Configuring Windows Agent
Starting with version 3.0, Windows Agents can be configured and managed from the FortiSIEM Supervisor node. Windows Agent Manager is not required.
Before proceeding, follow the instructions in the Windows Agent Installation Guide to complete these steps:
- Install the Windows Agent using the correct installation file.
- Make sure the Agent appears in the CMDB page of the FortiSIEM GUI, using the host name defined in the installation file.
- Configure the Windows Server to receive the types logs of interest (see Configuring Windows Servers for FortiSIEM Agents in the Windows Agent Installation Guide).
To receive logs from Windows Agent, you must complete the following steps:
Once these steps are completed, the Supervisor node will distribute monitoring policies to the Agents and you will be able to see events in FortiSIEM.
This section also covers these topics:
- Viewing Agent Status
- Enabling or Disabling an Agent
- Viewing Files in FortiSIEM
- Verifying Events in FortiSIEM
- Sample Windows Agent Logs
- Agent Troubleshooting Notes
Define the Windows Agent Monitor Templates
A Windows Monitoring Template consists of:
- Log Settings: Windows Event Logs and Log Files
- Change Settings: File Integrity Monitoring, Registry Changes, Installed Software Changes, Removable media
- Script Settings: WMI Classes and PowerShell Scripts
Complete these steps to add a Windows Agent Monitor Template:
- Go to ADMIN > Setup > Windows Agent tab.
- Click New under the section Windows Agent Monitor Templates.
- In the Windows Agent Monitor Template dialog box, enter the information under each tab with reference to the tables below.
- Configure the Generic settings with reference to the table below:
Generic settings Guidelines Name Enter the name of the Windows Agent Monitor Template. This name is used as a reference in Template associations. Description Enter a description of the Windows Agent Monitor Template. - Configure the Event settings with reference to the table below. Make sure you have completed these steps
from the Windows Agent Installation Guide:
- To enable DNS logging, follow the steps in Configuring Windows DNS.
- To enable DHCP logging, follow the steps in Configuring Windows DHCP.
- To enable IIS logging, follow the steps in Configuring Windows IIS.
- To get sysmon events, follow the steps in Configuring Windows Sysmon.
Event settings Guidelines Event Log To configure Event log settings:
- Select the Type of log from the drop-down:
- Application — Events that are logged by Windows Application. Select All, Exchange Server or SQL Server as Source.
- Security — Log that contains records of login/logout activity or other security-related events specified by the system's audit policy.
- System — Events that are logged by the operating system components.
- DFS — Logs to identify the users who accessed the Distributed File System.
- DNS — DNS Debug logs and Name Resolution Activity logs.
- Hardware Events — Events related to hardware.
- Key Management Service — Events related to creation and control of keys used to encrypt your data.
- Setup — Log files for all actions that occur during installation.
- Windows PowerShell — Logs related to Windows PowerShell.
- Other — Any other log type (specify the name under Event Name setting.)
- Enter the events to be included under Include Event and the ones to exclude under Exclude Event by entering each event ID followed by a semicolon as a separator.
- Select UEBA to turn on UEBA functionality for all hosts running Windows 4.0 that are permitted by the UEBA license. For example, if you have 10 UEBA licenses and you applied the template to 100 hosts, system will apply the UEBA license to 10 random hosts. You can turn on/off UEBA on hosts via CMDB.
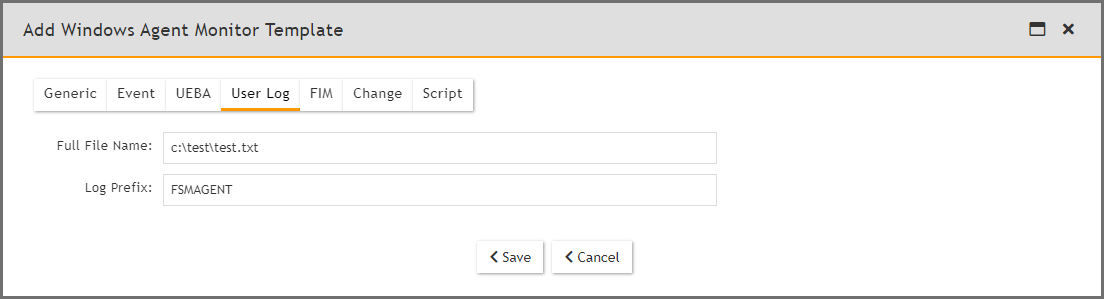
- Configure the User Log settings with reference to the table below:
User Log settings Guidelines User Log Click New to add the custom log files that must be monitored:
- File—(Required) Enter the full file name.
- Log Prefix—(Required) Any prefix to the identify events from this file for better accessibility.
Example:
The contents of the file
C:\test\test.txtneeds to be brought into FortiSIEM for analysis. The log prefix FSMAGENT was chosen. To configure the Windows Agent template in FortiSIEM, from the User Log tab, you would take the following steps.In the Full file Name field, you would enter "C:\test\test.txt".
In the Log Prefix field, you would enter "FSMAGENT".
Suppose the contents of the file C:\test\test.txt looks like this.
