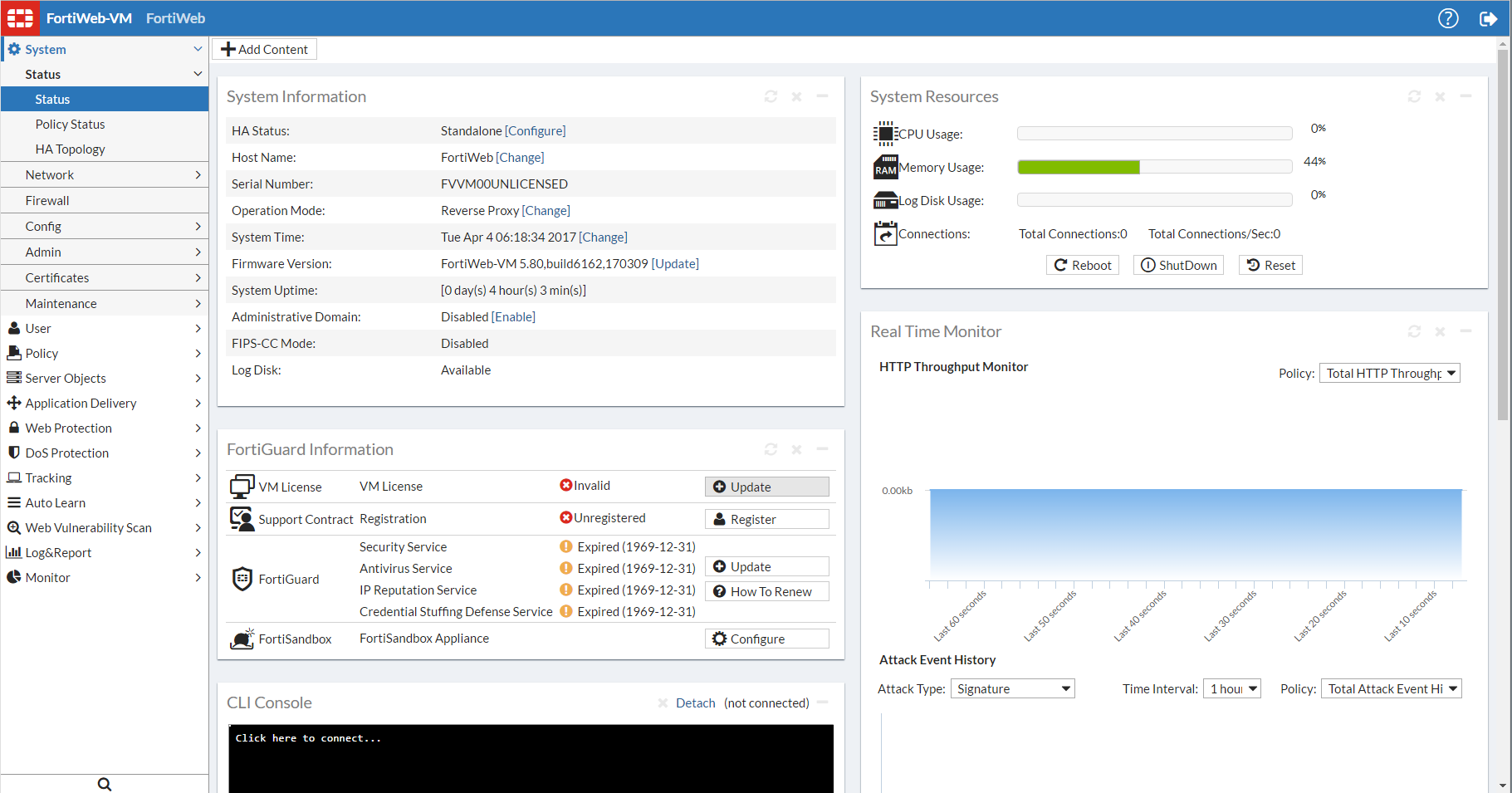
This topic describes aspects that are general to the use of the web UI, a graphical user interface (GUI) that provides access the FortiWeb appliance from within a web browser.
The management computer that you use to access the web UI must have:
To minimize scrolling, the computer’s screen should have a resolution that is a minimum of 1280 x 1024 pixels.
You access the web UI by URL, using a network interface on the FortiWeb appliance that you have configured for administrative access.
For first-time connection, see Connecting to the web UI.
