A cookie security policy allows you to configure FortiWeb features that prevent cookie-based attacks and apply them in a protection profile. For example, a policy can enable cookie poisoning detection, encrypt the cookies issued by a back-end server, and add security attributes to cookies.
|
|
When you first introduce some of the cookie security features, cookies that client browsers have cached earlier can generate false positives. To avoid this problem, use the Allow Suspicious Cookies setting to either take no action against violations of the cookie security features or delay taking action until a specific date. |
1. Go to Web Protection > Cookie Security.
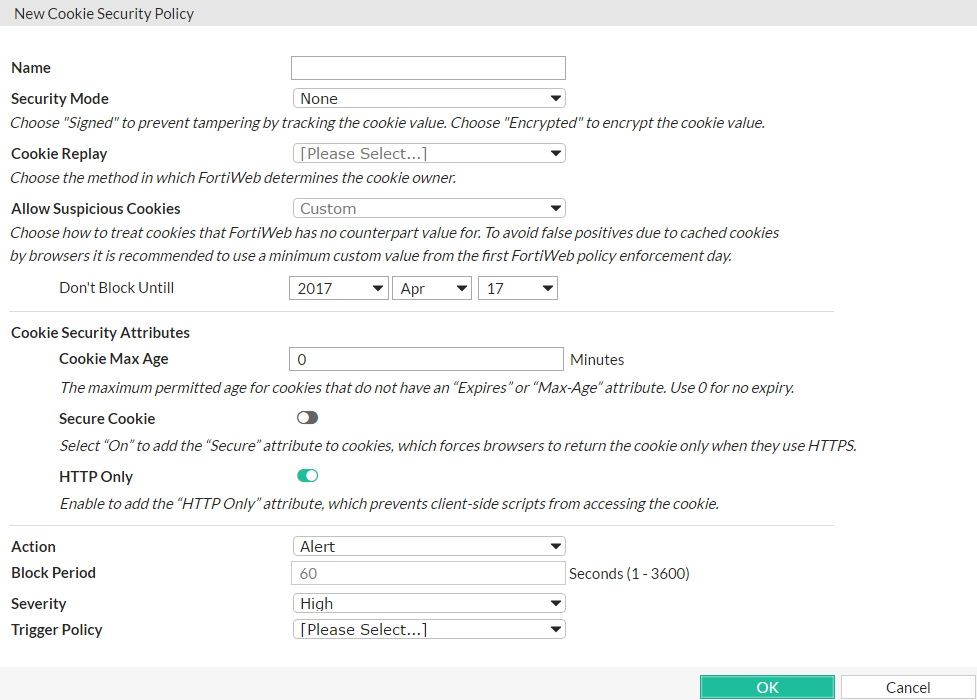
2. Click Create New and complete the following settings:
| Setting name | Description | |
|---|---|---|
| Name | Enter a name that identifies the policy when you select it in a protection profile. | |
| Security Mode |
|
|
| Cookie Replay |
Optionally, select whether FortiWeb uses the IP address of a request to determine the owner of the cookie. Note: This is available only when Security Mode is configured as Encrypted. |
|
| Allow Suspicious Cookies |
Select whether FortiWeb allows requests that contain cookies that it does not recognize or that are missing cookies.
In many cases, when you first introduce the cookie security features, cookies that client browsers have cached earlier generate false positives. To avoid this problem, either select Never, or select Custom and enter an appropriate date on which to start taking the specified action against suspicious cookies.
This feature is not available if Security Mode is Signed or None. |
|
| Don't Block Until | If Allow Suspicious Cookies is Custom, enter the date on which FortiWeb starts to take the specified action against suspicious cookies. | |
| Cookie Security Attributes | ||
| Cookie Max Age | Enter the maximum age (in minutes) permitted for cookies that do not have an “Expires” or “Max-Age” attribute. To configure no expiry age for cookies, enter 0. |
|
| Secure Cookie | Enable to add the secure flag to cookies, which forces browsers to return the cookie only when the request is for an HTTPS page. | |
| HTTP Only |
Enable to add the "HTTP Only" flag to cookies, which prevents client-side scripts from accessing the cookie. Warning: enabling this feature may break web applications that use cookies. |
|
| Action |
For cookie security features that trigger an action, select the action that FortiWeb takes:
|
|
| Block Period | When Action is Period Block, the number of seconds that FortiWeb blocks requests that have violated cookie security features. | |
| Severity | Select the severity level FortiWeb uses when it logs a violation of a cookie security feature. | |
| Trigger Policy | Select the trigger policy FortiWeb uses when it logs a violation of a cookie security feature. | |
3. Click OK.
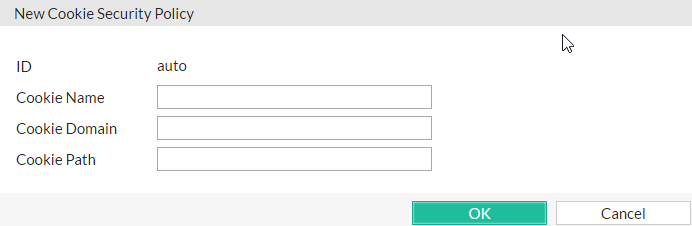
4. If you want to specify cookies that are exempt from the cookie security policy, under the Cookie Exceptions Table, click Create New and complete the following settings:
5.
| Setting name | Description | |
|---|---|---|
| Cookie Name | Enter the name of the cookie, such as NID. |
|
| Cookie Domain |
Optionally, enter the partial or complete domain name or IP address as it appears in the cookie. For example:
If clients sometimes access the back-end server via IP address instead of DNS, create exemption items for both. |
|
| Cookie Path | Optionally, enter the path as it appears in the cookie, such as / or /blog/folder. |
|
6. To apply the cookie security policy, select it in an inline protection profile (see Configuring a protection profile for inline topologies).
If Security Mode is Signed, ensure that Session Management is enabled for the profile.