User adds a comment
User adds a comment 1
User adds a comment 2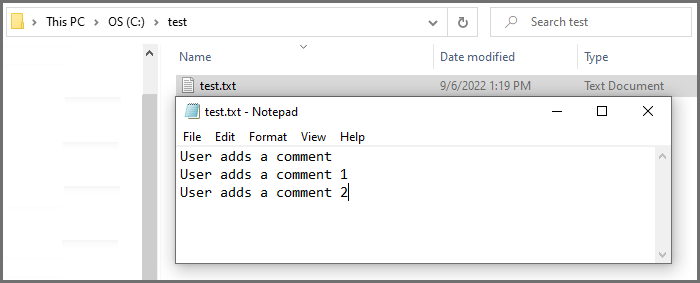
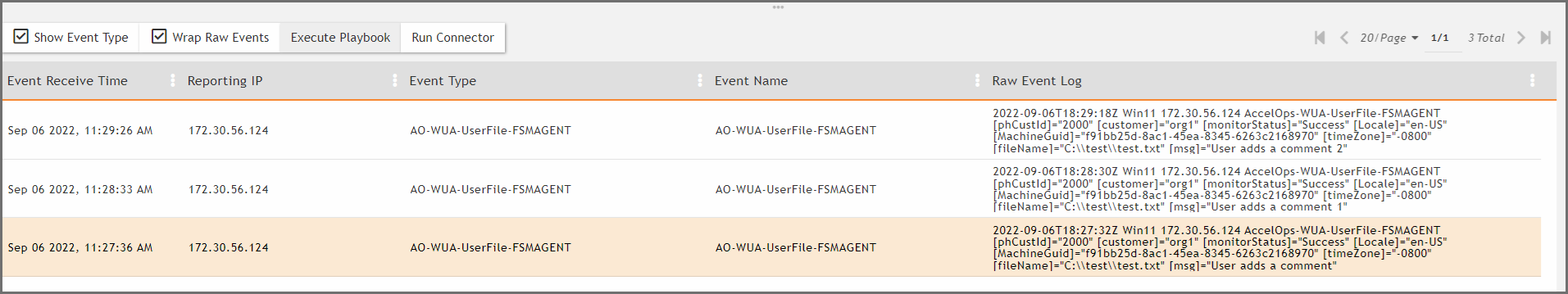
FortiSIEM agent will send each line in a separate event.
2022-09-06T17:16:27Z Win11 172.30.56.124 AccelOps-WUA-UserFile-FSMAGENT [phCustId]="2000" [customer]="org1" [monitorStatus]="Success" [Locale]="en-US" [MachineGuid]="f91bb25d-8ac1-45ea-8345-6263c2168970" [timeZone]="-0800" [fileName]="C:\\test\\test.txt" [msg]="User adds a comment" 2022-09-06T17:18:27Z Win11 172.30.56.124 AccelOps-WUA-UserFile-FSMAGENT [phCustId]="2000" [customer]="org1" [monitorStatus]="Success" [Locale]="en-US" [MachineGuid]="f91bb25d-8ac1-45ea-8345-6263c2168970" [timeZone]="-0800" [fileName]="C:\\test\\test.txt" [msg]="User adds a comment 1" 2022-09-06T17:20:27Z Win11 172.30.56.124 AccelOps-WUA-UserFile-FSMAGENT [phCustId]="2000" [customer]="org1" [monitorStatus]="Success" [Locale]="en-US" [MachineGuid]="f91bb25d-8ac1-45ea-8345-6263c2168970" [timeZone]="-0800" [fileName]="C:\\test\\test.txt" [msg]="User adds a comment 2"
The event type will be AO-WUA-UserFile-FSMAGENT.
-
Configure the FIM settings with reference to the table below. Make sure you have completed these steps
from the Windows Agent Installation Guide:
- To enable logging appropriately, follow the steps in Configure Security Audit Logging Policy.
- To get user meta data in the file auditing logs, follow the steps in Configure File Auditing Policy.
- To enable change events for permission and/or ownership changes to files and/or directories, follow the steps in Configure Audit File System Policy.
FIM settings Guidelines FIM To include the file directory details:
- Click New to add the file directory details:
- File/Directory— Enter the full path of the file directory:
- Include Subfolder(s) — Select if you must include the directory sub-folders.
- Exclude Subfolder(s) — Enter any sub-folders to exclude, if any.
- Include File Type — Enter the file types to include separated by a semi-colon.
- Exclude File Type — Enter the file types to exclude, if any, separated by a semi-colon.
- On Modify:
- Push Files—Select this if you want Windows Agent to push files to FortiSIEM whenever there is a change. File/Directory must specify a specific file and not a directory. Also, the absolute file name, including the path, must be specified. For example
C:\temp\fileToBeMonitored.txt. The files are stored in SVN and are accessible from the Supervisor. These files are displayed in CMDB > Device > File. Send only important files, as this can fill up disk space. - Compare Baseline—Select this if you want to be alerted when the file changes from a baseline. File/Directory must specify a specific file and not a directory. Also, the absolute file name, including the path, must be specified. For example
C:\temp\fileToBeMonitored.txt. This is common for configuration files that rarely change. If you choose this option, you will be asked to provide a copy of the baseline file. Click Choose File and upload the file from your workstation. The Supervisor will compute the MD5 checksum and distribute the checksum to the agents for comparison.
- Push Files—Select this if you want Windows Agent to push files to FortiSIEM whenever there is a change. File/Directory must specify a specific file and not a directory. Also, the absolute file name, including the path, must be specified. For example
- Click Save.
Use the Edit/Delete buttons to modify/remove any file directory information.
- Configure the Change settings with reference to the table below:
Change settings Guidelines Registry Change Select the required key(s) to monitor:
- HKEY_CLASSES_ROOT—key that contains file extension association information, as well as a programmatic identifier, Class ID, and Interface ID data.
- HKEY_CURRENT_USER—key that contains configuration information for Windows and software specific to the currently logged in user.
- HKEY_LOCAL_MACHINE—hive that contains the majority of the configuration information for the software you have installed, as well as for the Windows Operating System.
- HKEY_USERS—key that contains user-specific configuration information of all currently active users on the computer.
- HKEY_CURRENT_CONFIG—key that acts as a shortcut to a registry key which keeps information about the hardware profile currently used.
Check Every Set the time period to check the Registry Change in Minute(s) or Hour(s). Installed Software Change Select to enable monitoring of any installed software change. Removable Drive Select the removable drive to track:
- USB drive(s)
- CD-DVD drive(s)
- Configure the Script settings with reference to the table below:
Script settings Guidelines WMI Classes To include a WMI Class:
- Click New to add a new WMI Class. Select the Name, WMI Class, and Attributes from the drop-down lists (Use ';' as the separator).
- Set the time period to monitor in Minute(s) or Hour(s) under Check Every setting.
Use the Edit/Delete buttons to modify/remove any WMI Classes.
PowerShell Script To include a PowerShell Script:
Click New to add a new PowerShell Script and enter the Name and Script.
Use the Edit/Delete buttons to modify/remove any PowerShell Script.
- Configure the Generic settings with reference to the table below:
- Click Save.
Use the Edit button to modify any template or Delete button to remove any Windows Agent Monitor template.