The default URL to access the web UI through the network interface on port1 is:
If the network interfaces were configured during installation of the FortiWeb appliance (see Configuring the network settings), the URL and/or permitted administrative access protocols may no longer be in their default state. In that case, use either a DNS-resolvable domain name for the FortiWeb appliance as the URL, or the IP address that was assigned to the network interface during the installation process.
For example, you might have configured port2 with the IP address 10.0.0.1 and enabled HTTPS. You might have also configured a private DNS server on your network to resolve FortiWeb.example.com to 10.0.0.1. In this case, to access the web UI through port2, you could enter either https://FortiWeb.example.com/ or https://10.0.0.1/.
For information on enabling administrative access protocols and configuring IP addresses for the FortiWeb appliance, see Configuring the network settings.
|
|
If the URL is correct and you still cannot access the web UI, you may also need to configure FortiWeb to accept login attempts for your administrator account from that computer (that is, trusted hosts), and/or static routes. For details, see Administrators and Adding a gateway. |
While the “heart” of your security enforcement on FortiWeb is server policies, its individual settings are specified in rules and exceptions, that are grouped into sets and selected in a profile before being applied to the server policy. Often you will not be able to complete configuration of an item unless you have configured its chain of prerequisites. For that reason, you may want to start with the most granular settings first.
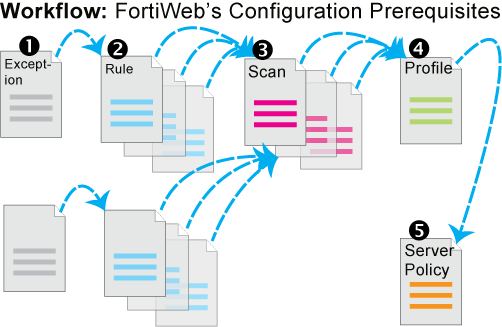
For example, when configuring DoS protection, configuration must occur in this order:
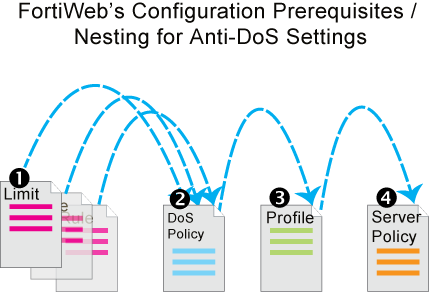
1. Configure anti-DoS settings for each type:
2. Group the settings together into a comprehensive anti-DoS policy (Grouping DoS protection rules).
3. Select the anti-DoS policy in a protection profile, and enable Session Management (Configuring a protection profile for inline topologies).
4. Select the protection profile in a server policy (Configuring a server policy).
Depending on the account that you use to log in to the FortiWeb appliance, you may not have complete access to all CLI commands or areas of the web UI.
Together, both:
control which commands and settings an administrator account can use.
Access profiles assign either:
to each area of the FortiWeb software.
Similar to VDOMs on FortiGate, ADOMs on FortiWeb divide policies and other settings so that they each can be assigned to a different administrators.
| Access profile setting | Grants access to* | |
|---|---|---|
| Admin Users | System > Admin ... except Settings | Web UI |
admingrp
|
config system admin
config system accprofile
|
CLI |
| Auth Users | User ... | Web UI |
authusergrp
|
config user ...
|
CLI |
| Autolearn Configuration | Auto Learn > Auto Learn Profile > Auto Learn Profile | Web UI |
learngrp
|
config server-policy custom-application ...
config waf web-protection-profile autolearning-profile
Note: Because generating an auto-learning profile also generates its required components, this area also confers Write permission to those components in the Web Protection Configuration/ wafgrp area.
|
CLI |
| Log & Report | Log & Report ... | Web UI |
loggrp
|
config log ...
execute formatlogdisk
|
CLI |
| Maintenance | System > Maintenance except System Time tab | Web UI |
mntgrp
|
diagnose system ...
execute backup ...
execute factoryreset
execute rebootexecute restore ...
execute shutdown
diagnose system flash ...
|
CLI |
| Network Configuration | System > Network ... | Web UI |
netgrp
|
config system interface
config system dns
config system v-zone
diagnose network ...exceptsniffer ...
|
CLI |
| Router Configuration | Router ... | Web UI |
routegrp
|
config router ...
