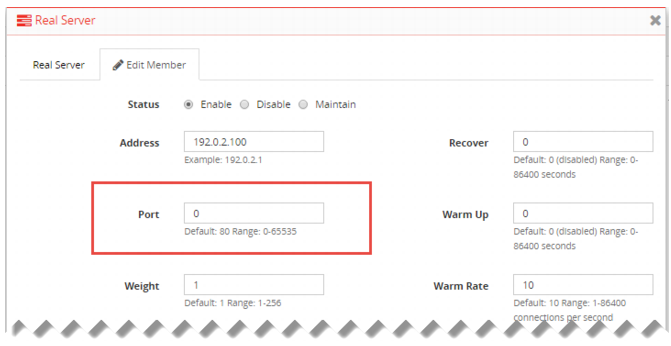
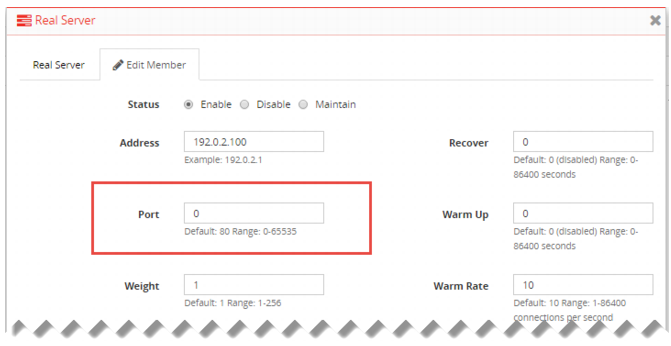
Figure 24: Real server port 0 configuration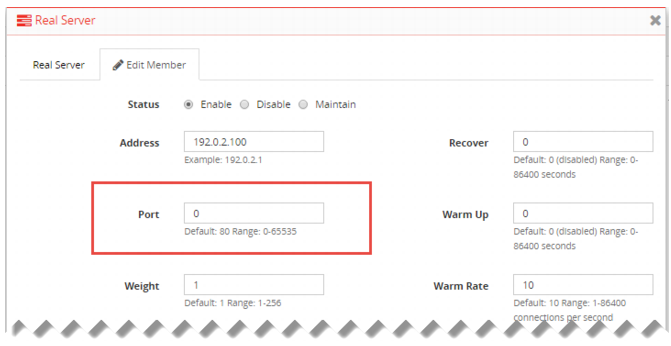
Settings | Guidelines |
Pool | |
Name | Configuration name. Valid characters are A-Z, a-z, 0-9, _, and -. No spaces. You reference this name in the virtual server configuration. Note: After you initially save the configuration, you cannot edit the name. |
Address Type | • IPv4 • IPv6 |
Health Check | Enable health checking for the pool. You can override this for individual servers in the pool. |
Health Check Relationship | • AND—All of the selected health checks must pass for the server to the considered available. • OR—One of the selected health checks must pass for the server to be considered available. |
Health Check List | Select one or more health check configuration objects. |
Member | |
Status | • Enable—The server can receive new sessions. • Disable—The server does not receive new sessions and closes any current sessions as soon as possible. • Maintain—The server does not receive new sessions but maintains any current connections. |
Address | Backend server IP address. In a Layer 2 virtual server deployment, specify the IP address of the next hop to the destination server. Configure a pseudo default gateway in the static route since Layer 2 virtual servers need to use this default route internally to match all the destinations that the client wants to access. However, this default gateway is not used because the next hop is the pool member and not the pseudo gateway. In a Layer 2 virtual server deployment, ensure the backend servers have been configured to route responses through the FortiADC IP address. |
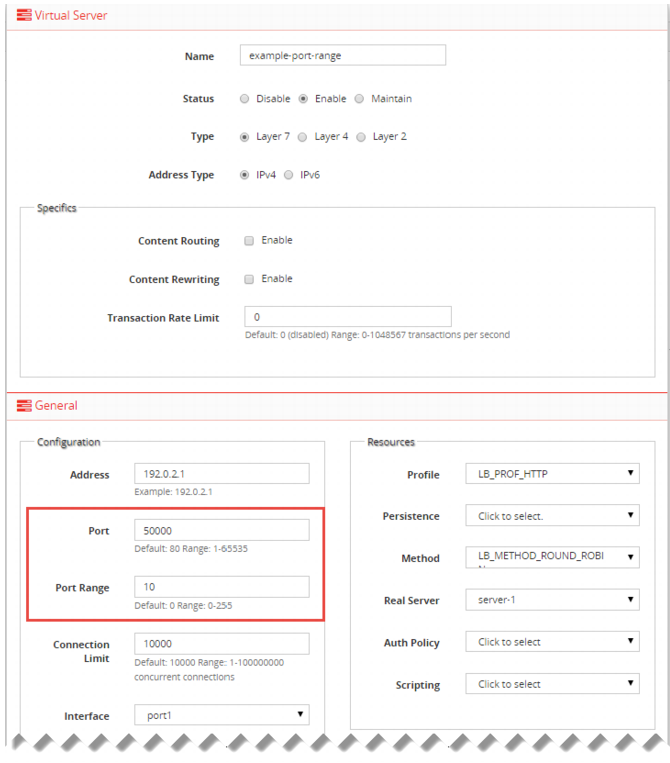
Port | Backend server listening port number. Usually HTTP is 80, HTTPS is 443, FTP is 21, SMTP is 25, DNS is 53, POP3 is 110, IMAP4 is 143, RADIUS is 1812, and SNMP is 161. Tip: The system handles port 0 as a “wildcard” port. When configured to use port 0, the system uses the destination port from the client request. For example, if you specify 0, and the destination port in the client request is 50000, the traffic is forwarded to port 50000. |
Weight | Assigns relative preference among members—higher values are more preferred and are assigned connections more frequently. The default is 1. The valid range is 1 to 256. All load balancing methods consider weight. Servers are dispatched requests proportional to their weight, relative to the sum of all weights. The following example shows the effect of weight on Round Robin: Sever A, Weight 2; Server B, Weight 1: Requests are sent AABAAB. Sever A, Weight 3; Server B, Weight 2: Requests are sent AABAB. For other methods, weight functions as a tie-breaker. For example, with the Least Connection algorithm, requests are sent to the server with the least connections. If the number of connections is equal, the request is sent to the server with the greater weight. For example: Server A, Weight 1, 1 connection Server B, Weight 2, 1 connection The next request is sent to Server B. |
Connection Limit | Maximum number of concurrent connections to the backend server. The default is 0 (disabled). The valid range is 1 to 1,048,576 concurrent connections. Note: Connection Limit is not supported for FTP servers. |
Connection Rate Limit | Limit the number of new connections per second to this server. The default is 0 (disabled). The valid range is 1 to 86,400 connections per second. In Layer 4 deployments, you can apply a connection rate limit per real server and per virtual server. Both limits are enforced. Note: The connection rate limit applies only when the real servers belong to a Layer 4 virtual server. If you add a real server pool with this setting configured to a Layer 7 virtual server, for example, the setting is ignored. Note: Connection Rate Limit is not supported for FTP servers. |