Associate Windows Agents to Templates
After defining the monitoring templates, you must associate hosts to templates. To scale to a large number of hosts, this is done via Policies. A Policy is a mapping from Organization and Host to Templates and Collectors. Policies are evaluated in order (lower order or rank is higher priority) and the policy that matches first is selected. Therefore, define the exceptions first followed by broad policies. Hosts are defined in terms of CMDB Device Groups or Business Services. Multiple templates can be used in one Policy and the system detects conflicts, if any.
Complete these steps to associate a Host to Template:
- Click New under the section Host To Template Associations.
- In the Host To Template Associations dialog box, enter the information below.
Settings Guidelines Name Name of the Host to Template Association. Organization Select the organization. Host Use the drop-down list to browse the folders and select the Devices or/and Business Services to monitor and click Save. Template Select one or more monitoring templates from the list or select All Templates to include all. You can also use the search bar to find any specific template. Collector Select the Collector from the list or select All Collectors to include all. Agents forward events to Collectors via HTTP(S). A Collector is chosen at random and if that Collector is not available or non-responsive, then another Collector in the list is chosen. - Click Save and Apply.
A Rank is automatically assigned to the association.
You can use the Edit button to modify or Delete button to remove any template association.
Viewing Agent Status
Complete these steps to view the Windows Agent status for any specific device:
- Go to CMDB > Devices and select the device.
The following fields display the information related to the Agent:- Agent Status: status of the Agent on the device
- Agent Policy: agent policy name
- Monitor Status: status of monitoring
The Agent Status indicates the following:
Status Description Registered Agent has completed registration but has not received the monitoring template. Running Active Agent has received a monitoring template and it is performing properly. Running Inactive Agent is running but does not have a monitoring template – the reasons can be (a) no license or (b) incomplete definition - no Collector or Template is defined for that host. Stopped Agent is stopped on the Linux Server. Disconnected Supervisor did not receive any status from the Agent for the last 10 minutes.
Enabling or Disabling an Agent
Complete these steps to enable or disable Agent for a specific device:
- Go to CMDB > Devices and select the required device.
- Select the Actions drop-down menu and click Enable Agent to enable or Disable Agent to disable Agent monitoring for the selected device.
Viewing Files in FortiSIEM
If the FortiSIEM Agent is running on a Server and a FIM policy is enabled with Push Files On Modify, then the FortiSIEM Agent will send the files to FortiSIEM when a change is detected. FortiSIEM stores the files in SVN on the Supervisor.
- Go to the CMDB page. Make sure that AGENT is one of the Methods.
- Search for the device in CMDB by name.
Use the host name that you used in the
InstallSettings.xmlfile to install the Windows Agent. - Click File beneath the device table.
You will see all of the files that were changed since the monitoring template was applied.
- Select a file.
If you need to search for a file, set the From and To dates. The files which changed between those dates will be displayed.
- Click the file name on the left and its contents will be displayed in the right hand window.
Each file has a header containing file meta data followed by the actual file content.
FILEPATH: The full file name, including the path.
ARCHIVE: Set to true if ArchiveBit is set; set to false if it is not.
HASHCODE: The file hash.
HASHALGO: The algorithm used to compute file hash.
OWNER: The file owner.
USER, PERMIT, DENY: Permissions are specified as a (User, Permit, Deny) triple. This describes the actions that the user is allowed to perform.
MODIFIED_TIME: The time when the file was last modified.
- To see the differences between two files, select two files on left and click Diff.
Verifying Events in FortiSIEM
Follow the steps below to verify the events in FortiSIEM:
- Go to ANALYTICS tab.
- Click the Filters field.
- Create the following condition: Attribute= Raw Event Log, Operator = CONTAIN, Value = AccelOps-WUA and click Save & Run.
Note: All event types for all Windows Server generated logs are prefixed by AccelOps-WUA. - Select the following Group By:
- Reporting Device Name
- Reporting IP
- Select the following Display Fields:
- Reporting Device Name
- Reporting IP
- COUNT(Matched Events)
- Run the query for the last 15 minutes.
The query will return all hosts that reported events in the last 15 minutes.
Sample Windows Agent Logs
FortiSIEM Windows Agent Manager generates Windows logs in an easy way to analyze "attribute=value" style without losing any information.
- System Logs
- Application Logs
- Security Logs
- DNS Logs
- DHCP Logs
- IIS Logs
- DFS Logs
- File Content Monitoring Logs
- File Integrity Monitoring Logs
- Installed Software Logs
- Registry change Logs
- WMI Logs
- Agent Troubleshooting Notes
System Logs
#Win-System-Service-Control-Manager-7036 Thu May 07 02:13:42 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-WinLog [monitorStatus]="Success" [eventName]="System" [eventSource]="Service Control Manager" [eventId]="7036" [eventType]="Information" [domain]="" [computer]="WIN-2008-LAW-agent" [user]="" [userSID]="" [userSIDAcctType]="" [eventTime]="May 07 2015 10:13:41" [deviceTime]="May 07 2015 10:13:41" [msg]="The Skype Updater service entered the running state."
Thu May 07 02:13:48 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-WinLog [monitorStatus]="Success" [eventName]="System" [eventSource]="Service Control Manager" [eventId]="7036" [eventType]="Information" [domain]="" [computer]="WIN-2008-LAW-agent" [user]="" [userSID]="" [userSIDAcctType]="" [eventTime]="May 07 2015 10:13:47" [deviceTime]="May 07 2015 10:13:47" [msg]="The Skype Updater service entered the stopped state."
Application Logs
#Win-App-MSExchangeServiceHost-2001 Thu May 07 03:05:42 2015 WIN-2008-249.ersijiu.com 10.1.2.249 AccelOps-WUA-WinLog [monitorStatus]="Success" [eventName]="Application" [eventSource]="MSExchangeServiceHost" [eventId]="2001" [eventType]="Information" [domain]="" [computer]="WIN-2008-249.ersijiu.com" [user]="" [userSID]="" [userSIDAcctType]="" [eventTime]="May 07 2015 11:05:42" [deviceTime]="May 07 2015 11:05:42" [msg]="Loading servicelet module Microsoft.Exchange.OABMaintenanceServicelet.dll"
#MSSQL #Win-App-MSSQLSERVER-17137 Thu May 07 03:10:16 2015 WIN-2008-249.ersijiu.com 10.1.2.249 AccelOps-WUA-WinLog [monitorStatus]="Success" [eventName]="Application" [eventSource]="MSSQLSERVER" [eventId]="17137" [eventType]="Information" [domain]="" [computer]="WIN-2008-249.ersijiu.com" [user]="" [userSID]="" [userSIDAcctType]="" [eventTime]="May 07 2015 11:10:16" [deviceTime]="May 07 2015 11:10:16" [msg]="Starting up database 'model'."