|
CLI |
| System Configuration | System ... except Network, Admin, and Maintenance tabs | Web UI |
sysgrp
|
config system except accprofile, admin, dns, interface, and v-zonediagnose hardware ...diagnose network sniffer ...diagnose system ...exceptflash ...execute date ...execute ha ...execute ping ...execute ping-options ...execute traceroute ...execute time ... |
CLI |
| Server Policy Configuration | Policy > Server Policy ... Server Objects ... Application Delivery ... | Web UI |
traroutegrp
|
config server-policy ...except custom-application ...
config waf file-compress-rule
config waf file-uncompress-rule
config waf http-authen ...
config waf url-rewrite ...
diagnose policy ...
|
CLI |
| Web Anti-Defacement Management | Web Anti-Defacement ... | Web UI |
wadgrp
|
config wad ...
|
CLI |
| Web Protection Configuration | Policy > Web Protection ... Web Protection ... DoS Protection ... |
Web UI |
wafgrp
|
config system dos-prevention
config waf except:
|
CLI |
| Web Vulnerability Scan Configuration | Web Vulnerability Scan ... | Web UI |
wvsgrp
|
config wvs ...
|
CLI |
* For each config command, there is an equivalent get/show command, unless otherwise noted.config access requires write permission.get/show access requires read permission.
|
||
Unlike other administrator accounts, the administrator account named admin exists by default and cannot be deleted. The admin administrator account is similar to a root administrator account. This administrator account always has full permission to view and change all FortiWeb configuration options, including viewing and changing all other administrator accounts and ADOMs. Its name and permissions cannot be changed. It is the only administrator account that can reset another administrator’s password without being required to enter that administrator’s existing password.
|
|
Set a strong password for the admin administrator account, and change the password regularly. By default, this administrator account has no password. Failure to maintain the password of the admin administrator account could compromise the security of your FortiWeb appliance. |
For complete access to all commands and abilities, you must log in with the administrator account named admin.
As their name implies, trusted hosts are assumed to be (to a reasonable degree) safe sources of administrative login attempts.
Configuring the trusted hosts of your administrator accounts (Trusted Host #1, Trusted Host #2, and Trusted Host #3) hardens the security of your FortiWeb appliance by further restricting administrative access. In addition to knowing the password, an administrator must connect only from the computer or subnets you specify. The FortiWeb appliance will not allow logins for that account from any other IP addresses. If all administrator accounts are configured with specific trusted hosts, FortiWeb will ignore login attempts from all other computers. This eliminates the risk that FortiWeb could be compromised by a brute force login attack from an untrusted source.
Trusted host definitions apply both to the web UI and to the CLI when accessed through Telnet, SSH, or the CLI Console widget. Local console access is not affected by trusted hosts, as the local console is by definition not remote, and does not occur through the network.
Relatedly, you can white-list trusted end-user IP addresses. End users do not log in to the web UI, but their connections to protected web servers are normally subject to protective scans by FortiWeb unless the clients are trusted. See Blacklisting & whitelisting clients using a source IP or source IP range.
If single administrator mode is enabled, you will not be able to log in while any other account is logged in. You must either wait for the other person to log out, or power cycle the appliance.
For details, see Enable Single Admin User login.
Some settings for connections to the web UI and CLI apply regardless of which administrator account you use to log in.
1. Go to System > Admin > Settings.
To access this part of the web UI, your administrator's account access profile must have Read and Write permission to items in the System Configuration category. For details, see Permissions.
