What if you want to allow a web crawler, but only if it is not too demanding, and comes from a source IP that is known to be legitimate for that crawler? What if you want to allow only a client that is a senior manager’s IP, and only if it hasn’t been infected by malware whose access rate is contributing to a DoS?
Advanced access control rules provide a degree of flexibility for these types of complex conditions. You can combine any or all of these criteria:
You use the rule's filters to specify all criteria that you require allowed traffic to match.
The filters apply to request traffic only, with the following exceptions:
FortiWeb includes predefined rules that defend against some popular attacks. You cannot edit these predefined rules, but you can view their settings or create duplicates of them that you can edit (that is, by cloning).
|
|
Advanced access control is available even if FortiWeb derives client source IP addresses from the X-header field (see Defining your proxies, clients, & X-headers on page 278). For example, if FortiWeb is deployed behind a load balancer or other web proxy that applies source NAT. |
1. Go to Web Protection > Advanced Protection > Custom Rule.
To access this part of the web UI, your administrator’s account access profile must have Read and Write permission to items in the Web Protection Configuration category. For details, see Permissions.
2. Do one of the following:
A dialog appears.
3. If you are cloning a predefined rule, enter a name for your new rule, and then click OK. To edit or review the rule settings, select the rule, and then click Edit.
4. Configure these settings:
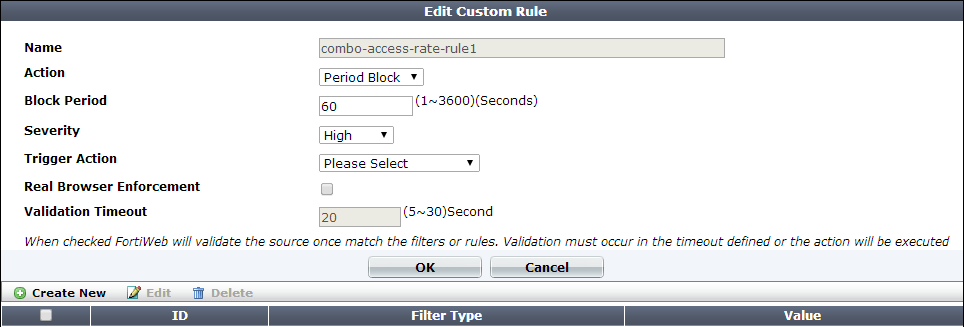
| Setting name | Description |
|---|---|
| Name | Type a unique name that can be referenced in other parts of the configuration. Do not use spaces or special characters. The maximum length is 35 characters. |
| Action |
Select which action the FortiWeb appliance will take when it detects a violation of the rule:
The default value is Alert. Caution: This setting is ignored when Monitor Mode is enabled. Note: Logging and/or alert email will occur only if enabled and configured. See Logging and Alert email. |
| Block Period |
Type the number of seconds that you want to block subsequent requests from the client after the FortiWeb appliance detects that the client has violated the rule. This setting is available only if Action is set to Period Block. The valid range is from 1 to 3,600 (1 hour). The default value is 60. See also Monitoring currently blocked IPs. |
| Severity |
When rule violations are recorded in the attack log, each log message contains a Severity Level (
The default value is Medium. |
| Trigger Action | Select which trigger, if any, that the FortiWeb appliance will use when it logs and/or sends an alert email about a violation of the rule. See Viewing log messages. |
| Real Browser Enforcement | Specifies whether FortiWeb returns a JavaScript to the client to test whether it is a web browser or automated tool when it meets any of the specified conditions. If the client fails the test or does not return results before the Validation Timeout expires, FortiWeb applies the Action. If the client appears to be a web browser, FortiWeb allows the client to exceed the action. See also Bot analysis. |
| Validation Timeout | Enter the maximum amount of time that FortiWeb waits for results from the client for Real Browser Enforcement. |
5. Click OK.
6. Click Create New to add an entry to the set.
A dialog appears.
7. From Filter Type, select one of the following conditions that a request must match in order to be allowed, then click OK.
The Filter Type value determines which settings are displayed in the next dialog box.
Source IPv4/IPv6 — Type the IP address of a client that is allowed. Depending on your configuration of how FortiWeb derives the client’s IP (see Defining your proxies, clients, & X-headers), this may be the IP address that is indicated in an HTTP header rather than the IP header.
To enter an address range, enter the first and last address in the range separated by a hyphen. For example, for an IPv4 address, enter 1.2.3.4-1.2.3.40. For an IPv6 address, enter 2001::1-2001::100.
User — Enter a user name to match, and then specify whether the condition matches if the request contains the specified user name or matches only for user names other than the specified one.
Note: This type of filter requires you to select a user tracking policy in any protection profile that uses this advanced access policy. See Tracking users.
/index\.jsp. Do not include the host name. |
|
To accept requests that do not match the URL, do not precede the URL with an exclamation mark ( ! ). Use the CLI to configure the reverse-match {no | yes} setting for this filter. For details, see the FortiWeb CLI Reference. |
HTTP Header — Indicate a single HTTP Header Name such as Host:,and all or part of its value in Header Value. The request matches the condition if that header contains your exact value or matches your regular expression (depending on whether you have selected Simple String or Regular Expression). Value matching is case sensitive.
If you select Header Value Reverse Match, the request matches the condition if the header does not contain the exact value or regular expression.
|
|
To prevent accidental matches, specify as much of the header’s value as possible. Do not use an ambiguous substring. For example, entering the value
|
Access Rate Limit — This is the number of requests per second per client IP. Depending on your configuration of how FortiWeb will derive the client’s IP (see Defining your proxies, clients, & X-headers), this may be the IP address that is indicated in an HTTP header rather than the IP header.
You can add only one Access Rate Limit filter to each rule.
To use one of these categories in an advanced access control rule, enable the corresponding item in your signatures configuration. For more information, see Blocking known attacks & data leaks.
404 or 500-503. To specify more than one response code or range, create additional HTTP Response Code filters.To measure by client, select User.
Note: The User option requires you to enable the Session Management option in your protection profile. For more information, see Configuring a protection profile for inline topologies.
8. Click OK to exit the sub-dialog and return to the rule configuration.
9. Repeat the previous steps for each individual criteria that you want to add to the access rule.
For example, you can require both a matching request URL, HTTP header, and client source IP in order to allow a request.
You can add only one Access Rate Limit filter to each rule.
10. Click OK to save the rule.
11. Go to Web Protection > Advanced Protection > Custom Policy.
12. Click Create New. Group the advanced access rules into a policy.
For example, to create a policy that allows rate-limited access by 3 client IPs, you would group the corresponding 3 advanced access rules for each of those IPs into the policy.
In Priority, enter the priority for each rule in relation to other defined rules. Rules with lower numbers (higher priority) are applied first.
13. To apply the advanced access policy, select it as the Custom Policy in a protection profile (see Configuring a protection profile for inline topologies or Configuring a protection profile for an out-of-band topology or asynchronous mode of operation).
Attack log messages contain Custom Access Violation when this feature detects an unauthorized access attempt.