Security Logs
#Win-Security-4624(Windows logon success)
Thu May 07 02:23:58 2015 WIN-2008-249.ersijiu.com 10.1.2.249 AccelOps-WUA-WinLog [monitorStatus]="Success" [eventName]="Security"
[eventSource]="Microsoft-Windows-Security-Auditing" [eventId]="4624" [eventType]="Audit Success" [domain]=""
[computer]="WIN-2008-249.ersijiu.com" [user]="" [userSID]="" [userSIDAcctType]="" [eventTime]="May 07 2015 10:23:56"
[deviceTime]="May 07 2015 10:23:56" [msg]="An account was successfully logged on." [[Subject]][Security ID]="S-1-0-0" [Account Name]=""
[Account Domain]="" [Logon ID]="0x0" [Logon Type]="3" [[New Logon]][Security ID]="S-1-5-21-3459063063-1203930890-2363081030-500"
[Account Name]="Administrator" [Account Domain]="ERSIJIU" [Logon ID]="0xb9bd3" [Logon GUID]="{00000000-0000-0000-0000-000000000000}"
[[Process Information]][Process ID]="0x0" [Process Name]="" [[Network Information]][Workstation Name]="SP171" [Source Network Address]="10.1.2.171"
[Source Port]="52409" [[Detailed Authentication Information]][Logon Process]="NtLmSsp" [Authentication Package]="NTLM" [Transited Services]=""
[Package Name (NTLM only)]="NTLM V2" [Key Length]="128" [details]=""
DNS Logs
#DNS Debug Logs #AccelOps-WUA-DNS-Started Thu May 07 02:35:43 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-DNS [monitorStatus]="Success" [msg]="5/7/2015 10:34:05 AM 20BC EVENT The DNS server has started."
#AccelOps-WUA-DNS-ZoneDownloadComplete Thu May 07 02:35:43 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-DNS [monitorStatus]="Success" [msg]="5/7/2015 10:34:05 AM 20BC EVENT The DNS server has finished the background loading of zones. All zones are now available for DNS updates and zone transfers, as allowed by their individual zone configuration."
#AccelOps-WUA-DNS-A-Query-Success Thu May 07 02:48:25 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-DNS [monitorStatus]="Success" [msg]="5/7/2015 10:47:13 AM 5D58 PACKET 0000000002B74600 UDP Rcv 10.1.20.232 0002 Q [0001 D NOERROR] A (8)testyjyj(4)yjyj(3)com(0)"Thu May 07 02:48:25 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-DNS [monitorStatus]="Success" [msg]="5/7/2015 10:47:13 AM 5D58 PACKET 0000000002B74600 UDP Snd 10.1.20.232 0002 R Q [8085 A DR NOERROR] A (8)testyjyj(4)yjyj(3)com(0)"
#AccelOps-WUA-DNS-PTR-Query-Success Thu May 07 02:48:25 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-DNS [monitorStatus]="Success" [msg]="5/7/2015 10:47:22 AM 5D58 PACKET 00000000028AB4B0 UDP Rcv 10.1.20.232 0002 Q [0001 D NOERROR] PTR (3)223(3)102(3)102(3)102(7)in-addr(4)arpa(0)"
Thu May 07 02:48:25 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-DNS [monitorStatus]="Success" [msg]="5/7/2015 10:47:22 AM 5D58 PACKET 00000000028AB4B0 UDP Snd 10.1.20.232 0002 R Q [8085 A DR NOERROR] PTR (3)223(3)102(3)102(3)102(7)in-addr(4)arpa(0)"
#DNS System Logs #Win-App-DNS-2(DNS Server started) Thu May 07 02:39:17 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-WinLog [monitorStatus]="Success" [eventName]="DNS Server" [eventSource]="DNS" [eventId]="2" [eventType]="Information" [domain]="" [computer]="WIN-2008-LAW-agent" [user]="" [userSID]="" [userSIDAcctType]="" [eventTime]="May 07 2015 10:39:17" [deviceTime]="May 07 2015 10:39:17" [msg]="The DNS server has started."
#Win-App-DNS-3(DNS Server shutdown) Thu May 07 02:39:16 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-WinLog [monitorStatus]="Success" [eventName]="DNS Server" [eventSource]="DNS" [eventId]="3" [eventType]="Information" [domain]="" [computer]="WIN-2008-LAW-agent" [user]="" [userSID]="" [userSIDAcctType]="" [eventTime]="May 07 2015 10:39:16" [deviceTime]="May 07 2015 10:39:16" [msg]="The DNS server has shut down.
