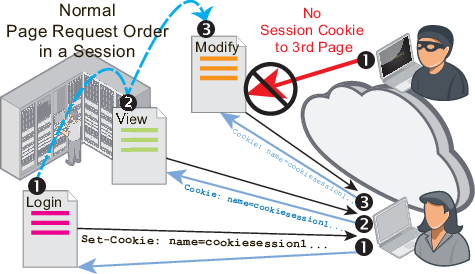
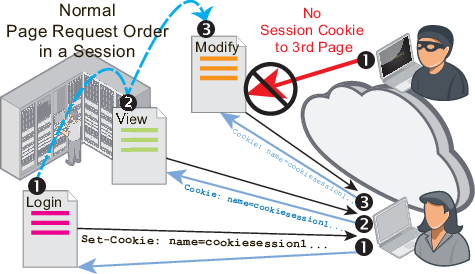
To prevent attackers from exploiting web applications that are vulnerable to state-based attacks, you may need to define legitimate entry points into your web applications.
When you select a start page group in the inline protection profile, clients must begin from a valid start page in order to initiate a valid HTTP session. If they violate this rule, they will wither be logged, blocked, or redirected to one of the valid entry pages (in the web UI, this is called the “default” page).
|
|
All web pages in a start page rule must belong to the same website. Start page rules cannot redirect each violation to a different location, depending on which of the rules was violated. If you choose to redirect violations, all violations will be redirected to the same “default” URL. |
For example, you may insist that HTTP clients of an e-commerce website begin their session from either the main page, an item view, or login. Clients are not allowed to begin a valid session from the third stage of the shopping cart checkout. If someone initiates a session from partway through the shopping cart checkout, it is likely to be an attack. But just in case it was due to a legitimate client clearing the browser’s cookies or clicking a link or bookmark, FortiWeb could redirect the request to one of the valid start pages.
1. Before you configure a start page rule, if you want to apply it only to HTTP requests for a specific real or virtual host, you must first define the web host in a protected host names group. For details, see Defining your protected/allowed HTTP “Host:” header names.
2. Go to Web Protection > Access > Start Pages.
To access this part of the web UI, your administrator’s account access profile must have Read and Write permission to items in the Web Protection Configuration category. For details, see Permissions.
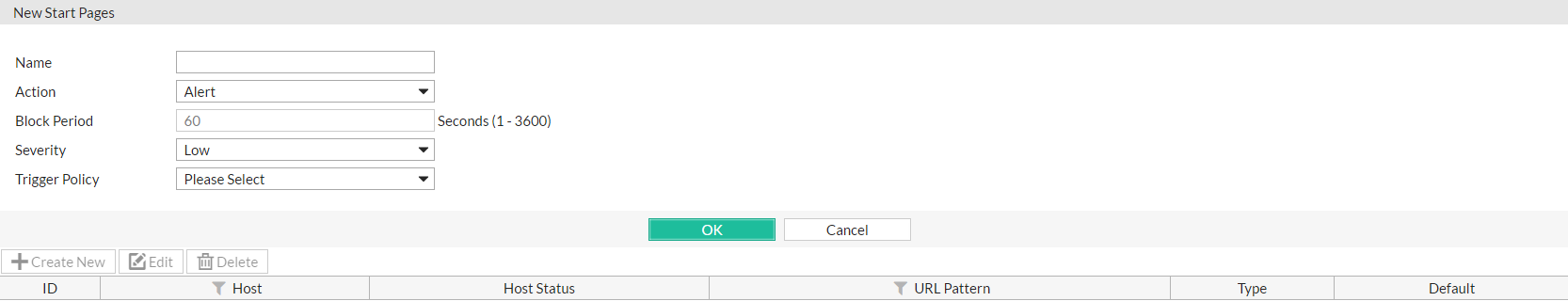
3. Click Create New.
A dialog appears.
