Grouping all suspicious request URLs
Auto Learn > Predefined Pattern > Suspicious URL groups both custom and predefined suspicious URLs together so that they can be selected in an auto-learning profile.
To configure a suspicious URL pattern group
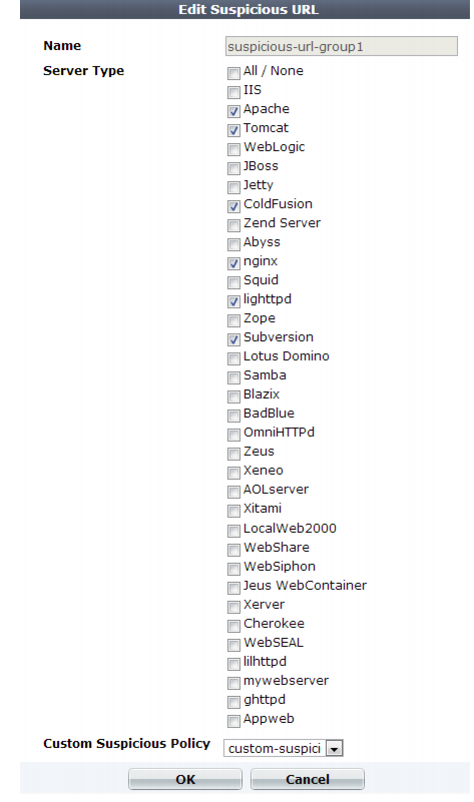
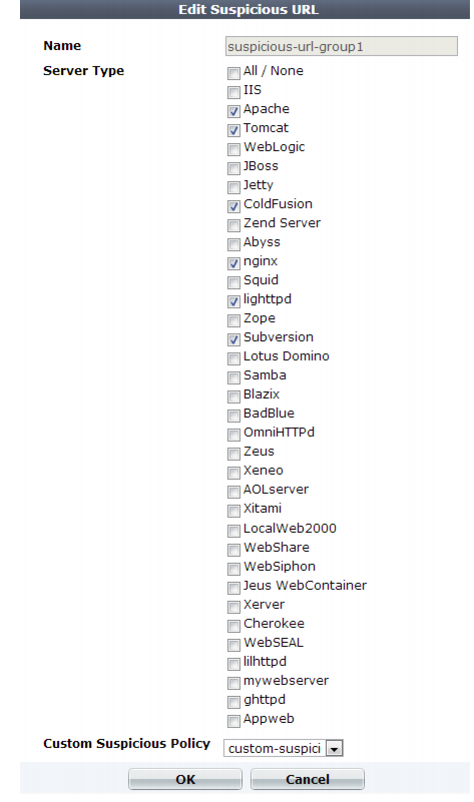
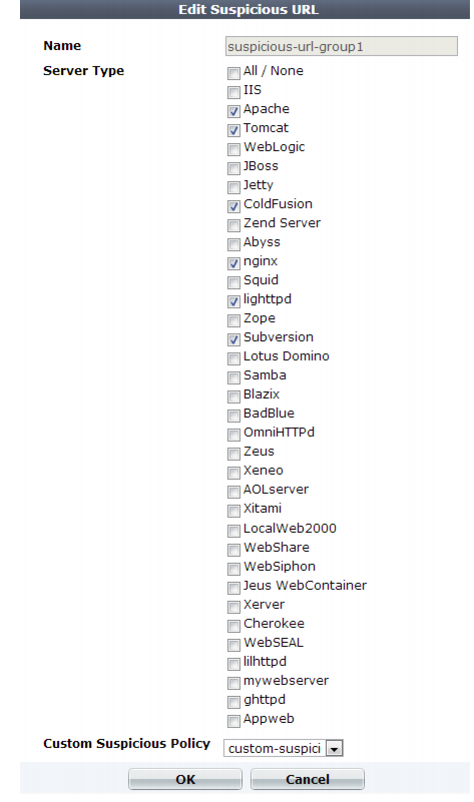
2. Go to Auto Learn > Predefined Pattern > Suspicious URL.
To access this part of the web UI, your administrator's account access profile must have
Read and
Write permission to items in the
Server Policy Configuration category. For details, see
“Permissions”.
3. Click Create New.
Alternatively, to clone an existing pattern as the basis for a new group, mark the check box next to it, then click the Clone icon.
A dialog appears.
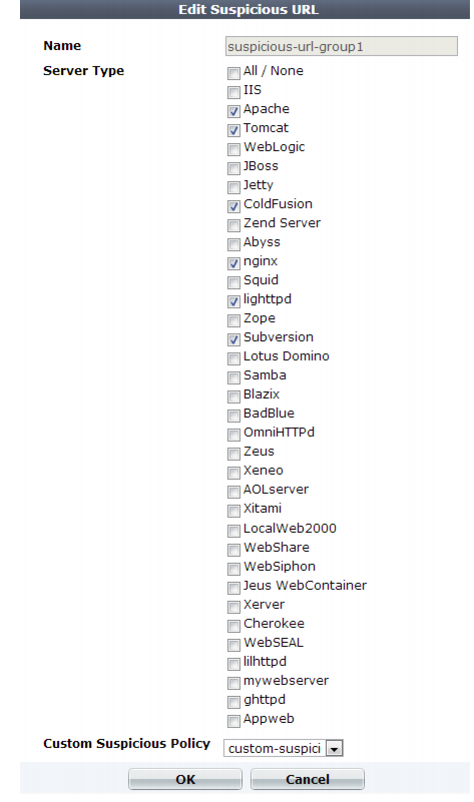
4. In Name, type a unique name that can be referenced by other parts of the configuration. Do not use spaces or special characters. The maximum length is 35 characters.
5. In Server Type, enable one or more of the predefined, web server-specific suspicious URL sets that you want to detect.
To view detailed descriptions of the types of patterns that each suspicious URL type will detect, see
“Predefined suspicious request URLs”.
| If you know that your network’ does not rely on one or more of the listed web server types, disable scans for suspicious access to their administrative URLs in order to improve performance. |
6. From the Custom Suspicious Policy drop-down list, select a group of custom suspicious URLs, that you have configured, if any.
7. Click OK.
See also