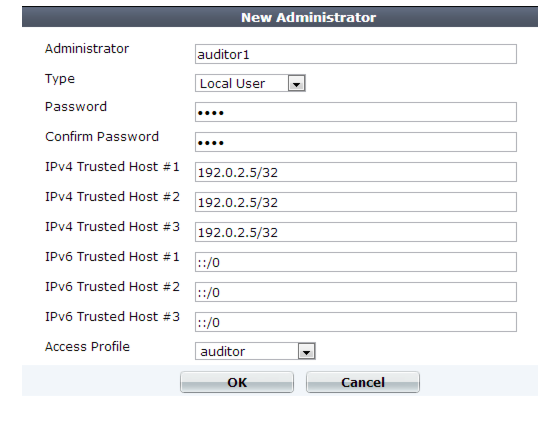
4. Configure these settings: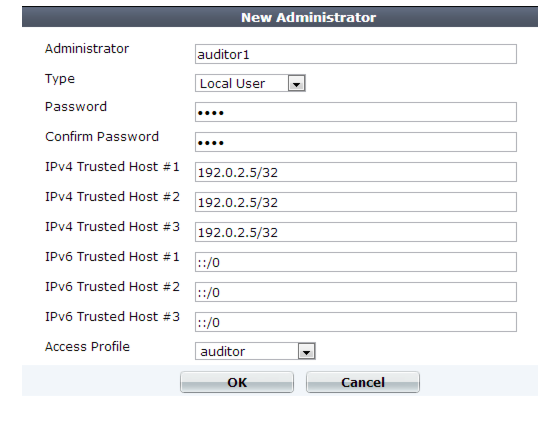
To prevent multiple administrators from logging in simultaneously, which could allow them to inadvertently overwrite each other’s changes, enable Enable Single Admin User login. For details, see “Global web UI & CLI settings”. |
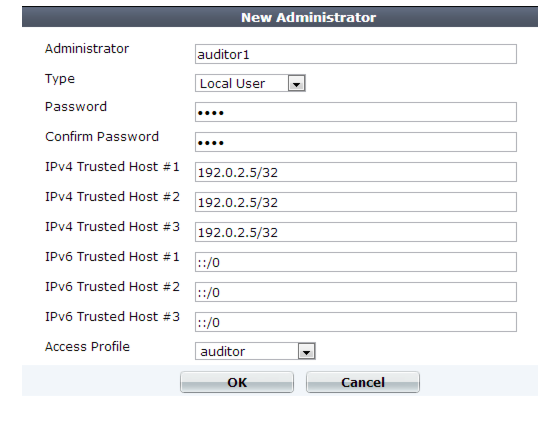
Setting name | Description | |
Administrator | Type the name of the administrator account, such as admin1 or admin@example.com, that can be referenced in other parts of the configuration. Do not use spaces or special characters except the ‘at’ symbol ( @ ). The maximum length is 35 characters. Note: This is the user name that the administrator must provide when logging in to the CLI or web UI. If using an external authentication server such as RADIUS or Active Directory, this name will be passed to the server via the remote authentication query. | |
Type | Select either: • Local User — Authenticate using an account whose name, password, and other settings are stored locally, in the FortiWeb appliance’s configuration. • Remote User — Authenticate by querying the remote server that stores the account’s name and password. Also configure Admin User Group. | |
Password | Type a password for the administrator account. Tip: Set a strong password for every administrator account, and change the password regularly. Failure to maintain the password of every administrator account could compromise the security of your FortiWeb appliance. As such, it can constitute a violation of PCI DSS compliance and is against best practices. For improved security, the password should be at least eight characters long, be sufficiently complex, and be changed regularly. To check the strength of your password, you can use a utility such as Microsoft’s password strength meter. | |
Confirm Password | Re-enter the password to confirm its spelling. | |
Admin User Group | Select a remote authentication query set. See “Grouping remote authentication queries for administrators”. Caution: Secure your authentication server and, if possible, all query traffic to it. Compromise of the authentication server could allow attackers to gain administrative access to your FortiWeb. | |
Wildcard | Specifies whether the user-configured access profile in a remote authentication server overrides the access profile that is configured in FortiWeb. | |
Trusted Host #1 Trusted Host #2 Trusted Host #3 | Type the source IP address(es) and netmask from which the administrator is allowed to log in to the FortiWeb appliance. If PING is enabled, this is also a source IP address to which FortiWeb will respond when it receives a ping or traceroute signal. Trusted areas can be single hosts, subnets, or a mixture. For more information, see “Trusted hosts”. To allow logins only from one computer, enter its IP address and 32- or 128-bit netmask in all Trusted Host fields: 192.0.2.2/32 2001:0db8:85a3:::8a2e:0370:7334/128 Caution: If you configure trusted hosts, do so for all administrator accounts. Failure to do so means that all accounts are still exposed to the risk of brute force login attacks. This is because if you leave even one administrator account unrestricted (i.e. any of its Trusted Host settings is 0.0.0.0/0.0.0.0), the FortiWeb appliance must allow login attempts on all network interfaces where remote administrative protocols are enabled, and wait until after a login attempt has been received in order to check that user name’s trusted hosts list. Tip: If you allow login from the Internet, set a longer and more complex Password, and enable only secure administrative access protocols (HTTPS and SSH) to minimize the security risk. For information on administrative access protocols, see “Configuring the network interfaces”. Also restrict trusted hosts to IPs in your administrator’s geographical area. Tip: For improved security, restrict all trusted host addresses to single IP addresses of computer(s) from which only this administrator will log in. | |
Access Profile | Select an existing access profile to grant permissions for this administrator account. For more information on permissions, see “Configuring access profiles” and “Permissions”. You can select prof_admin, a special access profile used by the admin administrator account. However, selecting this access profile will not confer all of the same permissions of the admin administrator. For example, the new administrator would not be able to reset lost administrator passwords. This option does not appear for the admin administrator account, which by definition always uses the prof_admin access profile. Tip: Alternatively, if your administrator accounts authenticate via a RADIUS query, you can override this setting and assign their access profile through the RADIUS server using RFC 2548 Microsoft Vendor-specific RADIUS Attributes. On the RADIUS server, create an attribute named: ATTRIBUTE Fortinet-Access-Profile 6 then set its value to be the name of the access profile that you want to assign to this account. Finally, in the CLI, enter the command to enable the override: config system admin edit "admin1" set accprofile-override enable end If none is assigned on the RADIUS server, or if it does not match the name of an existing access profile on FortiWeb, FortiWeb will fail back to use the one locally assigned by this setting. | |
Administrative Domain | Select which existing ADOM to assign this administrator account to it, and to restrict its permissions to that ADOM. For more information on ADOMs, see “Administrative domains (ADOMs)” and “Permissions”. This option appears only if ADOMs are enabled, and if Administrative Domain is not prof_admin. (prof_admin implies global access, with no restriction to an ADOM.) | |