4. Configure these settings:
| Setting name | Description |
|---|---|
| Name | Type a unique name that can be referenced in other parts of the configuration. Do not use spaces or special characters. The maximum length is 35 characters. |
| Action |
Select which action the FortiWeb appliance will take when it detects a violation of the rule:
The default value is Alert. Note: This setting will be ignored if Monitor Mode is enabled. Note: Logging and/or alert email will occur only if enabled and configured. See Logging and Alert email. Note: If you will use this rule set with auto-learning, you should select Alert. If Action is Alert & Deny, or any other option that causes the FortiWeb appliance to terminate or modify the request or reply when it detects an attack attempt, the interruption will cause incomplete session information for auto-learning. |
| Block Period |
Type the number of seconds that you want to block subsequent requests from the client after the FortiWeb appliance detects that the client has violated the rule. This setting is available only if Action is set to Period Block. The valid range is from 1 to 3,600 (1 hour). The default value is 1. See also Monitoring currently blocked IPs. |
| Severity |
When rule violations are recorded in the attack log, each log message contains a Severity Level (
The default value is Low. |
| Trigger Policy | Select which trigger, if any, that the FortiWeb appliance will use when it logs and/or sends an alert email about a violation of the rule. See Viewing log messages. |
5. Click OK.
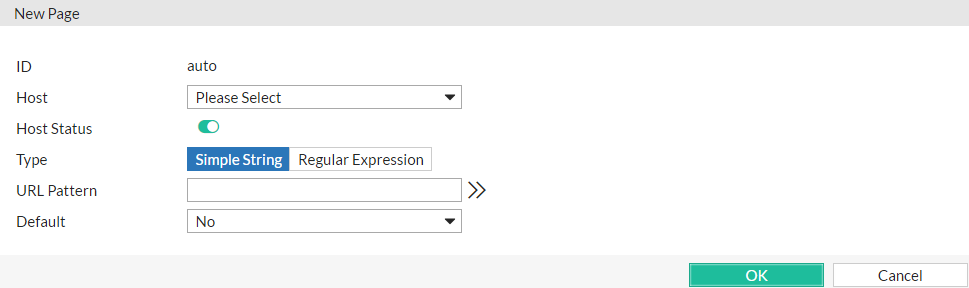
6. Click Create New to add an entry to the set.
A dialog appears.
7. Configure these settings:
| Setting name | Description |
|---|---|
| Host |
Select which protected host names entry (either a web host name or IP address) that the This option is available only if Host Status is enabled. |
| Host Status | Enable to require that the Host: field of the HTTP request match a protected host names entry in order to match a valid start page. Also configure Host. |
| Type |
Select whether URL Pattern is a Simple String (that is, a literal URL such as Note: If Default is Yes, you must select Simple String and provide the exact redirect/session initiation URL in URL Pattern. (A regular expression does not specify a single definite destination, and therefore is not a valid configuration in that case.) |
| URL Pattern |
Depending on your selection in Type, type either:
Do not include the domain name, such as To create and test a regular expression, click the >> (test) icon. This opens the Regular Expression Validator window where you can fine-tune the expression (see Regular expression syntax). |
| Default |
If Action is Redirect, for requests that either:
select Yes if you want FortiWeb to redirect the client to this page, indicated in URL Pattern. (i.e., This URL will be treated as the website’s default/home page.) Otherwise, select No and configure the redirect URL separately from this rule, in the protection profile’s Redirect URL. To prevent the redirect from having more than one possible destination, only one URL in the start page rule can be configured as the “default” at a given time. |
8. Click OK.
9. Repeat the previous steps for each start page that you want to add to the group of start pages.
10. To apply a start page rule:
Attack log messages contain Start Page Violation when this feature detects a start page violation. Additionally, if the start page rule was configured to redirect the attacker, parameters will be appended to the redirect URL to indicate the reason. e.g.:
http://example.com/index.html?redirect491=1&reason747sha=Start%20Page%20Violation
|
|
Because the new active appliance does not know previous session history, after an HA failover, for existing sessions, FortiWeb will not be able to apply this feature. It will apply to new sessions as they are formed. See Sessions & FortiWeb HA. |