4. Configure these settings: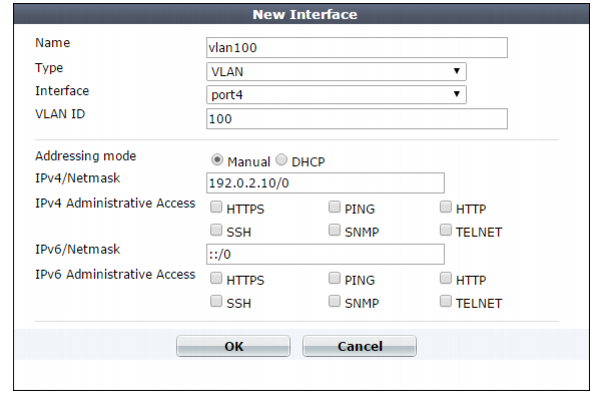
VLANs are not designed to be a security measure, and should not be used where untrusted devices and/or individuals outside of your organization have access to the equipment. VLAN tags are not authenticated, and can be ignored or modified by attackers. VLAN tags rely on the voluntary compliance of the receiving host or switch. |
Setting name | Description | |
Name | Type the name (such as vlan100) of this VLAN subinterface that can be referenced by other parts of the configuration. Do not use spaces or special characters. The maximum length is 15 characters. Tip: The name cannot be changed once you save the entry. For a workaround, see “Renaming entries”. | |
Interface | Select the name of the physical network port with which the VLAN subinterface will be associated. | |
VLAN ID | Type the VLAN ID , such as 100, of packets that belong to this VLAN subinterface. • If one physical network port (that is, a VLAN trunk) will handle multiple VLANs, create multiple VLAN subinterfaces on that port, one for each VLAN ID that will be received. • If multiple different physical network ports will handle the same VLANs, on each of the ports, create VLAN subinterfaces that have the same VLAN IDs. The valid range is between 1 and 4094 and must match the VLAN ID added by the IEEE 802.1q-compliant router or switch connected to the VLAN subinterface. For the maximum number of interfaces for your FortiWeb model, including VLAN subinterfaces, see “Appendix B: Maximum configuration values”. Note: Inter-VLAN routing is not supported if the FortiWeb appliance is operating in true transparent proxy mode. In that case, you must configure the same VLAN IDs on each physical network port. | |
Addressing Mode | Specify whether FortiWeb acquires an IPv4 address for this VLAN using DHCP. You can configure only one network interface to obtain its address using DHCP. | |
IP/Netmask | Type the IP address/subnet mask associated with the VLAN, if any. The IP address must be on the same subnet as the network to which the interface connects. Two network interfaces cannot have IP addresses on the same subnet. | |
Administrative Access | Enable the types of administrative access that you want to permit to this interface. These options do not disable outgoing administrative connections, such as update polling connections to the FDN or outgoing ICMP resulting from a CLI command such as execute ping. Neither do they govern traffic destined for a web server or virtual server, which are governed by policies. These options only govern incoming connections destined for the appliance itself. Caution: Enable only on network interfaces connected to trusted private networks (defined in Trusted Host #1, Trusted Host #2, Trusted Host #3) or directly to your management computer. If possible, enable only secure administrative access protocols such as HTTPS or SSH. Failure to restrict administrative access could compromise the security of your FortiWeb appliance. | |
HTTPS | Enable to allow secure HTTPS connections to the web UI through this network interface. To configure the listening port number, see “Global web UI & CLI settings”. | |
PING | Enable to allow: • ICMP type 8 (ECHO_REQUEST) • UDP ports 33434 to 33534 for ping and traceroute to be received on this network interface. When it receives an ECHO_REQUEST (“ping”), FortiWeb will reply with ICMP type 0 (ECHO_RESPONSE or “pong”). Note: Disabling PING only prevents FortiWeb from receiving ICMP type 8 (ECHO_REQUEST) and traceroute-related UDP. It does not disable FortiWeb CLI commands such as execute ping or execute traceroute that send such traffic. | |
HTTP | Enable to allow HTTP connections to the web UI through this network interface. To configure the listening port number, see “Global web UI & CLI settings”. Caution: HTTP connections are not secure, and can be intercepted by a third party. If possible, enable this option only for network interfaces connected to a trusted private network, or directly to your management computer. Failure to restrict administrative access through this protocol could compromise the security of your FortiWeb appliance. | |
SSH | Enable to allow SSH connections to the CLI through this network interface. | |
SNMP | Enable to allow SNMP queries to this network interface, if queries have been configured and the sender is a configured SNMP manager. To configure the listening port number and configure queries and traps, see “SNMP traps & queries”. | |
TELNET | Enable to allow Telnet connections to the CLI through this network interface. Caution: Telnet connections are not secure, and can be intercepted by a third party. If possible, enable this option only for network interfaces connected to a trusted private network, or directly to your management computer. Failure to restrict administrative access through this protocol could compromise the security of your FortiWeb appliance. | |