2. Configure these settings: 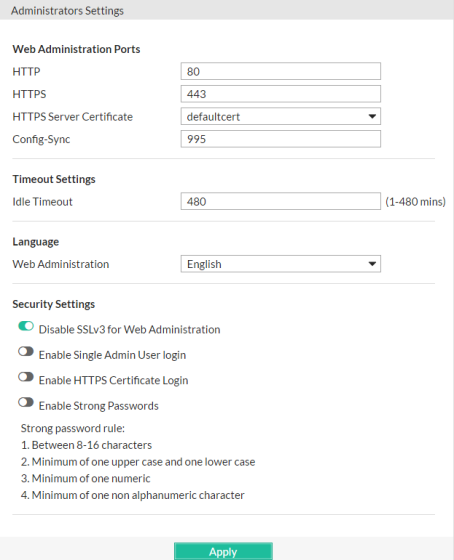
| Setting name | Description | |
|---|---|---|
| Web Administration Ports | ||
| HTTP | Type the TCP port number on which the FortiWeb appliance will listen for HTTP administrative access. The default is 80. This setting has an effect only if HTTP is enabled as an administrative access protocol on at least one network interface. For details, see Configuring the network interfaces. |
|
| HTTPS | Type the TCP port number on which the FortiWeb appliance will listen for HTTPS administrative access. The default is 443. This setting has an effect only if HTTPS is enabled as an administrative access protocol on at least one network interface. For details, see Configuring the network interfaces. |
|
| HTTPS Server Certificate | Select the certificate that FortiWeb uses for secure connections to its Web UI (see How to offload or inspect HTTPS). Certificates that stored in System > Admin > Admin Cert Local (How to change FortiWeb's default certificate) are listed here for options. defaultcert is the Fortinet factory default certificate. | |
| Config-Sync | Type the TCP port number on which the FortiWeb appliance will listen for configuration synchronization requests from the peer/remote FortiWeb appliance. The default is 8333. For details, see Configuring a high availability (HA) FortiWeb cluster. Note: This is not used by HA. See Configuring a high availability (HA) FortiWeb cluster. |
|
| Timeout Settings | ||
| Idle Timeout | Type the number of minutes that a web UI connection can be idle before the administrator must log in again. The maximum is 480 minutes (8 hours). To maintain security, keep the idle timeout at the default value of 5 minutes. | |
| Language | ||
| Web Administration | Select which language to use when displaying the web UI. Languages currently supported by the web UI are: The display’s web pages will use UTF-8 encoding, regardless of which language you choose. UTF-8 supports multiple languages, and allows them to display correctly, even when multiple languages are used on the same web page. For example, your organization could have websites in both English and simplified Chinese. Your FortiWeb administrators prefer to work in the English version of the web UI. They could use the web UI in English while writing rules to match content in both English and simplified Chinese without changing this setting. Both the rules and the web UI will display correctly, as long as all rules were input using UTF-8. Usually, your text input method or your management computer’s operating system should match the display by also using UTF-8. If they do not, your input and the web UI may not display correctly at the same time. For example, your web browser’s or operating system’s default encoding for simplified Chinese input may be GB2312. However, you usually should switch it to be UTF-8 when using the web UI, unless you are writing regular expressions that must match HTTP client’s requests, and those requests use GB2312 encoding. Note: Regular expressions are impacted by language. For more information, see Language support. Note: This setting does not affect the display of the CLI. |
|
| Security Settings | ||
| Disable SSLv3 for Web Administration | Enable to protect against a POODLE (Padding Oracle On Downgraded Legacy Encryption) attack by preventing access to the FortiWeb web UI via SSL 3.0. | |
| Enable Single Admin User login | To prevent inadvertent configuration overwrites or conflicts, enable to allow only one session from one administrator account to be logged in at any given time. If a second administrator attempts to log in while another administrator is already logged in (or if the same administrator attempts to start a second concurrent session), the second administrator will receive an error message:Too many bad login attempts or reached max number of logins. Please try again in a few minutes. Login aborted.When multiple administrators simultaneously modify the same part of the configuration, they each edit a copy of the current, saved state of the configuration. As each administrator makes changes, FortiWeb does not update the other administrators’ working copies. Each administrator may therefore make conflicting changes without being aware of the other. The FortiWeb appliance will only use whichever administrator’s configuration is saved last. If only one administrator can log in, this problem cannot occur. Disable to allow multiple administrators to be logged in. In this case, administrators should communicate with each other to avoid overwriting each other’s changes. |
|
| Enable HTTPS Certificate Login | Enable the option to let FortiWeb operates with only certificate-based authentication for Web UI accesses. If this option is enable, username/password authentication will be disabled. Please see Certificate-based Web UI login for details. | |
| Enable Strong Passwords | Enable to enforce strong password rules for administrator accounts. If the password entered is not strong enough when a new administrator account is created, an error message appears and you are prompted to re-enter a stronger password. Strong passwords have the following characteristics:
