Remote authentication servers
If you already have LDAP or RADIUS servers configured on your network, FortiAuthenticator can connect to them for remote authentication, much like FortiOS remote authentication.
LDAP
If you have existing LDAP servers, you may choose to continue using them with FortiAuthenticator by configuring them as remote LDAP servers.
|
|
When entering the remote LDAP server information, if any information is missing or in the wrong format, error messages will highlight the problem for you. |
|
|
FortiAuthenticator supports multiple Windows AD server forests, with a maximum of 20 Remote LDAP servers with Windows AD enabled. To view all information about your multiple servers, go to Monitor > Authentication > Windows AD. |
To add a remote LDAP server entry:
- Go to Authentication > Remote Auth. Servers > LDAP and select Create New. The Create New LDAP Server window opens.
- Enter the following information.
- If you want to want to import a specific LDAP system's template, under Query Elements, enter the following:
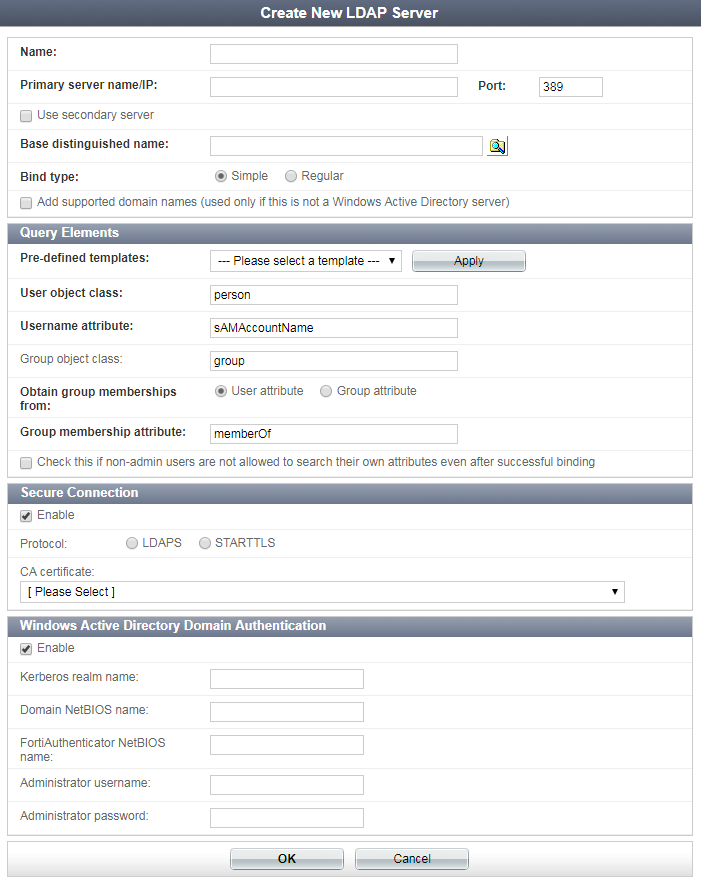
| Pre-defined templates | Select a pre-defined template from the dropdown menu: Microsoft Active Directory, OpenLDAP, or Novell eDirectory. |
| User object class | The type of object class to search for a user name search. The default is person. |
| Username attribute | The LDAP attribute that contains the user name. The default is sAMAccountName. |
| Group object class | The type of object class to search for a group name search. The default is group. |
| Obtain group memberships from | The LDAP attribute (either user or group) used to obtain group membership. The default is User attribute. |
| Group membership attribute | Used as the attribute to search for membership of users or groups in other groups. |
| Check this if non-admin users are not allowed to search their own attributes even after successful binding | This feature has been implemented to enhance Oracle-based ODSEE LDAP support. |
- If you want to have a secure connection between the FortiAuthenticator unit and the remote LDAP server, under Secure Connection, select Enable, then enter the following:
- If you want to authenticate users using MSCHAP2 PEAP in an Active Directory environment, enable Windows Active Directory Domain Authentication, then enter the required Windows AD Domain Controller information.
