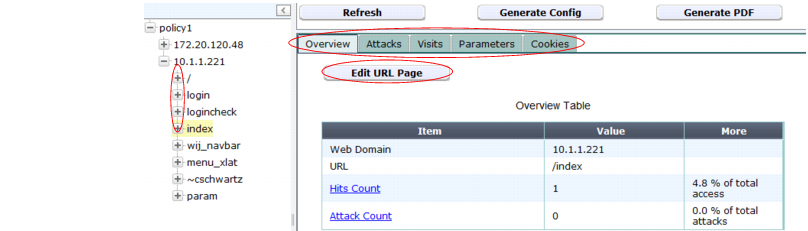
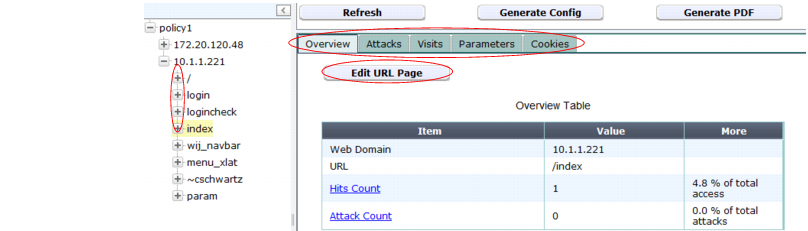
If you want to adjust the behavior of the profile and components to generate, in the left-hand pane, click the expand icon ( + ) next to items to expand the tree, then click the name of the single URL whose protection you want to manually configure.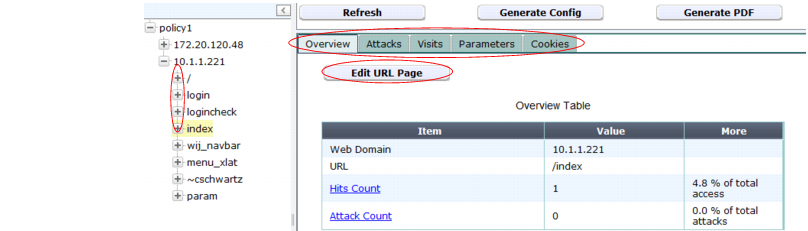
Setting name | Description | |
Overview tab | ||
Edit Protected Servers | Click to open a pop-up dialog. Enable or disable the IP addresses and/or domain names that will be members of the generated protected host names group. For details, see “Defining your protected/allowed HTTP “Host:” header names”. This appears only if you have selected the name of the auto-learning profile in the navigation pane. | |
Edit URL Page | Click to open a pop-up dialog. Enable or disable whether the currently selected URL will be included in start pages and white/black IP list rules in the generated profile. This appears only if you have selected a URL in the navigation pane. For more information on those rule types, see “Specifying URLs allowed to initiate sessions” and “Access control”. | |
Attacks tab | ||
Action and Enable | Select from the Enable drop-down list to enable or disable detection of each type of attack, and select from Action which action that the generated profile will take. The availability of these lists varies with the level of the item selected in the navigation pane. | |
Visits tab | ||
Edit Allow Method | Click to open a pop-up dialog. Change the Status option to select which HTTP request methods to allow in the generated profile. This appears only if you have selected a profile in the navigation pane. | |
Edit URL Access | Click to open a pop-up dialog. This appears only if you have selected a profile in the navigation pane. For details, see “Access control”. | |
Edit Start Page | Click to open a pop-up dialog. This appears only if you have selected a profile in the navigation pane. For details, see “Specifying URLs allowed to initiate sessions”. | |
Edit Exception Method | Click to open a pop-up dialog. This appears only if you have selected a URL in the navigation pane. For details, see “Configuring allowed method exceptions”. | |
Most hit IP table: Edit Content Type | Click to edit the values that FortiWeb adds to the Content Type filter in an automatically generated Advanced Protection custom rule. This rule is designed to detect web scraping (content scraping) activity. Available only if a policy or host is selected in the navigation pane. For more information, see “Most hit IP table and web scraping detection”. | |
Most hit IP table: row selection button | Selects the data that FortiWeb uses to create an Occurrence filter in an Advanced Protection custom rule in the generated profile. This rule is designed to detect web scraping activity. Available only if a policy or host is selected in the navigation pane. For more information, see “Most hit IP table and web scraping detection”. | |
Parameters tab | ||
Set | Type the data type and maximum length of the parameter, and indicate whether or not the parameter is required input. These settings will appear in the generated parameter validation rule and input rules. For details, see “Validating parameters (“input rules”)” and “Preventing zero-day attacks”. Caution: Before you leave the page, mark the Custom check boxes for rows where you have clicked this icon. Failure to do so will cause FortiWeb appliance to discard your settings when you leave the page. | |
Custom | Before you click Set or leave the page, enable this option for each row whose manual settings you want to save. | |
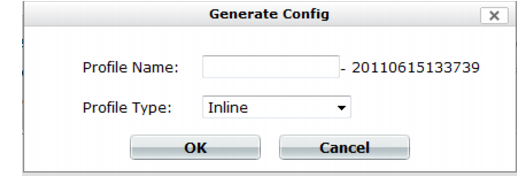
Adjust configuration items used by the generated profile, such as input rules, when necessary. Generated configuration items are based on auto-learning data current at the time that the profile is generated. Data may have changed while you were reviewing the auto-learning report, and/or after you have generated the profiles. |