Users and user groups
FortiGate authentication controls system access by user group. By assigning individual users to the appropriate user groups you can control each user’s access to network resources. The members of user groups are user accounts, of which there are several types. Local users and peer users are defined on the FortiGate unit. User accounts can also be defined on remote authentication servers.
This section describes how to configure local users and peer users and then how to configure user groups. For information about configuration of authentication servers see Authentication servers.
This section contains the following topics:
Users
A user is a user account consisting of username, password, and in some cases other information, configured on the FortiGate unit or on an external authentication server. Users can access resources that require authentication only if they are members of an allowed user group. There are several different types of user accounts with slightly different methods of authentication:
| User type | Authentication |
|---|---|
| Local user | The username and password must match a user account stored on the FortiGate unit. Authentication by FortiGate security policy. |
| Remote user | The username must match a user account stored on the FortiGate unit and the username and password must match a user account stored on the remote authentication server. FortiOS supports LDAP, RADIUS, and TACACS+ servers. |
| Authentication server user | A FortiGate user group can include user accounts or groups that exist on a remote authentication server. |
| FSSO user | With Fortinet Single Sign On (FSSO), users on a Microsoft Windows or Novell network can use their network authentication to access resources through the FortiGate unit. Access is controlled through FSSO user groups which contain Windows or Novell user groups as their members. |
| PKI or Peer user | A Public Key Infrastructure (PKI) or peer user is a digital certificate holder who authenticates using a client certificate. No password is required, unless two-factor authentication is enabled. |
| IM Users | IM users are not authenticated. The FortiGate unit can allow or block each IM user name from accessing the IM protocols. A global policy for each IM protocol governs access to these protocols by unknown users. |
| Guest Users | Guest user accounts are temporary. The account expires after a selected period of time. |
This section includes:
Local and remote users
Local and remote users are defined on the FortiGate unit in User & Device > User Definition.
| Create New | Creates a new user account. When you select Create New, you are automatically redirected to the User Creation Wizard. |
| Edit User | Modifies a user’s account settings. When you select Edit, you are automatically redirected to the Edit User page. |
| Delete | Removes a user from the list. Removing the user name removes the authentication configured for the user. The Delete icon is not available if the user belongs to a user group. To remove multiple local user accounts from within the list, on the User page, in each of the rows of user accounts you want removed, select the check box and then select Delete. To remove all local user accounts from the list, on the User page, select the check box in the check box column and then select Delete. |
| User Name | The user name. For a remote user, this username must be identical to the username on the authentication server. |
| Type | Local indicates a local user authenticated on the FortiGate unit. For remote users, the type of authentication server is shown: LDAP, RADIUS, or TACACS+. |
| Two-factor Authentication | Indicates whether two-factor authentication is configured for the user. |
| Ref. | Displays the number of times this object is referenced by other objects. Select the number to open the Object Usage window and view the list of referring objects. The list is grouped into expandable categories, such as Firewall Policy. Numbers of objects are shown in parentheses. To view more information about the referring object, use the icons:
|
To create a local or remote user account - web-based manager:
- Go to User & Device > User Definition and select Create New.
- On the Choose User Type page select:
| Local User | Select to authenticate this user using a password stored on the FortiGate unit. |
| Remote RADIUS User Remote TACACS+ User Remote LDAP User |
To authenticate this user using a password stored on an authentication server, select the type of server and then select the server from the list. You can select only a server that has already been added to the FortiGate unit configuration. |
- Select Next and provide user authentication information.
For a local user, enter the User Name and Password.
For a remote user, enter the User Name and the server name.
- Select Next and enter Contact Information.
If email or SMS is used for two-factor authentication, provide the email address or SMS cell number at which the user will receive token password codes. If a custom SMS service is used, it must already be configured. See FortiToken. - Select Next, then on the Provide Extra Info page enter
| Two-factor Authentication | Select to enable two-factor authentication. Then select the Token (FortiToken or FortiToken Mobile) for this user account. See Associating FortiTokens with accounts. |
| User Group | Select the user groups to which this user belongs. |
- Select Create.