- If you want to import remote LDAP users, select to either Import users or Import users by group memberships under Remote LDAP Users. Once a method is chosen, select Go. This will open a separate window where you may specify the LDAP server, apply filters, and attributes. Select Configure user attributes to apply/edit the following LDAP user mapping attributes:
| Protocol | Select LDAPS or STARTLS as the LDAP server requires. |
| CA Certificate | Select the CA certificate that verifies the server certificate from the dropdown menu. |
| Kerberos realm name | Enter the domain’s DNS name in uppercase letters. |
| Domain NetBIOS name | Enter the domain’s DNS prefix in uppercase letters. |
| FortiAuthentication NetBIOS name | Enter the NetBIOS name that will identify the FortiAuthenticator unit as a domain member. |
| Administrator username | Enter the name of the user account that will be used to associate the FortiAuthenticator unit with the domain. This user must have at least Domain User privileges. |
| Administrator password | Enter the administrator account’s password. |
When you are finished here, go to Authentication > RADIUS Service > Clients to choose whether authentication is available for all Windows AD users or only for Windows AD users who belong to particular user groups that you select. See RADIUS service for more information.
| Username |
Enter the remote LDAP user's name. Newly introduced in FortiAuthenticator 4.3. |
| First name | Enter the attribute that specifies the user's first name. Set to givenName by default. |
| Last name | Enter the attribute that specifies the user's last name. Set to sn by default. |
| Enter the attribute that specifies the user's email address. Set to mail by default. | |
| Phone | Enter the attribute that specifies the user's number. Set to telephoneNumber by default. |
| Mobile number | Enter the attribute that specifies the user's mobile number. Set to mobile by default. |
| FTK-200 serial number | Enter the remote LDAP user's FortiToken serial number. |
| Certificate binding common name |
Enter the remote LDAP user's certificate-binding CN. When this field is populated, the Certificate binding CA must also be specified. Newly introduced in FortiAuthenticator 4.3. |
| Certificate binding CA |
Local or trusted CAs to apply for the remote LDAP user. Must be specified if the Certificate binding common name is populated. Newly introduced in FortiAuthenticator 4.3. |
- Select OK to apply your changes.
You can now add remote LDAP users, as described in Remote users.
Remote LDAP password change
Windows AD users can conveniently change their passwords without provision changes being made to the network by a Windows AD system administrator. There are three ways FortiAuthenticator supports a password change: RADIUS Login, GUI User Login, and GUI User Portal.
RADIUS Login
For the method to work, all of the following conditions must be met:
- FortiAuthenticator has joined the Windows AD domain
- RADIUS client has been configured to "Use Windows AD domain authentication"
- RADIUS authentication request uses MS-CHAPv2
- RADIUS client must also support MS-CHAPv2 password change
A "change password" response will be produced that FortiAuthenticator will recognize, which will allow cooperation between the NAS and the Windows AD server that will result in a password change.
GUI User Login
For this method to work, one of the following conditions must be met:
- FortiAuthenticator has joined the Windows AD domain
- Secure LDAP is enabled and the LDAP admin (i.e. regular bind) has the permissions to reset user passwords
You must log in via the GUI portal. FortiAuthenticator will validate the user password against a Windows AD server. The Windows AD server will return with a "change password" response. If that happens, the user will be prompted to enter a new password.
GUI User Portal
For this method to work, one of the following conditions must be met:
- FortiAuthenticator has joined the Windows AD domain
- Secure LDAP is enabled
Once successfully logged into the GUI, the user has access to the user portal. If desired, the user can change their password in the user portal.
RADIUS
If you have existing RADIUS servers, you may choose to continue using them with FortiAuthenticator by configuring them as remote RADIUS servers.This feature can also be used to migrate away from third party two-factor authentication platforms.
|
|
When entering the remote RADIUS server information, if any information is missing or in the wrong format, error messages will highlight the problem for you. |
To add a remote RADIUS server entry:
- Go to Authentication > Remote Auth. Servers > RADIUS and select Create New. The Create New RADIUS Server window opens.
- Enter the following information, then select OK to add the RADIUS server.
| Name | Enter the name for the remote RADIUS server on FortiAuthenticator. |
| Primary Server | Enter the server name or IP address, port and secret in their requisite locations to configure the primary server. |
| Secondary Server | Optionally, add redundancy by configuring a secondary server. |
| User Migration | Select Enable learning mode to record and learn users that authenticate against this RADIUS server. This option should be enabled if you need to migrate users from the server to the FortiAuthenticator. Select View Learned Users to view the list of learned users. See Learned RADIUS users. |