|
|
3. Click Apply.
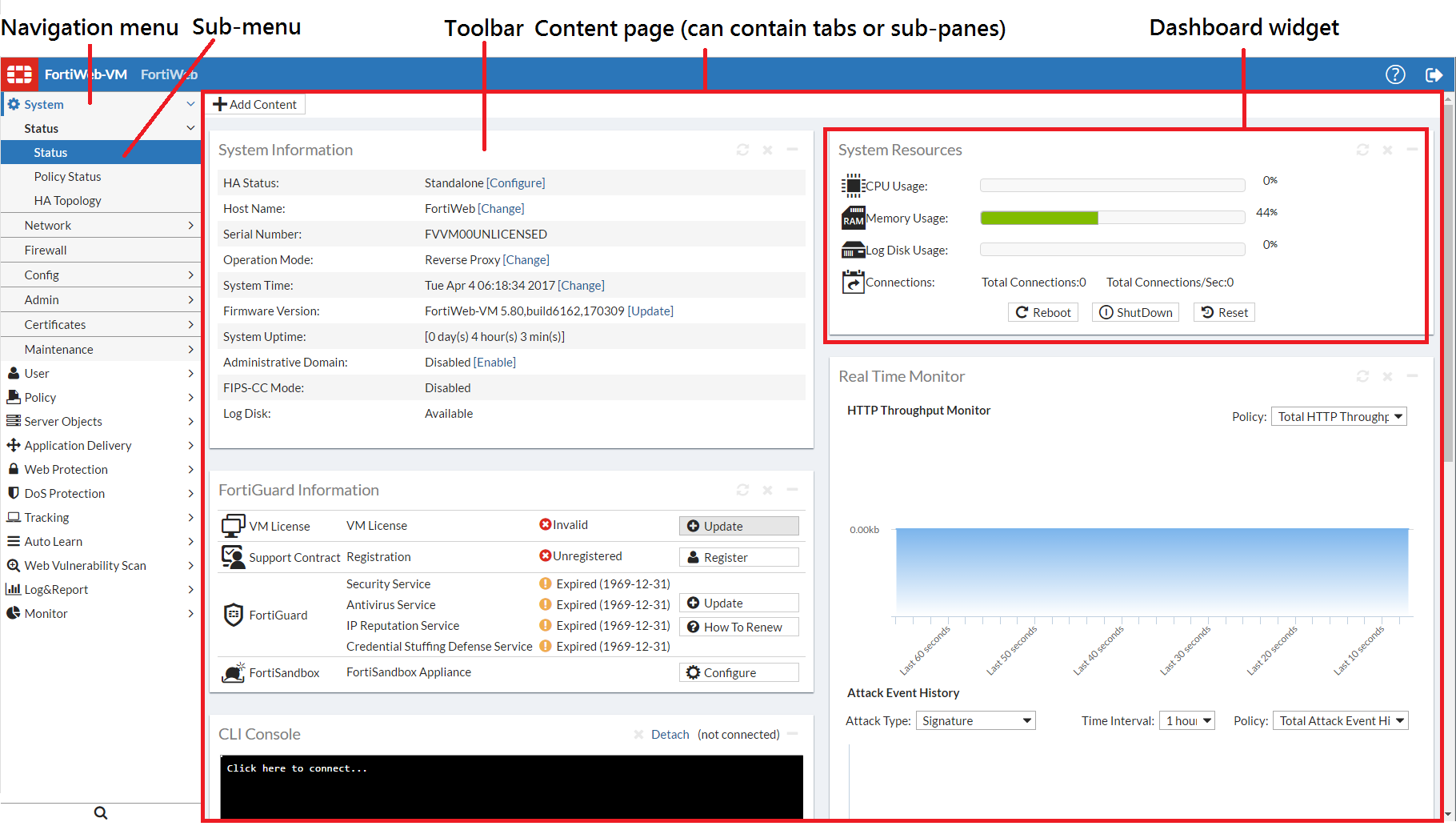
A navigation menu is located on the left side of the web UI. To expand a menu item, simply click it. To expand a submenu item click the > button located next to the submenu name, or click the submenu name itself. To view the pages located within a submenu, click the name of the page.
|
|
Do not use your browser’s Back button to navigate — pages may not operate correctly. Instead, use the navigation menu, tabs, and buttons within the pages of the web UI. |
To expand or collapse an area of the menu, click the name of the area itself. Within each area may be multiple submenus. To expand or collapse a submenu, click the > or v button next to the submenu name, or click the name of the submenu itself.
Within each submenu may be one or more tabs or sub-panes, which are displayed to the right of the navigation menu, in the content pane. At the top of the content pane is a toolbar. The toolbar contains buttons that enable you to perform operations on items displayed in the content pane, such as importing or deleting entries.