To create a local user - CLI example:
Locally authenticated user
config user local
edit user1
set type password
set passwd ljt_pj2gpepfdw
end
To create a remote user - CLI example:
config user local
edit user2
set type ldap
set ldap_server ourLDAPsrv
end
For a RADIUS or TACACS+ user, set type to radius or tacacs+, respectively.
To create a user with FortiToken Mobile two-factor authentication - CLI example:
config user local
edit user5
set type password
set passwd ljt_pj2gpepfdw
set two_factor fortitoken
set fortitoken 182937197
end
Remote users are configured for FortiToken two-factor authentication similarly.
To create a user with SMS two-factor authentication using FortiGuard messaging service - CLI example:
config user local
edit user6
set type password
set passwd 3ww_pjt68dw
set two_factor sms
set sms-server fortiguard
set sms-phone 1365984521
end
To add an SMS service
If you plan on sending SMS notifications to users. you can use the following command to add an email to SMS service to your FortiGate.
config system sms-server
edit <server-name>
set mail-server <server-name>
end
Removing users
Best practices dictate that when a user account is no longer in use, it should be deleted. Removing local and remote users from FortiOS involve the same steps.
If the user account is referenced by any configuration objects, those references must be removed before the user can be deleted. See Removing references to users.
To remove a user from the FortiOS configuration - web-based manager:
- Go to User & Device > User Definition.
- Select the check box of the user that you want to remove.
- Select Delete.
- Select OK.
To remove a user from the FortiOS configuration - CLI example:
config user local
delete user4444
end
Removing references to users
You cannot remove a user that belongs to a user group. Remove the user from the user group first, and then delete the user.
To remove references to a user - web-based manager
- Go to User & Device > User Definition.
- If the number in the far right column for the selected user contains any number other than zero, select it.
- A more detailed list of object references to this user is displayed. Use its information to find and remove these references to allow you to delete this user.
PKI or peer users
A PKI, or peer user, is a digital certificate holder. A PKI user account on the FortiGate unit contains the information required to determine which CA certificate to use to validate the user’s certificate. Peer users can be included in firewall user groups or peer certificate groups used in IPsec VPNs. For more on certificates, see Certificates overview.
To define a peer user you need:
- a peer username
- the text from the subject field of the user’s certificate, or the name of the CA certificate used to validate the user’s certificate
Creating a peer user
The peer user can be configured only in the CLI.
To create a peer user for PKI authentication - CLI example:
config user peer
edit peer1
set subject peer1@mail.example.com
set ca CA_Cert_1
end
There are other configuration settings that can be added or modified for PKI authentication. For example, you can configure the use of an LDAP server to check access rights for client certificates. For information about the detailed PKI configuration settings, see the FortiGate CLI Reference.
Two-factor authentication
The standard logon requires a username and password. This is one factor authentication—your password is one piece of information you need to know to gain access to the system.
Two factor authentication adds the requirement for another piece of information for your logon. Generally the two factors are something you know (password) and something you have (certificate, token, etc.). This makes it harder for a hacker to steal your logon information. For example if you have a FortiToken device, the hacker would need to both use it and know your password to gain entry to your account.
Two-factor authentication is available on both user and admin accounts. But before you enable two-factor authentication on an administrator account, you need to ensure you have a second administrator account configured to guarantee administrator access to the FortiGate unit if you are unable to authenticate on the main admin account for some reason.
|
|
Two-factor authentication does not work with explicit proxies. |
FortiToken extension to comply with PCI 3.2
With multi-factor-authentication enabled as mandatory (see syntax below), all authentication will collect both username/password and OTP as a second factor before presenting an authentication result. The system will log for each factor.
If a user is not configured with two-factor authentication, any OTP or an empty OTP would make the second factor authentication pass.
FortiOS processes the user and password first and then always collects the second factor (if configured) without any indication of the first factor failing or succeeding. FortiOS accepts the second factor even if the first failed (unknown to the user) and returns a login attempt pass or fail, with no indication of which factor failed.