Health Check Inherit | Use the pool's health check settings. Disable to override those settings by selecting a different health check to use with this individual backend server. |
Health Check | Enable health checking for this server. |
Health Check Relationship | • AND—All of the selected health checks must pass for the server to the considered available. • OR—One of the selected health checks must pass for the server to be considered available. |
Health Check List | Select one or more health check configuration objects. Shift-click to select multiple objects. |
Recover | Seconds to postpone forwarding traffic after downtime, when a health check indicates that this server has become available again. The default is 0 (disabled). The valid range is 1 to 86,400 seconds. After the recovery period elapses, the FortiADC assigns connections at the warm rate. Examples of when the server experiences a recovery and warm-up period: • A server is coming back online after the health check monitor detected it was down. • A network service is brought up before other daemons have finished initializing and therefore the server is using more CPU and memory resources than when startup is complete. To avoid connection problems, specify the separate warm-up rate, recovery rate, or both. Tip: During scheduled maintenance, you can also manually apply these limits by setting Status to Maintenance instead of Enable. |
Warm Up | If the server cannot initially handle full connection load when it begins to respond to health checks (for example, if it begins to respond when startup is not fully complete), indicate how long to forward traffic at a lesser rate. The default is 0 (disabled). The valid range is 1 to 86,400 seconds. |
Warm Rate | Maximum connection rate while the server is starting up. The default is 10 connections per second. The valid range is 1 to 86,400 connections per second. The warm up calibration is useful with servers that have the network service brought up before other daemons have finished initializing. As the servers are brought online, CPU and memory are more utilized than they are during normal operation. For these servers, you define separate rates based on warm-up and recovery behavior. For example, if Warm Up is 5 and Warm Rate is 2, the number of allowed new connections increases at the following rate: • 1st second—Total of 2 new connections allowed (0+2). • 2nd second—2 new connections added for a total of 4 new connections allowed (2+2). • 3rd second—2 new connections added for a total of 6 new connections allowed (4+2). • 4th second—2 new connections added for a total of 8 new connections allowed (6+2). • 5th second—2 new connections added for a total of 10 new connections allowed (8+2). |
Cookie | Cookie name to be used for Layer 7 session persistence. The cookie is used to create a FortiADC session ID, which enables the system to forward subsequent related requests to the same backend server. The default is cookie. |
SSL | Use SSL/TLS for the connection between the FortiADC and the real server. Content routing and rewriting requires SSL decryption. In some cases, you might want to re-encrypt traffic before forwarding it to the backend servers. For example, if you are load balancing traffic and forwarding to backend servers along untrusted paths, vital credit card and personally identifying information would be vulnerable during its backend transit unless you re-encrypt it. Verify that your backend servers are configured for encrypted connections. If they are not, the connection will fail. Conversely, if you do not enable SSL to Server, you should also disable SSL/TLS on your servers. |
Backup | Server that the ADC directs traffic to only when other servers in the pool are down. The backup server receives connections when all the other pool members fail the health check or you have manually disabled them, for example. |