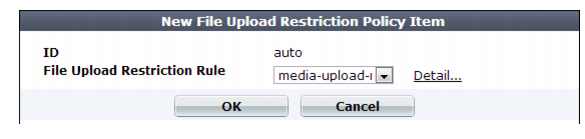
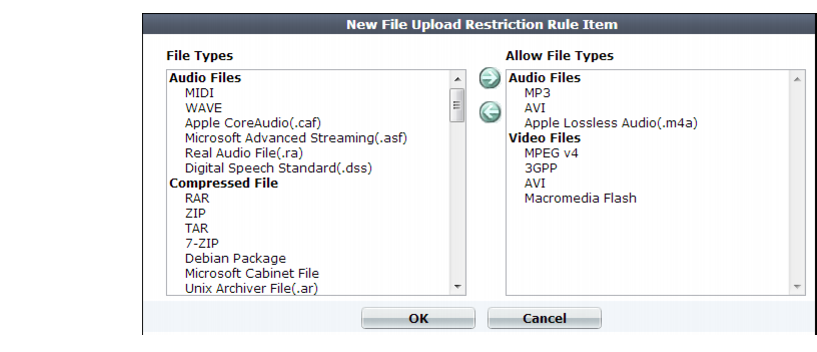
A dialog appears.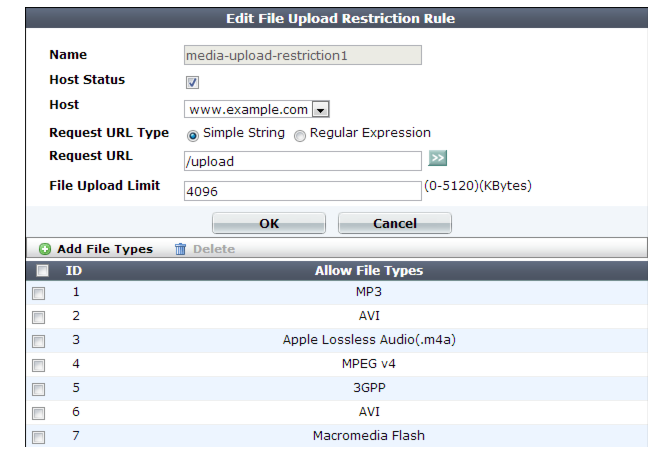
Microsoft Office Open XML file types such as .docx, xlsx, .pptx, and .vsdx are a type of ZIP-compressed XML. If you specify restrictions for them, those signatures will take priority. However, if you do not select a MSOOX restriction but do have an XML or ZIP restriction, the XML and ZIP restrictions will still apply, and the files will still be restricted. |
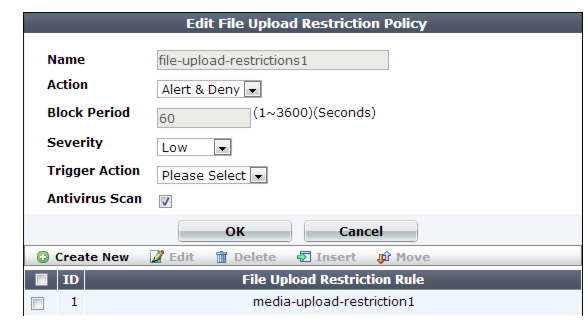
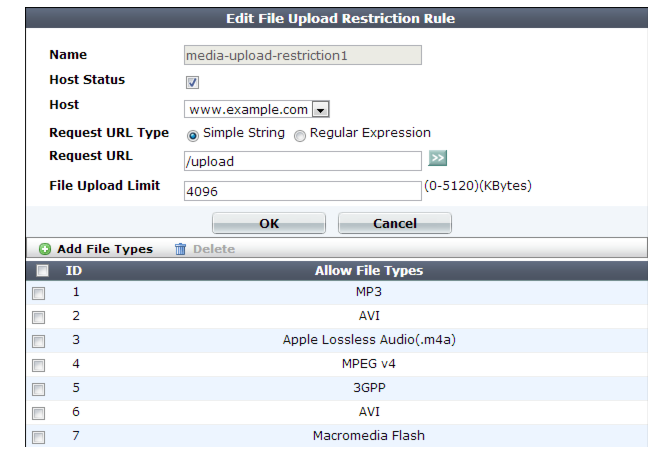
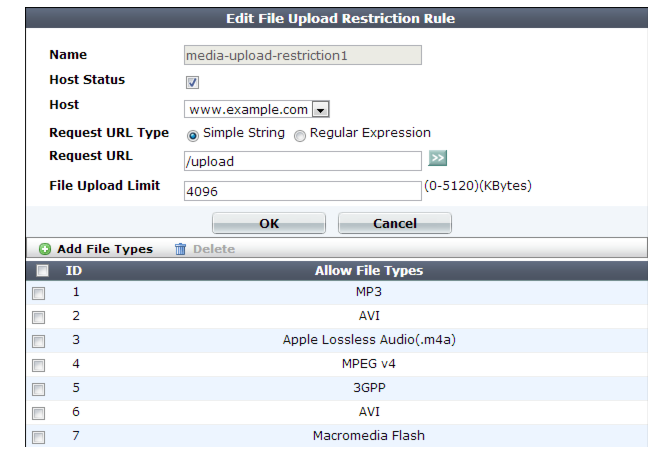
Setting name | Description |
Name | Type a unique name that can be referenced in other parts of the configuration. Do not use spaces or special characters. The maximum length is 35 characters. |
Action | Select which action the FortiWeb appliance will take when it detects a violation of the rule: • Alert — Accept the connection and generate an alert email and/or log message. • Alert & Deny — Block the request (reset the connection) and generate an alert and/or log message. You can customize the web page that FortiWeb returns to the client with the HTTP status code. See “Customizing error and authentication pages (replacement messages)”. • Period Block — Block subsequent requests from the client for a number of seconds. Also configure Block Period. You can customize the web page that FortiWeb returns to the client with the HTTP status code. See “Customizing error and authentication pages (replacement messages)”. Note: If FortiWeb is deployed behind a NAT load balancer, when using this option, you must also define an X-header that indicates the original client’s IP (see “Defining your proxies, clients, & X-headers”). Failure to do so may cause FortiWeb to block all connections when it detects a violation of this type. The