Syntax
config system global
set multi-factor-authentication {optional | mandatory}
end
The methods of two-factor authentication include:
Certificate
You can increase security by requiring both certificate and password authentication for PKI users. Certificates are installed on the user’s computer. Requiring a password also protects against unauthorized use of that computer.
Optionally peer users can enter the code from their FortiToken instead of the certificate.
To create a peer user with two-factor authentication - CLI example
config user peer
edit peer1
set subject E=peer1@mail.example.com
set ca CA_Cert_1
set two-factor enable
set passwd fdktguefheygfe
end
For more information on certificates, see Certificates overview.
Two-factor email authentication sends a randomly generated six digit numeric code to the specified email address. Enter that code when prompted at logon. This token code is valid for 60 seconds. If you enter this code after that time, it will not be accepted.
A benefit is that you do not require mobile service to authenticate. However, a potential issue is if your email server does not deliver the email before the 60 second life of the token expires.
The code will be generated and emailed at the time of logon, so you must have email access at that time to be able to receive the code.
To configure an email provider - web-based manager:
- Go to System > Advanced and enable Use Custom Email Server under Email Service.
- Enter SMTP Server and Default Reply To address.
- If applicable, enable Authentication and enter the SMTP User and Password to use.
- Select a Security Mode, options are: None, SMTPS or STARTTLS.
- Enter the Port number, the default is 25.
- Select Apply.
To configure an email provider - CLI:
config system email-server
set server <server_domain-name>
set reply-to <Recipient_email_address>
end
To enable email two-factor authentication - web-based manager:
- To modify an administrator account, go to System > Administrators. To modify a user account go to User & Device > User Definition.
- Edit the user account.
- Enable and enter the user’s Email Address.
- Select Enable Two-factor Authentication.
- Select Email based two-factor authentication.
- Select OK.
|
|
If Email based two-factor authentication option doesn't appear after selecting Enable Two-factor Authentication, you need to enable it via the CLI as follows. To enable email two-factor authentication - CLI: config user local edit <user_name> set email-to <user_email> set two-factor email end |
SMS
SMS two-factor authentication sends the token code in an SMS text message to the mobile device indicated when this user attempts to logon. This token code is valid for 60 seconds. If you enter this code after that time, it will not be accepted. Enter this code when prompted at logon to be authenticated.
SMS two-factor authentication has the benefit that you do not require email service before logging on. A potential issue is if the mobile service provider does not send the SMS text message before the 60 second life of the token expires.
FortiGuard Messaging Service include four SMS Messages at no cost. If you need more, you should acquire a license through support.fortinet.com or via customer service.
If you do not use the FortiGuard Messaging Service, you need to configure an SMS service.
To configure an SMS service - CLI:
config system sms-server
edit <provider_name>
set mail-server <server_domain-name>
next
end
To configure SMS two-factor authentication - web-based manager:
- To modify an:
- administrator account, go to System > Administrators, or
- user account go to User & Device > User Definition.
- Edit the user account.
- Select SMS and enter the Country Dial Code and Phone Number.
- Select Enable Two-factor Authentication. and select the correct Token.
- Select OK.
If you have problems receiving the token codes via SMS messaging, contact your mobile provider to ensure you are using the correct phone number format to receive text messages and that your current mobile plan allows text messages.
FortiToken
FortiToken is a disconnected one-time password (OTP) generator. It is a small physical device with a button that when pressed displays a six digit authentication code. This code is entered with a user’s username and password as two-factor authentication. The code displayed changes every 60 seconds, and when not in use the LCD screen is blanked to extend the battery life.
There is also a mobile phone application, FortiToken Mobile, that performs much the same function.
FortiTokens have a small hole in one end. This is intended for a lanyard to be inserted so the device can be worn around the neck, or easily stored with other electronic devices. Do not put the FortiToken on a key ring as the metal ring and other metal objects can damage it. The FortiToken is an electronic device like a cell phone and must be treated with similar care.
Any time information about the FortiToken is transmitted, it is encrypted. When the FortiGate unit receives the code that matches the serial number for a particular FortiToken, it is delivered and stored encrypted. This is in keeping with the Fortinet’s commitment to keeping your network highly secured.
