Figure 128: Administrator user configuration page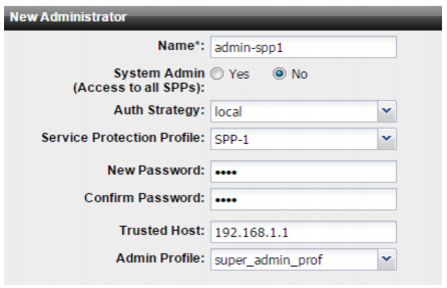
Settings | Guidelines |
Name | Name of the administrator account, such as admin1 or admin@example.com, that can be referenced in other parts of the configuration. Do not use spaces or special characters except the ‘at’ symbol ( @ ). The maximum length is 35 characters. If you use RADIUS authentication, this is the username stored in the RADIUS authentication server. Note: This is the user name that the administrator must provide when logging in to the CLI or web UI. |
System Admin | • Yes—Administrator for all SPPs. • No—Administrator for the selected SPP only. |
Auth Strategy | • Local—Use the local authentication server. When you use the local authentication server, you also configure a password. • RADIUS—Authenticate against a RADIUS server. When you use RADIUS, you do not configure a password. The system authenticates against the username and password stored in the RADIUS server. |
Service Protection Profile | If this administrator is not a system administrator, select the profile that this account manages. |
New Password | Type a password for the administrator account. Passwords may have a maximum of 16 characters, may include numbers, upper and lowercase characters, and the following special characters: _ (underscore), - (hyphen), !, @, #, $, %, ^, &, * |
Confirm Password | Type the password again to confirm its spelling. |
Trusted Host | Source IP address and netmask from which the administrator is allowed to log in. For multiple addresses, separate each entry with a space. You can specify up to three trusted areas. They can be single hosts, subnets, or a mixture. Configuring trusted hosts hardens the security of the system. In addition to knowing the password, an administrator must connect only from the computer or subnets you specify. Trusted host definitions apply both to the web UI and to the CLI when accessed through Telnet, SSH, or the CLI console widget. Local console access is not affected by trusted hosts, as the local console is by definition not remote, and does not occur through the network. If ping is enabled, the address you specify here is also a source IP address to which the system will respond when it receives a ping or traceroute signal. To allow logins only from one computer, enter only its IP address and 32- or 128-bit netmask: 192.0.2.2/32 2001:0db8:85a3:::8a2e:0370:7334/128 To allow login attempts from any IP address (not recommended), enter: 0.0.0.0/0.0.0.0. Caution: If you restrict trusted hosts, do so for all administrator accounts. Failure to do so means that all accounts are still exposed to the risk of brute force login attacks. This is because if you leave even one administrator account unrestricted (i.e. 0.0.0.0/0), the system must allow login attempts on all network interfaces where remote administrative protocols are enabled, and wait until after a login attempt has been received in order to check that user name’s trusted hosts list. Tip: If you allow login from the Internet, set a longer and more complex password, and enable only secure administrative access protocols. We also recommend that you restrict trusted hosts to IPs in your administrator’s geographical area. Tip: For improved security, restrict all trusted host addresses to single IP addresses of computer(s) from which only this administrator will log in. |
Admin Profile | Select a user-defined or predefined profile. The predefined profile named super_admin_prof is a special access profile used by the admin account. However, selecting this access profile will not confer all permissions of the admin account. For example, the new administrator would not be able to reset lost administrator passwords. Note: This option does not appear for the admin administrator account, which by definition always uses the super_admin_prof access profile. |
CLI commands: config system admin edit admin set access-profile super_admin_prof next edit admin-spp1 set is-system-admin no set domain SPP-1 set password ENC $1$0b721b38$vk7GoO147JXXqy5B3ag8z/ set access-profile admin end |