default value is Alert. Caution: This setting will be ignored if Monitor Mode is enabled. Note: Logging and/or alert email will occur only if enabled and configured. See “Logging” and “Alert email”. Note: If you will use this rule set with auto-learning, you should select Alert. If Action is Alert & Deny, or any other option that causes the FortiWeb appliance to terminate or modify the request or reply when it detects an attack attempt, the interruption will cause incomplete session information for auto-learning. |
Block Period | Type the number of seconds that you want to block subsequent requests from the client after the FortiWeb appliance detects that the client has violated the rule. This setting is available only if Action is set to Period Block. The valid range is from 1 to 3,600 (1 hour). The default value is 1. See also “Monitoring currently blocked IPs”. |
Severity | When rule violations are recorded in the attack log, each log message contains a Severity Level (severity_level) field. Select which severity level the FortiWeb appliance will use when it logs a violation of the rule: • Low • Medium • High The default value is High. |
Trigger Action | Select which trigger, if any, that the FortiWeb appliance will use when it logs and/or sends an alert email about a violation of the rule. See “Configuring triggers”. |
Antivirus Scan | Enable to scan for trojans. Also enable the signatures (Trojans) and configure the antivirus-specific Action, Block Period, Severity, and Trigger Action (see “Blocking known attacks & data leaks”). Attackers often modify HTTP header so that the request’s Content‑Type: does not match — it indicates an allowed file type, but the byte code contained in the body is actually a virus. This scan ensures that the request actually contains the file type that it professes, and that it is not infected. |