Fortinet Security Fabric overview
The Fortinet Security Fabric provides a visionary approach to security that allows your organization to deliver intelligent, powerful, and seamless security. Fortinet offers security solutions for endpoints, access points, network elements, the data center, applications, cloud, and data, designed to work together as an integrated Security Fabric that can be integrated, analyzed, and managed to provide end-to-end protection for your network. Your organization can also add third-party products that are members of the Fabric-Ready Partner Program to the Security Fabric.
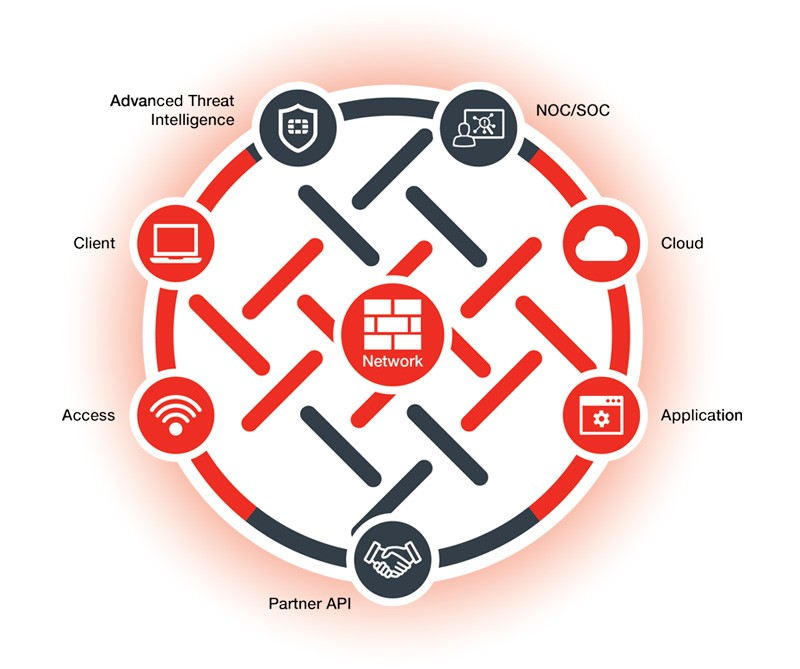
All elements in the Security Fabric work together as a team to share policy, threat intelligence, and application flow information. This collaborative approach expands network visibility and provides fast threat detection in real time and the ability to initiate and synchronize a coordinated response, no matter which part of the network is being compromised. The Security Fabric allows your network to automatically see and dynamically isolate affected devices, partition network segments, update rules, push out new policies, and remove malware.
The Security Fabric is designed to cover the entire attack surface and provide you with complete visibility into your network. It allows you to collect, share, and correlate threat intelligence between security and network devices, centrally manage and orchestrate policies, automatically synchronize resources to enforce policies, and coordinate a response to threats detected anywhere across the extended network. The unified management interface provides you with cooperative security alerts, recommendations, audit reports, and full policy control across the Security Fabric that will give you confidence that your network is secure.
Access security
The Security Fabric secures the access layer of your organization’s network. It integrates various access points in a network, such as endpoints, applications, the cloud, and IoT devices, regardless of their distribution, into an end-to-end solution that covers all attack surfaces.
Secure access architecture extends coordinated security policies to the edge of the wired and wireless network, where most vulnerabilities are targeted. It protects the access layer, guarding against data breaches and security threats from both internal user devices and IoT products.
Client security
Client security, through FortiClient, provides easy-to-manage, automated, fully customizable endpoint security for various devices. FortiClient provides end-to-end threat visibility and control by natively integrating endpoints into the security architecture and offers unified endpoint features, including compliance, protection, and secure access. It also offers integrated patch management and vulnerability shielding to harden all endpoints.
FortiClient integrates with the Security Fabric to provide real-time actionable visibility to stop threats to your organization’s network at the endpoints.
For more information about FortiClient, see http://www.forticlient.com/.
Application security
The Security Fabric protects your organization’s sensitive and proprietary data that is managed by applications, and ensures the security and availability of your organization’s applications. It allows Fortinet application security products, and those of third-party vendors, to work together to boost security across core networks, remote devices, and the cloud. This provides your organization with a network architecture that is secure, aware, actionable, scalable, and open.
Fortinet‘s robust and integrated application security solution provides a complete end-to-end high-performance solution that protects your organization’s valuable information by using a combination of Fortinet products which are deeply integrated into the Security Fabric for direct communications. These products include web application firewalls for application security, DDoS attack mitigation appliances for DDoS protection, advanced application delivery controllers (ADCs) to meet the demands of secure application traffic, sandboxing to isolate malicious code for inspection, and email security gateways that can detect and prevent email-borne threats from getting to your users.
Cloud security
The Security Fabric is designed to extend deep into different cloud environments to ensure that policies are consistent and enforced across all distributed resources. Within the unified security architecture, virtual firewalls can be deployed across private, public, and hybrid clouds to establish north-south and east-west microsegmentation. The Security Fabric weaves cloud applications into the broader environment, governed by seamless, universal security and compliance policies and managed using transparent visibility across the entire attack surface. Combining Fortinet Cloud Security with an existing enterprise firewall deployment extends the same powerful security, as well as the same intelligence and dynamic risk mitigation to applications located either in the cloud or on-premise.
NOC and SOC security
Fortinet’s security operations center solution covers both IT and security risk management across your entire organization. The solution is a comprehensive approach to managing risk that includes adaptive awareness of the threat landscape, rapid local and global threat detection, reduced complexity in managing alerts and alarms, and reporting and analytics so you can better understand how your organization’s risk profiles are being managed.
When Fortinet devices are unified into a Security Fabric, with compatible operating systems and shared intelligence, the security operations solution also includes information from network elements beyond Fortinet devices. The solution allows your network operations center (NOC) and security operations center (SOC) to share information, integrating and cross-correlating the data from each operations center. This additional context, visibility, and focus breaks down the barrier between your NOC and SOC, and gives you a comprehensive view across your entire Security Fabric so you can quickly find and respond to threats.
Advanced threat intelligence
Fortinet’s Advanced Threat Protection (ATP) solution allows your organization to detect and mitigate against threats, both known and unknown, and share that information locally to deliver a coordinated defense.
The ATP solution relies on many types of security technologies, products, and research applied from the network edge through to endpoint devices. To deliver the most effective protection, they are integrated with other security elements from the Enterprise Firewall and Cloud solutions to work together automatically, continuously handing off data from one element to the next to identify, evaluate, and respond to attacks across the entire environment.
The ATP framework delivers end-to-end protection across the attack chain and consists of three elements: prevention, detection, and mitigation, with continuous threat monitoring and analytics from FortiGuard Labs.
For more information about the Advanced Threat Protection Solution, see http://www.fortinet.com/atp.
Partner API
The Fortinet Fabric-Ready Partner Program is an interoperability program for technology alliance partners. Technology alliance partners integrate their products with the Fortinet Security Fabric using Fortinet Security Fabric APIs. Their products are then able to actively collect and share threat and mitigation information from one end of the security solution to the other, which improves threat intelligence, enhances overall threat awareness, and broadens threat response.
Inclusion in the program means that Fabric-Ready Partners have collaborated with Fortinet and leveraged the Fortinet Security Fabric APIs to develop and validate integrated end-to-end security solutions that are ready for deployment.
The Fabric-Ready Partner Program allows Fortinet technology alliance partners to build on Fortinet products and solutions which help your organization get even more value from your security deployment.
For more information about the Fortinet Fabric-Ready Partner Program, see
https://www.fortinet.com/partners/partnerships/alliance-partners.html