DHCP Logs
AccelOps-WUA-DHCP-Generic Thu May 07 05:44:44 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-DHCP [monitorStatus]="Success" [ID]="00" [Date]="05/07/15" [Time]="13:44:08" [Description]="Started" [IP Address]="" [Host Name]="" [MAC Address]="" [User Name]="" [ TransactionID]="0" [ QResult]="6" [Probationtime]="" [ CorrelationID]="" [Dhcid.]=""
#AccelOps-WUA-DHCP-IP-ASSIGN Thu May 07 05:56:41 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-DHCP [monitorStatus]="Success" [ID]="10" [Date]="05/07/15" [Time]="13:56:37" [Description]="Assign" [IP Address]="10.1.2.124" [Host Name]="Agent-247.yj" [MAC Address]="000C2922118E" [User Name]="" [ TransactionID]="2987030242" [ QResult]="0" [Probationtime]="" [ CorrelationID]="" [Dhcid.]=""
#AccelOps-WUA-DHCP-Generic(Release) Thu May 07 05:56:41 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-DHCP [monitorStatus]="Success" [ID]="12" [Date]="05/07/15" [Time]="13:56:33" [Description]="Release" [IP Address]="10.1.2.124" [Host Name]="Agent-247.yj" [MAC Address]="000C2922118E" [User Name]="" [ TransactionID]="2179405838" [ QResult]="0" [Probationtime]="" [ CorrelationID]="" [Dhcid.]=""
#AccelOps-WUA-DHCP-IP-LEASE-RENEW Wed Feb 25 02:53:28 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-DHCP [monitorStatus]="Success" [ID]="11" [Date]="02/25/15" [Time]="10:53:19" [Description]="Renew" [IP Address]="10.1.2.123" [Host Name]="WIN-2008-249.yj" [MAC Address]="0050568F1B5D" [User Name]="" [ TransactionID]="1136957584" [ QResult]="0" [Probationtime]="" [ CorrelationID]="" [Dhcid.]=""
IIS Logs
#AccelOps-WUA-IIS-Web-Request-Success Thu May 07 03:49:23 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-IIS [monitorStatus]="Success" [date]="2015-05-07" [time]="03:44:28" [s-sitename]="W3SVC1" [s-computername]="WIN-2008-LAW-AG" [s-ip]="10.1.2.242" [cs-method]="GET" [cs-uri-stem]="/welcome.png" [cs-uri-query]="-" [s-port]="80" [cs-username]="-" [c-ip]="10.1.20.232" [cs-version]="HTTP/1.1" [cs(User-Agent)]="Mozilla/5.0+(Windows+NT+6.1;+WOW64)+AppleWebKit/537.36+(KHTML,+like+Gecko)+Chrome/42.0.2311.135+Safari/537.36" [cs(Cookie)]="-" [cs(Referer)]="http://10.1.2.242/" [cs-host]="10.1.2.242" [sc-status]="200" [sc-substatus]="0" [sc-win32-status]="0" [sc-bytes]="185173" [cs-bytes]="324" [time-taken]="78" [site]="Default Web Site" [format]="W3C"
#AccelOps-WUA-IIS-Web-Client-Error Thu May 07 03:49:23 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-IIS [monitorStatus]="Success" [date]="2015-05-07" [time]="03:44:37" [s-sitename]="W3SVC1" [s-computername]="WIN-2008-LAW-AG" [s-ip]="10.1.2.242" [cs-method]="GET" [cs-uri-stem]="/wrongpage" [cs-uri-query]="-" [s-port]="80" [cs-username]="-" [c-ip]="10.1.20.232" [cs-version]="HTTP/1.1" [cs(User-Agent)]="Mozilla/5.0+(Windows+NT+6.1;+WOW64)+AppleWebKit/537.36+(KHTML,+like+Gecko)+Chrome/42.0.2311.135+Safari/537.36" [cs(Cookie)]="-" [cs(Referer)]="-" [cs-host]="10.1.2.242" [sc-status]="404" [sc-substatus]="0" [sc-win32-status]="2" [sc-bytes]="1382" [cs-bytes]="347" [time-taken]="0" [site]="Default Web Site" [format]="W3C"
#AccelOps-WUA-IIS-Web-Forbidden-Access-Denied Thu May 07 03:30:39 2015 WIN-2008-249.ersijiu.com 10.1.2.249 AccelOps-WUA-IIS [monitorStatus]="Success" [date]="2015-05-07" [time]="03:30:15" [s-ip]="10.1.2.249" [cs-method]="POST" [cs-uri-stem]="/AOCACWS/AOCACWS.svc" [cs-uri-query]="-" [s-port]="80" [cs-username]="-" [c-ip]="10.1.2.42" [cs(User-Agent)]="-" [sc-status]="403" [sc-substatus]="4" [sc-win32-status]="5" [time-taken]="1" [site]="Default Web Site" [format]="W3C"
DFS Logs
#Win-App-DFSR-1002 Thu May 07 03:01:12 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-WinLog [monitorStatus]="Success" [eventName]="DFS Replication" [eventSource]="DFSR" [eventId]="1002" [eventType]="Information" [domain]="" [computer]="WIN-2008-LAW-agent" [user]="" [userSID]="" [userSIDAcctType]="" [eventTime]="May 07 2015 11:01:12" [deviceTime]="May 07 2015 11:01:12" [msg]="The DFS Replication service is starting."
#Win-App-DFSR-1004 Thu May 07 03:01:12 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-WinLog [monitorStatus]="Success" [eventName]="DFS Replication" [eventSource]="DFSR" [eventId]="1004" [eventType]="Information" [domain]="" [computer]="WIN-2008-LAW-agent" [user]="" [userSID]="" [userSIDAcctType]="" [eventTime]="May 07 2015 11:01:12" [deviceTime]="May 07 2015 11:01:12" [msg]="The DFS Replication service has started."
#Win-App-DFSR-1006 Thu May 07 03:01:10 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-WinLog [monitorStatus]="Success" [eventName]="DFS Replication" [eventSource]="DFSR" [eventId]="1006" [eventType]="Information" [domain]="" [computer]="WIN-2008-LAW-agent" [user]="" [userSID]="" [userSIDAcctType]="" [eventTime]="May 07 2015 11:01:10" [deviceTime]="May 07 2015 11:01:10" [msg]="The DFS Replication service is stopping."
#Win-App-DFSR-1008 Thu May 07 03:01:11 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-WinLog [monitorStatus]="Success" [eventName]="DFS Replication" [eventSource]="DFSR" [eventId]="1008" [eventType]="Information" [domain]="" [computer]="WIN-2008-LAW-agent" [user]="" [userSID]="" [userSIDAcctType]="" [eventTime]="May 07 2015 11:01:11" [deviceTime]="May 07 2015 11:01:11" [msg]="The DFS Replication service has stopped."
File Content Monitoring Logs
#AccelOps-WUA-UserFile Thu May 07 05:40:08 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-UserFile [monitorStatus]="Success" [fileName]="C:\test\i.txt" [msg]="another newline adddedddddd"
File Integrity Monitoring Logs
The following sections describe various use cases that can be detected by File Integrity Monitoring Logs.