Each tab or pane (per Permissions) displays or allows you to modify settings, using a similar set of buttons.
| Icon | Description |
|---|---|
|
|
Click to collapse a visible area. |
|
|
Click to expand a hidden area. |
|
|
Click to view the first page’s worth of records within the tab. or pane. If this button is grey, you are already viewing the first page. |
|
|
Click to view the previous page’s worth of records within the tab or pane. If this button is grey, you are viewing the first page. |
|
|
To go to a specific page number, type the page number in the field and press Enter. The total number of pages depends on the number of records per page. |
|
|
Click to view the next page’s worth of records within the tab or pane. If this button is grey, you are viewing the last page. |
|
|
Click to view the last page’s worth of records within the tab or pane. If this button is gray, you are already viewing the last page. |
|
|
Click to create a new entry using only typical default values as a starting point. |
|
|
Click to create a new entry by duplicating an existing entry. To use this button, you must first mark a check box to select an existing entry upon which the new entry will be based. |
|
|
Click to modify an existing entry. To use this button, you must first select which existing entry you want to modify. Alternatively, you can double-click the existing entry, or right-click the entry and select Edit. |
|
|
Click to remove an existing entry. To use this button, you must first mark a check box to select which existing entry you want to remove. To delete multiple entries, either mark the check boxes of each entry that you want to delete, then click Delete. This button may not always be available. See Deleting entries. |
Common buttons are not described in subsequent sections of this guide.
Some pages have unique buttons, or special behaviors associated with common buttons. Those buttons are described in their corresponding section of this guide.
To delete a part of the configuration, you must first remove all references to it.
For example, if you selected a profile named “Profile1” in a policy named “PolicyA”, that policy references “Profile1” and requires it to exist. Therefore the appliance will not allow you to delete “Profile1” until you have reconfigured “PolicyA” (and any other references) so that “Profile1” is no longer required and may be safely deleted.
|
|
Back up the configuration before deleting any part of the configuration. Deleted items cannot be recovered unless you upload a backup copy of the previous configuration. See Backups and Restoring a previous configuration. |
|
|
If you do not know where your configuration refers to the entry that you want to delete, to find the references, you can download a backup of the configuration and use a plain text editor to search for the entry’s name. |
|
|
Predefined entries included with the firmware cannot be deleted. |
In the web UI, each entry’s name is not editable after you create and save it.
For example, let’s say you create a policy whose Name is “PolicyA”. While configuring the policy, you change your mind about the policy’s name a few times, and ultimately you change the Name to “Blog-Policy”. Finally, you click OK to save the policy. Afterwards, if you edit the policy, most settings can be changed. However, Name is greyed-out, and cannot any longer be changed.
While you cannot edit Name, you can achieve the same effect by other means.
|
|
Alternatively, if you need to rename an item that is only referenced in the core configuration file, you can download a backup copy, use a plain text editor to find and replace the entry’s old name, then restore the modified configuration backup file to the appliance. Where there are many references, this may save time. |
1. Clone the entry, supplying the new name.
2. In all areas of the configuration that refer to the old name, replace the old entry name by selecting the new name.
|
|
If you do not know where your configuration refers to the entry that you want to delete, to find the references, you can download a backup of the configuration and use a plain text editor to search for the entry’s name. |
3. Delete the item with the old name.
Always properly shut down the FortiWeb appliance’s operating system before turning off the power switch or unplugging it. This causes it to finish writing any buffered data, and to correctly spin down and park the hard disks.
|
|
Do not unplug or switch off the FortiWeb appliance without first halting the operating system. Failure to do so could cause data loss and hardware damage. |
1. Access the CLI or web UI. For details, see Connecting to the web UI or CLI.
2. From the CLI console, enter the following command:
Alternatively, if you are connected to the web UI, go to System > Status > Status, and in the Operation widget, click Shut Down.
You may be able to hear the appliance become more quiet when the appliance halts its hardware and operating system, indicating that power can be safely disconnected.
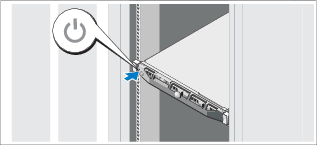
3. For hardware appliances, press the power button if there is one. Power supplies and switches vary by hardware model. On some, you will press the power button. On others, you will flip the switch to either the off (O) or on (I) position. When power is connected and the hardware is started, the power indicator LEDs should light. For details, see the LED specifications in the QuickStart Guide for your model.
For FortiWeb-VM, in the hypervisor or VM manager, power off the virtual machine.
4. Disconnect the power cable from the power supply.