FortiTokens can be added to user accounts that are local, IPsec VPN, SSL VPN, and even Administrators. See Associating FortiTokens with accounts.
A FortiToken can be associated with only one account on one FortiGate unit.
If a user loses their FortiToken, it can be locked out using the FortiGate so it will not be used to falsely access the network. Later if found, that FortiToken can be unlocked on the FortiGate to allow access once again. See FortiToken maintenance.
There are three tasks to complete before FortiTokens can be used to authenticate accounts:
- Adding FortiTokens to the FortiGate
- Activating a FortiToken on the FortiGate
- Associating FortiTokens with accounts
In addition, this section includes the following:
The FortiToken authentication process
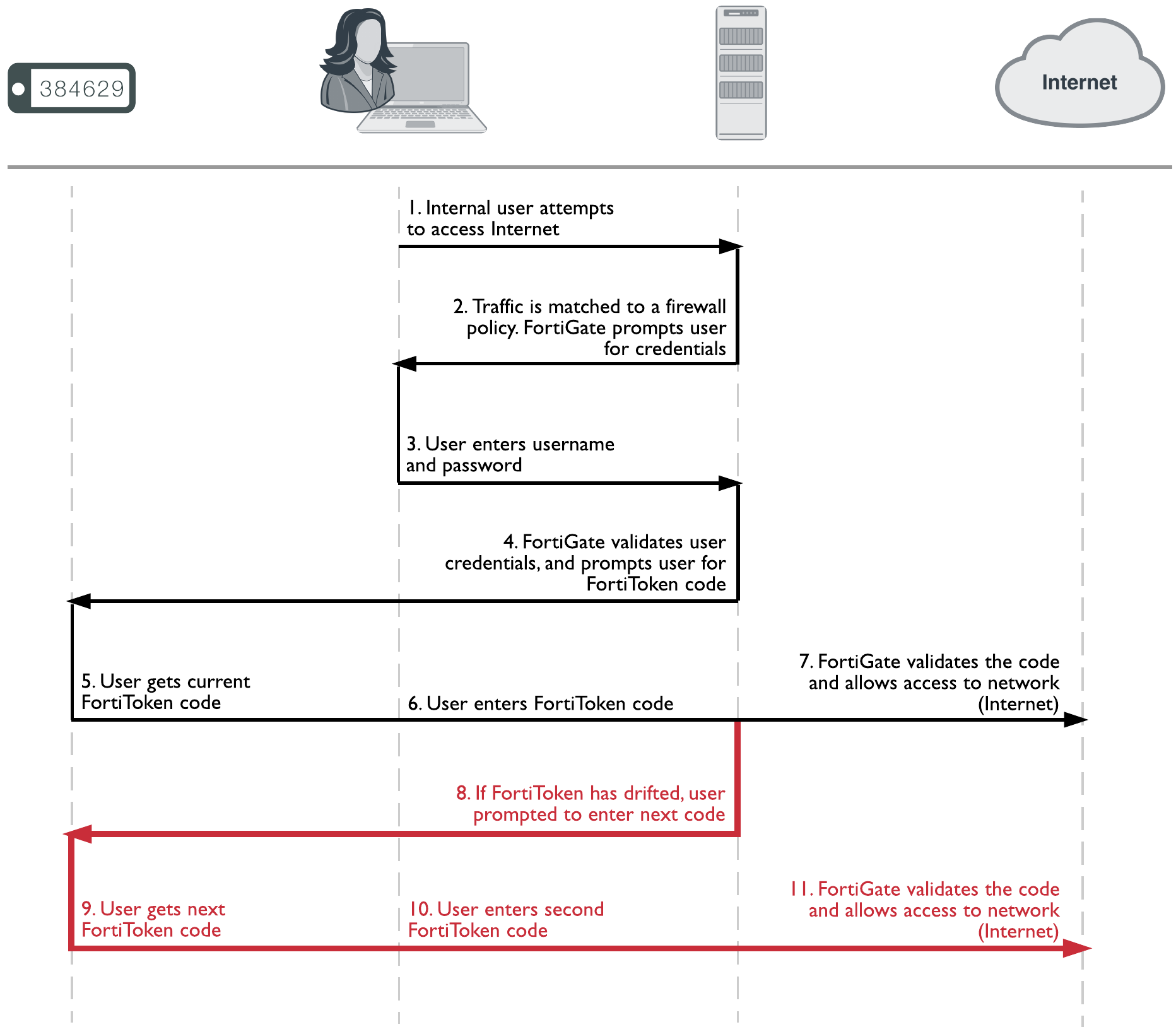
The steps during FortiToken two-factor authentication are as follows.