- Use Case 1: File or Directory Created
- Use Case 2: File or Directory Deleted
- Use Case 3: File Content Modified
- Use Case 4: File Content Modified and Upload is Selected
- Use Case 5: File Renamed
- Use Case 6: File Permission Changed
- Use Case 7: File Ownership Changed
- Use Case 8: File Archive Bit Changed
- Use Case 9: File Baseline Changed
Use Case 1: File or Directory Created
Event Type
AO-WUA-FileMon-Added
Important Event Attributes
userId: The ID of the user who added the file.domain: The user’s domain for a Domain computer.osObjType- Can be either File or Directory.fileName: The name of the file or directory that was added.hashCode, hashAlgo: The file hash obtained by using the specified algorithm.procName: The name of the Windows process that was used to create the file.fileOwner: The owner of the file.targetUserType, targetUser: The user or group to whom the permission applies.targetFilePermit: The permitted file operations.targetFileDeny: The denied file operations.archiveSet: Istrueif the Archive bit is set for this file;falseotherwise.
Reports
Agent FIM: Windows File/Directory Created/Deleted/Renamed
Rules
Agent FIM - Windows File or Directory Created
Sample Log
2020-03-25T07:30:50Z Win-167 10.30.2.167 AccelOps-WUA-FileMon [phCustId]="2000" [customer]="org1" [monitorStatus]="Success" [Locale]="en-US" [MachineGuid]="e892a6e4-bbfa-4ba6-bc8c-00d2c31812b4" [timeZone]="+0800" [userId]="jdoe" [domain]="ACME" [eventTime]="Mar 25 2020 07:30:48" [fileName]="C:\\test\\New Text Document.txt" [osObjAction]="Added" [objectType]="File" [hashCode]="e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855" [hashAlgo]="SHA256" [procName]="C:\\Windows\\explorer.exe" [msg]="" [archiveSet]="true" [fileOwner]=""
Use Case 2: File or Directory Deleted
Event Type
AO-WUA-FileMon-Removed
Important Event Attributes
userId: The ID of the user who removed the file.domain: The user’s domain for a Domain computer.fileName: The name of the file that was removed.procName: The Windows process that was used to remove the file.
Report
Agent FIM: Windows File/Directory Creation/Deletion/Rename
Rule
Agent FIM - Windows File or Directory Deleted
Sample Log
2020-03-25T07:43:24Z Win-167 10.30.2.167 AccelOps-WUA-FileMon [phCustId]="2000" [customer]="org1" [monitorStatus]="Success" [Locale]="en-US" [MachineGuid]="e892a6e4-bbfa-4ba6-bc8c-00d2c31812b4" [timeZone]="+0800" [userId]="jdoe" [domain]="ACME" [eventTime]="Mar 25 2020 07:43:21" [fileName]="C:\\test\\test1.txt" [osObjAction]="Removed" [objectType]="Unknown" [hashCode]="" [hashAlgo]="SHA256" [procName]="C:\\Windows\\explorer.exe" [msg]="" [archiveSet]="false" [fileOwner]=""
Use Case 3: File Content Modified
Event Type
AO-WUA-FileMon-Modified
Important Event Attributes
userId: The user who modified the file.domain: The user’s domain for a Domain computer.fileName: The name of the file that was modified.procName: The Windows process that was used to modify the file.hashCode, hashAlgo: The file hash after modification and the algorithm used to calculate the hash.
Report
Agent FIM: Windows File Content Modified
Rule
Agent FIM - Windows File Content Modified
Sample Log
2020-03-25T10:50:40Z WIN-167.fortinet.wulei.com 10.30.2.167 AccelOps-WUA-FileMon [phCustId]="2000" [customer]="org1" [monitorStatus]="Success" [Locale]="en-US" [MachineGuid]="e892a6e4-bbfa-4ba6-bc8c-00d2c31812b4" [timeZone]="+0800" [userId]="jdoe" [domain]="ACME" [eventTime]="Mar 25 2020 10:50:37" [fileName]="C:\\test\\test.txt" [osObjAction]="Modified" [objectType]="File" [hashCode]="6396e3c19b155770f3ae25afa5f29832d6f35b315407ed88820339b705fd2bcc" [hashAlgo]="SHA256" [procName]="C:\\Windows\\System32\<br/>otepad.exe" [msg]="" [archiveSet]="true" [fileOwner]=""
Use Case 4: File Content Modified and Upload is Selected
Event Type
PH_DEV_MON_FILE_CONTENT_CHANGE
Important Event Attributes
userId: The ID of the user who modified the file.domain: The user’s domain for a Domain computer.fileName: The name of the file that was modified.procName: The Windows process that was used to modify the file.hashCode, hashAlgo: The file hash after modification and the algorithm used to calculate the hash.oldSVNVersion: The SVN revision number of file before the change.newSVNVersion: The SVN revision number of file after the change.addedItem: The lines that were added to the file.deletedItem: The lines that were removed from the file.
Report
Agent FIM: Windows File Content Modified in SVN
Rule
Audited file or directory content modified in SVN
Sample Log
<14>Mar 25 20:30:44 sp3 phPerfMonitor[17521]: [PH_DEV_MON_FILE_CONTENT_CHANGE]:[eventSeverity]=PHL_INFO,[procName]=phPerfMonitor,[fileName]=phSvnUpdate.cpp,[lineNumber]=306,[phCustId]=2000,[hostName]=Win-169,[hostIpAddr]=10.30.3.169,[fileName]=/C:/test/test.txt,[hashCode]=08998b2cce90ee6695bd8dae82d43137,[oldSVNVersion]=50,[newSVNVersion]=51,[deletedItem]=(none),[addedItem]=333;,[user]=Administrator,[hashAlgo]=SHA256,[phLogDetail]=
Use Case 5: File Renamed
Event Type
AO-WUA-FileMon-Renamed-New-Name
Important Event Attributes
userId: The ID of the user who renamed the file.domain: The user’s domain for a Domain computer.fileName: The new name of the file.procName: The Windows process that was used to rename the file.hashCode, hashAlgo: The new file hash using the specified algorithm.
