Figure 56: An HTML form with two inputs: Account ID‘s type attribute is text; Password’s type attribute is password 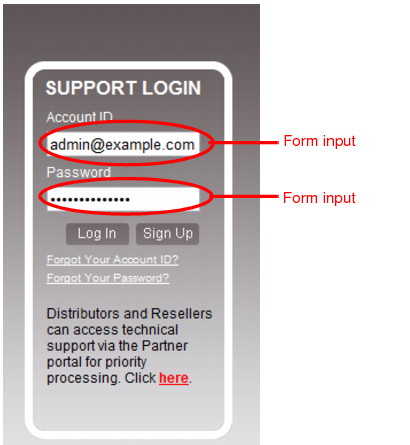
FortiWeb cannot enforcement the rule if the parameter is bigger than the memory size you have configured for FortiWeb’s scan buffers. To configure the buffer size, see http-cachesize in the FortiWeb CLI Reference. If your web applications do not require requests larger than the buffer, enable Malformed Request to harden your configuration. |
Setting name | Description |
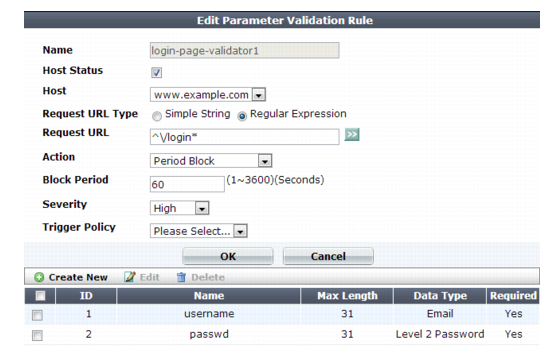
Name | Type a unique name that can be referenced in other parts of the configuration. Do not use spaces or special characters. The maximum length is 35 characters. |
Host Status | Enable to apply this input rule only to HTTP requests for specific web hosts. Also configure Host. Disable to match the input rule based upon the other criteria, such as the URL, but regardless of the Host: field. |
Host | Select which protected host names entry (either a web host name or IP address) that the Host: field of the HTTP request must be in to match the signature exception. This option is available only if Host Status is enabled. |
Request URL Type | Select whether the Request URL field must contain a literal URL (Simple String), or a regular expression designed to match multiple URLs (Regular Expression). |
Request URL | Depending on your selection in Request URL Type, type either: • the literal URL, such as /index.php, that the HTTP request must contain in order to match the input rule. The URL must begin with a backslash ( / ). • a regular expression, such as ^/*.php, matching all and only the URLs to which the input rule should apply. The pattern does not require a slash ( / ).; however, it must at least match URLs that begin with a slash, such as /index.cfm. Do not include the domain name, such as www.example.com, which is configured separately in the Host drop-down list. To create and test a regular expression, click the >> (test) icon. This opens the Regular Expression Validator window where you can fine-tune the expression (see “Regular expression syntax” and “Cookbook regular expressions”). |
Action | Select the action FortiWeb takes when it detects a rule violation: • Alert — Accept the connection and generate an alert email and/or log message. • Alert & Deny — Block the request (reset the connection) and generate an alert and/or log message. You can customize the web page that FortiWeb returns to the client with the HTTP status code. See “Customizing error and authentication pages (replacement messages)”. • Period Block — Block subsequent requests from the client for a number of seconds. Also configure Block Period. You can customize the web page that FortiWeb returns to the client with the HTTP status code. See “Customizing error and authentication pages (replacement messages)”. Note: If FortiWeb is deployed behind a NAT load balancer, when using this option, you must also define an X-header that indicates the original client’s IP (see “Defining your proxies, clients, & X-headers”). Failure to do so may cause FortiWeb to block all connections when it detects a violation of this type. • Redirect — Redirect the request to the URL that you specify in the protection profile and generate an alert and/or log message. Also configure Redirect URL and Redirect URL With Reason. • Send 403 Forbidden — Reply with an HTTP 403 Access Forbidden error message and generate an alert and/or log message. The default value is Alert. See also “Reducing false positives”. Caution: This setting will be ignored if Monitor Mode is enabled. Note: Logging and/or alert email will occur only if enabled and configured. See “Logging” and “Alert email”. Note: If you will use this rule set with auto-learning, you should select Alert. If Action is Alert & Deny, or any other option that causes the FortiWeb appliance to terminate or modify the request or reply when it detects an attack attempt, the interruption will cause incomplete session information for auto-learning. |
