FGSP - FortiGate Session Life Support Protocol
FortiGate Session Life Support Protocol (FGSP) distributes sessions between two entities, which could be standalone FortiGates or an FGCP cluster, and performs session synchronization. If one of the peers fails, session failover occurs and active sessions fail over to the peer that is still operating. This failover occurs without any loss of data. Also, the external routers or load balancers will detect the failover and re-distribute all sessions to the peer that is still operating. FortiGates in both entities must be the same model and must be running the same firmware.
You can use the config system cluster-sync command to configure FGSP between
two FortiGate units.
The FortiGate's HA Heartbeat listens on ports TCP/703, TCP/23, or ETH Layer 2/8890.
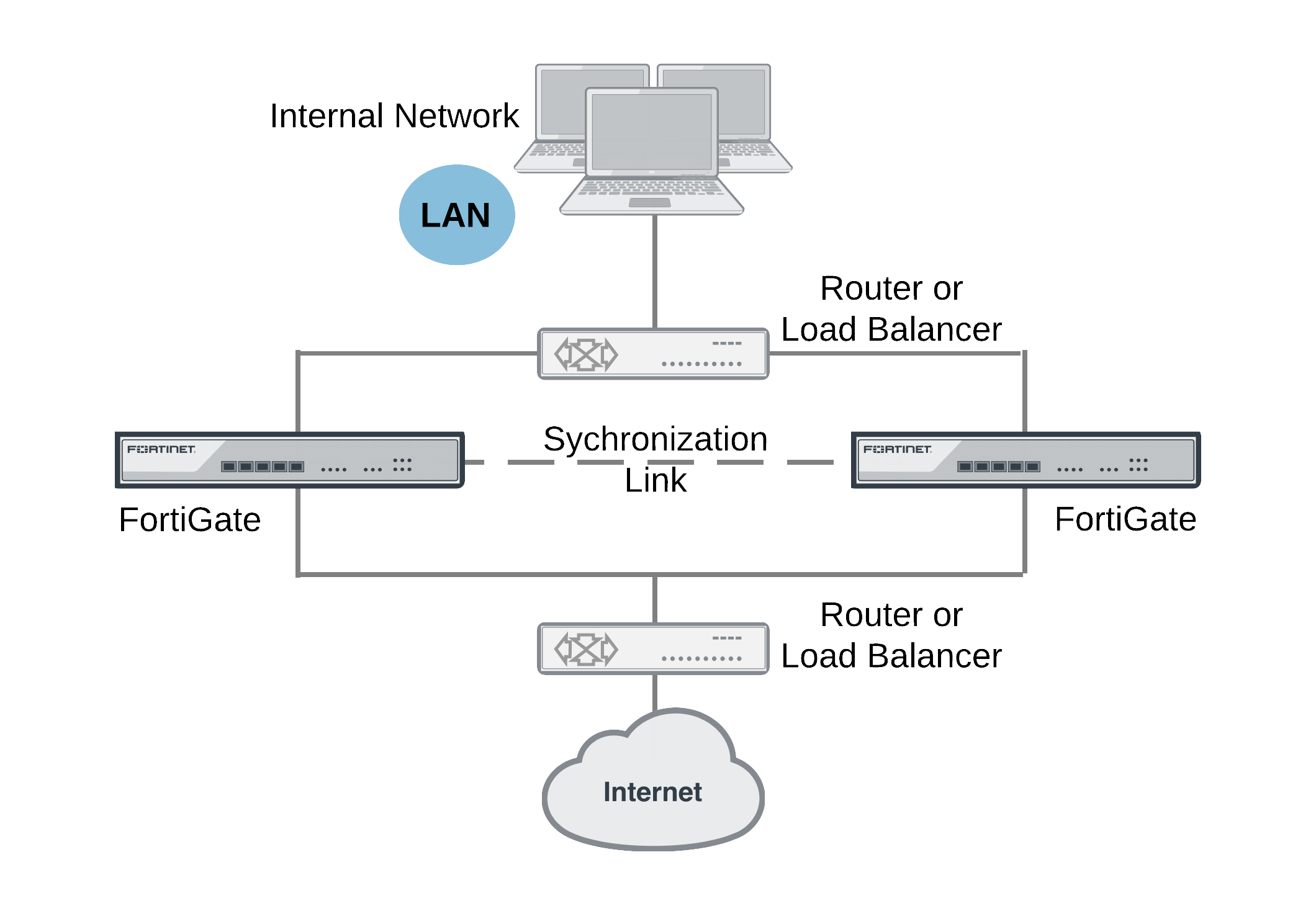
In previous versions of FortiOS, FGSP was called TCP session synchronization or standalone session synchronization. However, FGSP has been expanded to include both IPv4 and IPv6 TCP, UDP, ICMP, expectation, NAT sessions, and IPsec tunnels.
UDP and ICMP (connectionless) session synchronization
In many configurations, due to their non-stateful nature, UDP and ICMP sessions don't need to be synchronized to naturally failover. However, if it is required, you can configure the FGSP to also synchronize UDP and ICMP sessions by entering the following command:
config system ha
set session-pickup enable
set session-pickup-connectionless enable
end
Expectation (asymmetric) session synchronization
Synchronizing asymmetric traffic can be very useful in situations where multiple Internet connections from different ISPs are spread across two FortiGates.