Report
Agent FIM: Windows File/Directory Creation/Deletion/Rename
Rule
None
Sample Log
2020-03-25T09:59:34Z WIN-167.fortinet.wulei.com 10.30.2.167 AccelOps-WUA-FileMon [phCustId]="2000" [customer]="org1" [monitorStatus]="Success" [Locale]="en-US" [MachineGuid]="e892a6e4-bbfa-4ba6-bc8c-00d2c31812b4" [timeZone]="+0800" [userId]="jdoe" [domain]="ACME" [eventTime]="Mar 25 2020 09:59:32" [fileName]="C:\\test\\test5.txt" [osObjAction]="Renamed [New Name]" [objectType]="File" [hashCode]="2b64c6d9afd8a34ed0dbf35f7de171a8825a50d9f42f05e98fe2b1addf00ab44" [hashAlgo]="SHA256" [procName]="C:\\Windows\\explorer.exe" [msg]="" [archiveSet]="true" [fileOwner]=""
Event Type
AO-WUA-FileMon-Renamed-Old-Name
Important Event Attributes
userId: The ID of the user who modified the file.
domain: The user’s domain for a Domain computer.
fileName: The old name of the file before renaming.
procName: The Windows process that was used to remove the file.
Report
Agent FIM: Windows File/Directory Creation/Deletion/Rename
Rule
None
Sample Log
None
Use Case 6: File Permission Changed
Event Type
AO-WUA-FileMon-PermissionChange
Important Event Attributes
userId: The ID of the user who modified the file permission.domain: The user’s domain for a Domain computer.objectType: The type of object. Can beFileorDirectory.fileName: The name of the file or directory whose permission was changed.procName: The Windows process that was used to change the permission.hashCode, hashAlgo: The file hash using the specified algorithm.fileOwner: The name of the owner of the file.targetUserType, targetUser: The name of the user or group to whom the permission below applies.targetFilePermit: The permitted file operations after change.targetFileDeny: The denied file operations after change.archiveSet: Istrueif theArchivebit is set for this file;falseotherwise.
Report
Agent FIM: Windows File/Directory Permission Changes
Rule
Agent FIM - Windows File Permission Changed
Sample Log
2020-03-25T10:21:00Z WIN-167.fortinet.wulei.com 10.30.2.167 AccelOps-WUA-FileMon [phCustId]="2000" [customer]="org1" [monitorStatus]="Success" [Locale]="en-US" [MachineGuid]="e892a6e4-bbfa-4ba6-bc8c-00d2c31812b4" [timeZone]="+0800" [userId]="jdoe" [domain]="ACME" [eventTime]="Mar 25 2020 10:20:58" [fileName]="C:\\test\\test.txt" [osObjAction]="PermissionChange" [objectType]="File" [hashCode]="7936d255ef43706a93fdd15f4bbfde45e3b2d2b9a0d4cc7c39184cf745ab78c5" [hashAlgo]="SHA256" [procName]="C:\\Windows\\System32\\dllhost.exe" [msg]="" [archiveSet]="true" [fileOwner]=“Joe” [targetUserType]="USER" [targetUser]="BUILTIN\Administrators" [targetFilePermit]="ALL" [targetFileDeny]="WRITE"
Use Case 7: File Ownership Changed
Event Type
AO-WUA-FileMon-OwnershipChange
Important Event Attributes
userId: The ID of the user who modified the file ownership.domain: The user’s domain for a Domain computer.objectType: The type of object whose ownership was changed:FileorDirectory.fileName: The name of the file or directory whose ownership was changed.procName: The Windows process that was used to change ownership.hashCode, hashAlgo: The file hash using the specified algorithm.fileOwner: The name of the new file owner.archiveSet: Istrueif theArchivebit is set for this file;falseotherwise.
Report
Agent FIM: Windows File/Directory Ownership Changes
Rule
Agent FIM - Windows File Ownership Changed
Sample Log
2020-03-06T07:08:56Z Win-167 10.30.2.167 AccelOps-WUA-FileMon [phCustId]="1" [customer]="super" [monitorStatus]="Success" [Locale]="en-US" [MachineGuid]="e892a6e4-bbfa-4ba6-bc8c-00d2c31812b4" [timeZone]="+0800" [userId]="Administrator" [domain]="WIN-167" [eventTime]="Mar 06 2020 07:08:53" [fileName]="C:\\test\\test1.txt" [osObjAction]="OwnershipChange" [objectType]="File" [hashCode]="d17f25ecfbcc7857f7bebea469308be0b2580943e96d13a3ad98a13675c4bfc2" [hashAlgo]="SHA256" [procName]="C:\\Windows\\System32\\dllhost.exe" [msg]="" [archiveSet]="true" [fileOwner]=“Joe”
Use Case 8: File Archive Bit Changed
Event Type
AO-WUA-FileMon-ArchivedBitChange
Important Event Attributes
userId: The ID of the user who modified the file.domain: The user’s domain for a Domain computer.objectType: The type of object whoseArchivebit was changed:FileorDirectory.fileName: The name of the file whose archive bit was changed.procName: The Windows process that was used to change archive bit.hashCode, hashAlgo: The file hash using the specified algorithm.archiveSet: Istrueif theArchivebit is set for this file;falseotherwise.
Report
Agent FIM: Windows File/Directory Archive Bit Changes
Rule
Agent FIM - Windows File/Directory Archive Bit Changed
Sample Log
2020-03-25T10:02:38Z WIN-167.fortinet.wulei.com 10.30.2.167 AccelOps-WUA-FileMon [phCustId]="2000" [customer]="org1" [monitorStatus]="Success" [Locale]="en-US" [MachineGuid]="e892a6e4-bbfa-4ba6-bc8c-00d2c31812b4" [timeZone]="+0800" [userId]="jdoe" [domain]="ACME" [eventTime]="Mar 25 2020 10:02:35" [fileName]="C:\\test\\test.txt" [osObjAction]="ArchivedBitChange" [objectType]="File" [hashCode]="7936d255ef43706a93fdd15f4bbfde45e3b2d2b9a0d4cc7c39184cf745ab78c5" [hashAlgo]="SHA256" [procName]="C:\\Windows\\System32\\attrib.exe" [msg]="" [archiveSet]="false" [fileOwner]=""
Use Case 9: File Baseline Changed
Event Type
AO-WUA-FileMon-BaselineChange
Important Event Attributes
userId: The ID of the user who modified the file.domain: The user’s domain for a Domain computer.fileName: The name of the file that was changed.procName: The Windows process that was used to remove the file.hashCode, hashAlgo: The file hash using the specified algorithm.targetHashCode: The hash of the target file (defined in the GUI).