Block Period | Type the number of seconds that you want to block subsequent requests from the client after the FortiWeb appliance detects that the client has violated the rule. This setting is available only if Action is set to Period Block. The valid range is from 1 to 3,600 (1 hour). The default value is 1. See also “Monitoring currently blocked IPs”. |
Severity | When rule violations are recorded in the attack log, each log message contains a Severity Level (severity_level) field. Select which severity level the FortiWeb appliance will use when it logs a violation of the rule: • Low • Medium • High The default value is High. |
Trigger Action | Select which trigger, if any, that the FortiWeb appliance will use when it logs and/or sends an alert email about a violation of the rule. See “Configuring triggers”. |
Setting name | Description |
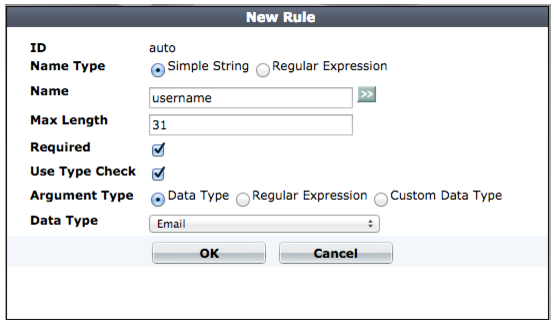
Name Type | Select one of the following options: • Simple String — Name contains the name attribute of the parameter’s input tag exactly as it appears in the form on the web page. • Regular Expression — Name contains a regular expression designed to match the name attribute of the parameter’s input tag. |
Name | Enter one of the following: • The value of the name attribute of the parameter’s input tag exactly as it appears in the form on the web page (if Name Type is Simple String). For example, for an input tag that is defined by the following HTML code, enter pwd: <input type="password" name="pwd" /> • A regular expression that matches the name attribute of the parameter’s input tag (if Name Type is Regular Expression). Note: FortiWeb does not support regular expressions that begin with an exclamation point ( ! ) . For information on language and regular expression matching, see “Regular expression syntax”. |
Max Length | Type the maximum length of the string that is the input’s value. For example, if the input’s value is always a short string like candy, the maximum length could be 5. If the value is a number less than 100 such as 42, the maximum length should be 2 (since the number “42” is 2 characters long). To disable the length limit, type 0. Tip: See also Malformed Request. |
Required | Enable if the parameter is required for HTTP/HTTPS requests to this combination of Host: field and URL. |
Use Type Check | Enable to validate the data type of the parameter. Also configure Argument Type. |
Argument Type | Select one of: This option is only applicable when Use Type Check is enabled. |
Data Type | Select a predefined data type. See “Predefined data types”. This option is only available when Argument Type is Data Type. |
Regular Expression | Type a regular expression that matches all valid values, and no invalid values, for this input. This option is only available when Argument Type is Regular Expression. To create and test a regular expression, click the >> (test) icon. This opens the Regular Expression Validator window where you can fine-tune the expression (see “Regular expression syntax”). |
Custom Data Type | Select a custom data type. See “Defining custom data types”. This option is only available when Argument Type is Custom Data Type. |
If you do not want sensitive inputs such as passwords to appear in the attack logs’ packet payloads, you can obscure them. For details, see “Obscuring sensitive data in the logs”. |