Monitoring authenticated users
This section describes how to view lists of currently logged-in firewall and VPN users. It also describes how to disconnect users.
The following topics are included in this section:
- Monitoring firewall users
- Monitoring SSL VPN users
- Monitoring IPsec VPN users
- Monitoring users Quarantine
Monitoring firewall users
To monitor firewall users, go to User & Device > Monitor > Firewall.
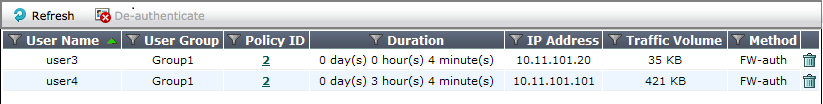
You can de-authenticate a user by selecting the Delete icon for that entry.
You can filter the list of displayed users by selecting the funnel icon for one of the column titles or selecting Filter Settings.
Optionally, you can de-authenticate multiple users by selecting them and then selecting De-authenticate.
Monitoring SSL VPN users
You can monitor web-mode and tunnel-mode SSL VPN users by username and IP address.
To monitor SSL VPN users, go to VPN > Monitor > SSL-VPN Monitor. To disconnect a user, select the user and then select the Delete icon.
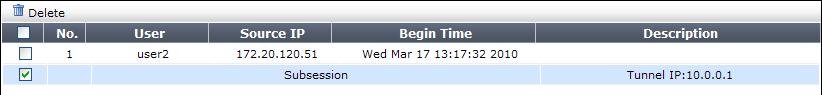
The first line, listing the username and IP address, is present for a user with either a web-mode or tunnel-mode connection. The Subsession line is present only if the user has a tunnel mode connection. The Description column displays the virtual IP address assigned to the user’s tunnel-mode connection.
For more information about SSL VPN, see the FortiOS Handbook SSL VPN guide.
To monitor SSL VPN users - CLI:
To list all of the SSL VPN sessions and their index numbers:
execute vpn sslvpn list
The output looks like this:
SSL-VPN Login Users:
Index User Auth Type Timeout From HTTPS in/out
0 user1 1 256 172.20.120.51 0/0
SSL-VPN sessions:
Index User Source IP Tunnel/Dest IP
0 user2 172.20.120.51 10.0.0.1
You can use the Index value in the following commands to disconnect user sessions:
To disconnect a tunnel-mode user
execute vpn sslvpn del-tunnel <index>
To disconnect a web-mode user
execute vpn sslvpn del-web <index>
You can also disconnect multiple users:
To disconnect all tunnel-mode SSL VPN users in this VDOM
execute vpn ssl del-all tunnel
To disconnect all SSL VPN users in this VDOM
execute vpn ssl del-all
Monitoring IPsec VPN users
To monitor IPsec VPN tunnels in the web-based manager, go to VPN > Monitor > IPsec Monitor. user names are available only for users who authenticate with XAuth.
You can close a tunnel by selecting the tunnel and right click to select Bring Down.
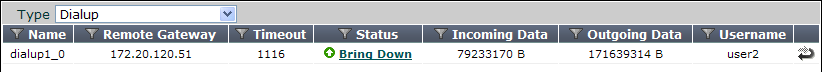
For more information, see the FortiOS Handbook IPsec VPN guide.
Monitoring users Quarantine
The User Quarantine list shows all IP addresses and interfaces blocked by NAC quarantine. The list also shows all IP addresses, authenticated users, senders, and interfaces blocked by Data Leak Prevention (DLP). The system administrator can selectively release users or interfaces from quarantine or configure quarantine to expire after a selected time period.
All sessions started by users or IP addresses on the User Quarantine list are blocked until the user or IP address is removed from the list. All sessions to an interface on the list are blocked until the interface is removed from the list.
You can configure NAC quarantine to add users or IP addresses to the User Quarantine list under the following conditions:
- Users or IP addresses that originate attacks detected by IPS - To quarantine users or IP addresses that originate attacks, enable and configure Quarantine in an IPS Filter.
- Users or IP addresses that are quarantined by Data Leak Prevention - In a DLP sensor select Quarantine IP Address as the action to take.
For more information, see FortiOS Handbook Security Profiles guide.
Users are viewed from User & Device > Monitor > User Quarantine.
| Delete | Removes the selected user or IP address from the User Quarantine list. |
| Remove All | Removes all users and IP addresses from the User Quarantine list. |
| Search | Search the list for a particular IP address. |
| Source | The FortiGate function that caused the user or IP address to be added to the User Quarantine list: IPS or Data Leak Prevention. |
| Created | The date and time the user or IP address was added to the Banned User list. |
| Expires | The date and time the user or IP address will be automatically removed from the User Quarantine list. If Expires is Indefinite, you must manually remove the user or host from the list. |