Report
Agent FIM: Windows File Change from Baseline
Rule
Agent FIM - Windows File Changed From Baseline
Sample Log
2020-03-25T12:52:42Z Win-169 10.30.3.169 AccelOps-WUA-FileMon [phCustId]="2000" [customer]="org1" [monitorStatus]="Success" [Locale]="en-US" [MachineGuid]="5c83ec12-73fd-4e06-a396-1f128564f09e" [timeZone]="+0800" [userId]="Administrator" [domain]="WINSRV2012-169" [fileName]="C:\\test\\test.txt" [osObjAction]="BaselineChange" [hashCode]="c1f79ea2bbfb77bf30446a4c9be762eb" [hashAlgo]="MD5" [targetHashCode]="74DE7651DFC55294CC59240AE514A676" [msg]="
Installed Software Logs
#AccelOps-WUA-InstSw-Added Thu May 07 05:28:17 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-InstSw [monitorStatus]="Success" [osObjAction]="Added" [appName]="7-Zip 9.20 (x64 edition)" [vendor]="Igor Pavlov" [appVersion]="9.20.00.0"
#AccelOps-WUA-InstSw-Removed Thu May 07 05:28:30 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-InstSw [monitorStatus]="Success" [osObjAction]="Removed" [appName]="7-Zip 9.20 (x64 edition)" [vendor]="Igor Pavlov" [appVersion]="9.20.00.0"
Registry Change Logs
#AccelOps-WUA-Registry-Modified
Thu May 07 04:01:58 2015 WIN-2008-249.ersijiu.com 10.1.2.249 AccelOps-WUA-Registry [monitorStatus]="Success" [regKeyPath]="HKLM\\SOFTWARE\\Microsoft\\ExchangeServer\\v14\\ContentIndex\\CatalogHealth\\{0d2a342a-0b15-4995-93db-d18c3df5860d}" [regValueName]="TimeStamp" [regValueType]="1" [osObjAction]="Modified" [oldRegValue]="MgAwADEANQAtADAANQAtADAANwAgADAAMwA6ADQAOQA6ADQANwBaAAAA"
[newRegValue]="MgAwADEANQAtADAANQAtADAANwAgADAANAA6ADAAMQA6ADQAOABaAAAA" #AccelOps-WUA-Registry-Removed Thu May 07 05:25:09 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-Registry [monitorStatus]="Success" [regKeyPath]="HKLM\\SOFTWARE\\RegisteredApplications" [regValueName]="Skype" [regValueType]="1" [osObjAction]="Removed" [oldRegValue]="UwBPAEYAVABXAEEAUgBFAFwAQwBsAGkAZQBuAHQAcwBcAEkAbgB0AGUAcgBuAGUAdAAgAEMAYQBsAGwAXABTAGsAeQBwAGUAXABDAGEAcABhAGIAaQBsAGkAdABpAGUAcwBkAGgAZABoAGQAaABkAGgAZABoAGQAAAA=" [newRegValue]=""
WMI logs
#AccelOps-WUA-WMI-Win32_Processor Thu May 07 03:53:33 2015 WIN-2008-LAW-agent 10.1.2.242 AccelOps-WUA-WMI [monitorStatus]="Success" [__CLASS]="Win32_Processor" [AddressWidth]="64" [Architecture]="9" [Availability]="3" [Caption]="Intel64 Family 6 Model 26 Stepping 5" [ConfigManagerErrorCode]="" [ConfigManagerUserConfig]="" [CpuStatus]="1" [CreationClassName]="Win32_Processor" [CurrentClockSpeed]="2266" [CurrentVoltage]="33" [DataWidth]="64" [Description]="Intel64 Family 6 Model 26 Stepping 5" [DeviceID]="CPU0" [ErrorCleared]="" [ErrorDescription]="" [ExtClock]="" [Family]="12" [InstallDate]="" [L2CacheSize]="0" [L2CacheSpeed]="" [L3CacheSize]="0" [L3CacheSpeed]="0" [LastErrorCode]="" [Level]="6" [LoadPercentage]="8" [Manufacturer]="GenuineIntel" [MaxClockSpeed]="2266" [Name]="Intel(R) Xeon(R) CPU E5520 @ 2.27GHz" [NumberOfCores]="1" [NumberOfLogicalProcessors]="1" [OtherFamilyDescription]="" [PNPDeviceID]="" [PowerManagementCapabilities]="" [PowerManagementSupported]="0" [ProcessorId]="0FEBFBFF000106A5" [ProcessorType]="3" [Revision]="6661" [Role]="CPU" [SocketDesignation]="CPU socket #0" [Status]="OK" [StatusInfo]="3" [Stepping]="" [SystemCreationClassName]="Win32_ComputerSystem" [SystemName]="WIN-2008-LAW-AG" UniqueId]="" [UpgradeMethod]="4" [Version]="" [VoltageCaps]="2"
Agent Troubleshooting Notes
A Windows Agent can be in following states (shown in CMDB):
- Registered
- Running Inactive
- Running Active
- Disabled
- Disconnected
When an Agent is installed and registered, then it is in Registered state. The following audit event is generated: PH_AUDIT_AGENT_INSTALLED.
When a monitoring template is assigned to the device, then the state moves to Running Inactive. When the agent receives the template and starts monitoring, then the state moves to Running Active. In both cases, the following audit event is generated: PH_AUDIT_AGENT_RUNNING.
Agent periodically sends heartbeat messages. When a heartbeat not received for 10 minutes, the state moves to Disconnected and the audit event PH_AUDIT_AGENT_NOTRESPONDING is generated. Status is checked every 1 hour. At that time, if we heard from the Agent in the last 15 minutes, the state moves back to Running Inactive and a PH_AUDIT_AGENT_RUNNING audit event is generated.
If the Agent is disabled from the GUI, the state moves to Disabled and PH_AUDIT_AGENT_DISABLED audit event is generated.
If the Agent is uninstalled or the service is stopped, then the state moves to Disconnected and the audit event PH_AUDIT_AGENT_NOTRESPONDING is generated.
Audit events are generated at state transitions, however, the event PH_AUDIT_AGENT_NOTRESPONDING is generated every hour to identify all agents that are currently disconnected. A nested query can be run to detect Agents that did not report in the last N hours. Note that PH_AUDIT events must be queried with System Event Category = 2. Rules do not need this condition.
