4. Configure these settings: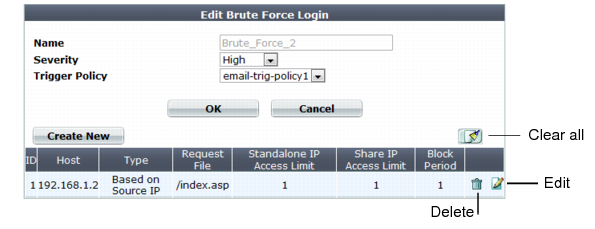
This scan is bypassed if the client’s source IP is a known search engine and you have enabled Allow Known Search Engines. |
If you do not enable detection of shared IP addresses (Shared IP), the second threshold, Share IP Access Limit, will be ignored. |
Setting name | Description |
Name | Type a unique name that can be referenced in other parts of the configuration. Do not use spaces or special characters. The maximum length is 35 characters. |
Severity | When rule violations are recorded in the attack log, each log message contains a Severity Level (severity_level) field. Select which severity level the FortiWeb appliance will use when it logs a violation of the rule: • Low • Medium • High The default value is High. |
Trigger Action | Select which trigger, if any, that the FortiWeb appliance will use when it logs and/or sends an alert email about a violation of the rule. See “Configuring triggers”. |
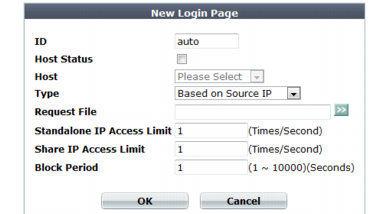
Setting name | Description |
Host Status | Enable to require that the Host: field of the HTTP request match a protected host names entry in order to be included in the brute force login attack profile’s rate calculations. Also configure Host. |
Host | Select which protected host names entry (either a web host name or IP address) that the Host: field of the HTTP request must be in to match the brute force login attack profile. This option is available only if Host Status is enabled. |
Type | Select how to apply the limit of login attempts in Standalone IP Access Limit or Share IP Access Limit, either: • Based on Source IP — Apply the limit to per source IP. • Based on TCP Session — Apply the limit to per TCP/IP session. Tip: If you need to cover both possibilities, create two members. |
Request File | Type the URL that the HTTP/HTTPS request must match to be included in the brute force login attack profile’s rate calculations. When you have finished typing the regular expression, click the >> (test) icon. This opens the Regular Expression Validator window where you can fine-tune the expression (see “Regular expression syntax”). |
Block Period | Type the length of time in seconds for which the FortiWeb appliance will block subsequent requests after a source IP address exceeds the rate threshold in either Standalone IP Access Limit or Share IP Access Limit. The block period is shared by all clients whose traffic originates from the source IP address. The valid range is from 1 to 10,000 seconds. |
Standalone IP Access Limit | Type the rate threshold for source IP addresses that are single clients. Request rates exceeding the threshold will cause the FortiWeb appliance to block additional requests for the length of the time in the Block Period field. To disable the rate limit, type 0. |
Share IP Access Limit | Type the rate threshold for source IP addresses that are shared by multiple clients behind a network address translation (NAT) device such as a firewall or router. Request rates exceeding the threshold will cause the FortiWeb appliance to block additional requests for the length of the time in the Block Period field. To disable the rate limit, type 0. Note: Blocking a shared source IP address could block innocent clients that share the same source IP address with an offending client. In addition, the rate is a total rate for all clients that use the same source IP address. For these reasons, you should usually enter a greater value for this field than for Standalone IP Access Limit. Note: This option will be ignored if you have not enabled detection of shared IP addresses. See “Advanced settings”. |