The FGSP enforces firewall policies for asymmetric traffic, including cases where the TCP 3-way handshake is split between two FortiGates. For example, FGT-A receives the TCP-SYN, FGT-B receives the TCP-SYN-ACK, and FGT-A receives the TCP-ACK. Under normal conditions a firewall will drop this connection since the 3-way handshake was not seen by the same firewall. However two FortiGates with FGSP configured will be able to properly pass this traffic since the firewall sessions are synchronized.
If traffic will be highly asymmetric, as described above, the following command must be enabled on both FortiGates:
config system ha
set session-pickup enable
set session-pickup-expectation enable
end
Security profile inspection with asymmetric and symmetric traffic
Security profile inspection, flow- or proxy-based, is not expected to work properly if the traffic in the session is load balanced across more than one FortiGate in either direction. However, flow-based inspection should be used in FGSP deployments.
For symmetric traffic, security profile inspection can be used but with the following limitations:
- No session synchronization for the sessions inspected using proxy-based inspection. Sessions will drop and need to be reestablished after data path failover.
- Sessions with flow-based inspection will failover, and inspection of sessions after a failover may not work.
Improving session synchronization performance
Two HA configuration options are available to reduce the performance impact of enabling session failover (also known as session pickup): reducing the number of sessions that are synchronized by adding a session pickup delay, and using more FortiGate interfaces for session synchronization.
Reducing the number of sessions that are synchronized
If session pickup is enabled, as soon as new sessions are added to the primary unit session table they are synchronized to the peer unit. Enable the session-pickup-delay CLI option to reduce the number of sessions that are synchronized by synchronizing sessions only if they remain active for more than 30 seconds. Enabling this option could greatly reduce the number of sessions that are synchronized if a peer typically processes very many short duration sessions, which is typical of most HTTP traffic for example.
Use the following command to enable a 30-second session pickup delay:
config system ha
set session-pickup-delay enable
end
Enabling session pickup delay means that if a failover occurs, more sessions may not be resumed after a failover. In most cases short duration sessions can be restarted with only a minor traffic interruption. However, if you notice too many sessions not resuming after a failover, you might want to disable this setting.
Using multiple FortiGate interfaces for session synchronization
Using the session-sync-dev option, you can select one or more FortiGate interfaces to use for synchronizing sessions as required for session pickup. Normally session synchronization occurs over the HA heartbeat link. Using this HA option means only the selected interfaces are used for session synchronization and not the HA heartbeat link. If you select more than one interface, session synchronization traffic is load balanced among the selected interfaces.
Moving session synchronization from the HA heartbeat interface reduces the bandwidth required for HA heartbeat traffic and may improve the efficiency and performance of the FGSP deployment, especially if the peers are synchronizing a large number of sessions. Load balancing session synchronization among multiple interfaces can further improve performance and efficiency if the peers are synchronizing a large number of sessions.
Use the following command to perform cluster session synchronization using the port10 and port12 interfaces:
config system ha
set session-sync-dev port10 port12
end
Session synchronization packets use Ethertype 0x8892. The interfaces to use for session synchronization must be connected together either directly using the appropriate cable (possible if there are only two units in the deployment) or using switches. If one of the interfaces becomes disconnected, the peer uses the remaining interfaces for session synchronization. If all of the session synchronization interfaces become disconnected, session synchronization reverts back to using the HA heartbeat link.
Since large amounts of session synchronization traffic can increase network congestion, it is recommended that you keep this traffic off of your network by using dedicated connections for it.
|
|
"Unsetting"
|
NAT session synchronization
NAT sessions are not synchronized by default. You can enable NAT session synchronization by entering the following command:
config system ha
set session-pickup enable
set session-pickup-nat enable
end
After a failover with this configuration, all sessions that include the IP addresses of interfaces on the failed FortiGate unit will have nowhere to
go since the IP addresses of the failed FortiGate unit will no longer be on the network. If you want NAT sessions to resume after a failover you should not configure NAT to use the destination interface IP address, since the FGSP FortiGate units have different IP addresses. To avoid this issue, you should use IP pools with the type set to overload (which is the default IP pool type), as shown in the example below:
config firewall ippool
edit FGSP-pool
set type overload
set startip 172.20.120.10
set endip 172.20.120.20
end
In NAT mode, only sessions for route mode security policies are synchronized. FGSP is also available for FortiGate units or virtual domains operating in transparent mode. Only sessions for normal transparent mode policies are synchronized.
IPsec tunnel synchronization
When you use the config system cluster-sync command to enable FGSP, IPsec keys and other
runtime data are synchronized between cluster units. This means that if one of
the peer units goes down, the peer unit that is still operating can quickly get IPsec tunnels re-established
without re-negotiating them. However, after a failover, all existing tunnel sessions on the failed FortiGate have to
be restarted on the still operating FortiGate.
IPsec tunnel sync only supports dialup IPsec. The interfaces on both FortiGates that are tunnel endpoints must have the same IP addresses and external routers must be configured to load balance IPsec tunnel sessions to the FortiGates in the deployment.
Automatic session synchronization after peer reboot
The following command allows you to configure an automatic session synchronization after a peer FGSP unit has rebooted. FGSP will send out heartbeat signals (every 1–10 seconds, as shown below) if one FortiGate is rebooting and the other FortiGate fails.
To configure automatic session synchronization:
config system session-sync
edit 1
set down-intfs-before-sess-sync <interfaces> - List of interfaces to be turned down before session synchronization is complete.
set-hb-interval <integer> - (1 - 10 seconds)
set hb-lost-threshold <integer> - (1 - 10)
next
end

