates. - Enter a password and enter it again to confirm it. You will need this password to restore the file.
- Select Backup.
- The web browser will prompt you for a location to save the configuration file. The configuration file will have a .conf extension.
Backing up the configuration using the CLI
Use the following command:
execute backup config management-station <comment>
… or …
execute backup config usb <backup_filename> [<backup_password>]
… or for FTP, note that port number, username are optional depending on the FTP site…
execute backup config ftp <backup_filename> <ftp_server> [<port>] [<user_name>] [<password>]
… or for TFTP …
execute backup config tftp <backup_filename> <tftp_servers> <password>
Use the same commands to backup a VDOM configuration by first entering the commands:
config vdom
edit <vdom_name>
Backup and restore the local certificates
This procedure exports a server (local) certificate and private key together as a password protected PKCS12 file. The export file is created through a customer-supplied TFTP server. Ensure that your TFTP server is running and accessible to the FortiGate unit before you enter the command.
Backing up the local certificates
Connect to the CLI and use the following command:
execute vpn certificate local export tftp <cert_name> <filename> <tftp_ip>
where:
<cert_name>is the name of the server certificate.<filename>is a name for the output file.<tftp_ip>is the IP address assigned to the TFTP server host interface.
Restoring the local certificates - web-based manager
- Move the output file from the TFTP server location to the management computer.
- Go to System > Certificates > Local Certificates and select Import.
- Select the appropriate Type of certificate and fill in any required fields.
- Select Browse. Browse to the location on the management computer where the exported file has been saved, select the file and select Open.
- If required, enter the Password needed to upload the exported file..
- Select OK.
Restoring the local certificates - CLI
Connect to the CLI and use the following command:
execute vpn certificate local import tftp <filename> <tftp_ip>
Backup and restore a configuration file using SCP
You can use secure copy protocol (SCP) to download the configuration file from the FortiGate unit as an alternative method of backing up the configuration file or an individual VDOM configuration file. This is done by enabling SCP for and administrator account and enabling SSH on a port used by the SCP client application to connect to the FortiGate unit. SCP is enabled using the CLI commands:
config system global
set admin-scp enable
end
Use the same commands to backup a VDOM configuration by first entering the commands:
config global
set admin-scp enable
end
config vdom
edit <vdom_name>
Enable SSH access on the interface
SCP uses the SSH protocol to provide secure file transfer. The interface you use for administration must allow SSH access.
To enable SSH - web-based manager:
- Go to System > Network > Interface.
- Select the interface you use for administrative access and select Edit.
- In the Administrative Access section, select SSH.
- Select OK.
To enable SSH - CLI:
config system interface
edit <interface_name>
set allowaccess ping https ssh
end
|
|
When adding to, or removing a protocol, you must type the entire list again. For example, if you have an access list of HTTPS and SSH, and you want to add PING, typing:set allowaccess ping...only PING will be set. In this case, you must type... set allowaccess https ssh ping |
Using the SCP client
The FortiGate unit downloads the configuration file as sys_conf. Use the following syntax to download the file:
Linux
scp admin@<FortiGate_IP>:fgt-config <location>
Windows
pscp admin@<FortiGate_IP>:fgt-config <location>
The following examples show how to download the configuration file from a FortiGate-100D, at IP address 172.20.120.171, using Linux and Windows SCP clients.
Linux client example
To download the configuration file to a local directory called ~/config, enter the following command:
scp admin@172.20.120.171:fgt-config ~/config
Enter the admin password when prompted.
Windows client example
To download the configuration file to a local directory called c:\config, enter the following command in a Command Prompt window:
pscp admin@172.20.120.171:fgt-config c:\config
Enter the admin password when prompted.
SCP public-private key authentication
SCP authenticates itself to the FortiGate unit in the same way as an administrator using SSH accesses the CLI. Instead of using a password, you can configure the SCP client and the FortiGate unit with a public-private key pair.
To configure public-private key authentication
- Create a public-private key pair using a key generator compatible with your SCP client.
- Save the private key to the location on your computer where your SSH keys are stored.
This step depends on your SCP client. The Secure Shell key generator automatically stores the private key. - Copy the public key to the FortiGate unit using the CLI commands:
config system admin
edit admin
set ssh-public-key1 "<key-type> <key-value>"
end
<key-type>must be the ssh-dss for a DSA key or ssh-rsa for an RSA key. For the<key-value>, copy the public key data and paste it into the CLI command.
If you are copying the key data from Windows Notepad, copy one line at a time and ensure that you paste each line of key data at the end of the previously pasted data. As well:
- Do not copy the end-of-line characters that appear as small rectangles in Notepad.
- Do not copy the
---- BEGIN SSH2 PUBLIC KEY ---- or Comment: “[2048-bit dsa,...]”lines. - Do not copy the
---- END SSH2 PUBLIC KEY ----line.
- Type the closing quotation mark and press Enter.
Your SCP client can now authenticate to the FortiGate unit based on SSH keys rather than the administrator password.
Restoring a configuration using SCP
To restore the configuration using SCP, use the commands:
scp <local_file> <admin_user>@<FGT_IP>:fgt-restore-config
To use this command/method of restoring the FortiGate configuration, you need to log in as the “admin” administrator.
Restoring a configuration
Should you need to restore a configuration file, use the following steps:
To restore the FortiGate configuration - web-based manager
- Go to System > Dashboard > Status.
- On the System Information widget, select Restore for the System Configuration.
- Select to upload the configuration file to be restored from your Local PC or a USB key.
The USB Disk option will be grayed out if no USB drive is inserted in the USB port. You can restore from the FortiManager using the CLI. - Enter the path and file name of the configuration file, or select Browse to locate the file.
- Enter a password if required.
- Select Restore.
To back up the FortiGate configuration - CLI
execute restore config management-station normal 0
… or …
execute restore config usb <filename> [<password>]
… or for FTP, note that port number, username are optional depending on the FTP site…
execute backup config ftp <backup_filename> <ftp_server> [<port>] [<user_name>] [<password>]
… or for TFTP …
execute backup config tftp <backup_filename> <tftp_server> <password>
The FortiGate unit will load the configuration file and restart. Once the restart has completed, verify that the configuration has been restored.
Configuration revisions
The Revisions options on the System Information widget enables you to manage multiple versions of configuration files. Revision control requires either a configured central management server, or FortiGate units with 512 MB or more of memory. The central management server can either be a FortiManager unit or the FortiCloud.
When revision control is enabled on your unit, and configurations have been backed up, a list of saved revisions of those backed-up configurations appears.
Restore factory defaults
There may be a point where need to reset the FortiGate unit to its original defaults; for example, to begin with a fresh configuration. There are two options when restoring factory defaults. The first resets the entire device to the original out-of-the-box configuration:
To reset the FortiGate unit to its factory default settings - web-based manager
- Go to System > Dashboard > Status.
- In the System Information widget, select Restore for the System Configuration.
- Select Restore Factory Defaults at the top of the page.
You can reset using the CLI by entering the command:
execute factoryreset
When prompted, type y to confirm the reset.
Alternatively, in the CLI you can reset the factory defaults but retain the interface and VDOM configuration.
Use the command:
execute factoryreset2