- User attempts to access a network resource.
- FortiGate unit matches the traffic to an authentication security policy, and FortiGate unit prompts the user for username and password.
- User enters their username and password.
- FortiGate unit verifies their information, and if valid prompts the user for the FortiToken code.
- User gets the current code from their FortiToken device.
- User enters current code at the prompt.
- FortiGate unit verifies the FortiToken code, and if valid allows access to the network resources such as the Internet.
The following steps are needed only if the time on the FortiToken has drifted and needs to be re-synchronized with the time on the FortiGate unit. - If time on FortiToken has drifted, FortiGate unit will prompt user to enter a second code to confirm.
- User gets the next code from their FortiToken device
- User enters the second code at the prompt.
- FortiGate unit uses both codes to update its clock to match the FortiToken and then proceeds as in step Users and user groups.
The FortiToken authentication process is illustrated below:
When configured the FortiGate unit accepts the username and password, authenticates them either locally or remotely, and prompts the user for the FortiToken code. The FortiGate then authenticates the FortiToken code. When FortiToken authentication is enabled, the prompt field for entering the FortiToken code is automatically added to the authentication screens.
Even when an Administrator is logging in through a serial or Telnet connection and their account is linked to a FortiToken, that Administrator will be prompted for the token’s code at each login.
|
|
If you have attempted to add invalid FortiToken serial numbers, there will be no error message. The serial numbers will simply not be added to the list. |
Adding FortiTokens to the FortiGate
Before one or more FortiTokens can be used to authenticate logons, they must be added to the FortiGate. The import feature is used to enter many FortiToken serial numbers at one time. The serial number file must be a text file with one FortiToken serial number per line.
|
|
Both FortiToken Mobile and physical FortiTokens store their encryption seeds on the cloud, therefore you will only be able to register them to a single FortiGate or FortiAuthenticator. Because FortiToken-200CD seed files are stored on the CD, these tokens can be registered on multiple FortiGates and/or FortiAuthenticators, but not simultaneously. |
To manually add a FortiToken to the FortiGate - web-based manager:
- Go to User & Device > FortiTokens.
- Select Create New.
- In Type, select Hard Token or Mobile Token.
- Enter one or more FortiToken serial numbers (hard token) or activation codes (mobile token).
- Select OK.
|
|
For mobile token, you receive the activation code in the license certificate once you purchase a license. FortiOS include a license for two mobile token at no cost. |
To import multiple FortiTokens to the FortiGate - web-based manager:
- Go to User & Device > FortiTokens.
- Select Create New.
- In Type, select Hard Token.
- Select Import.
- Select Serial Number File or Seed File, depending on which file you have.
- Browse to the local file location on your local computer.
- Select OK.
The file is imported. - Select OK.
To import FortiTokens to the FortiGate from external sources - CLI:
FortiToken seed files (both physical and mobile versions) can be imported from either FTP or TFTP servers, or a USB drive, allowing seed files to be imported from an external source more easily:
execute fortitoken import ftp <file name> <ip>[:ftp port] <Enter> <user> <password>
execute fortitoken import tftp <file name> <ip>
execute fortitoken import usb <file name>
|
|
To import seed files for FortiToken Mobile, replace fortitoken with fortitoken-mobile. |
To add two FortiTokens to the FortiGate - CLI:
config user fortitoken
edit <serial_number>
next
edit <serial_number2>
next
end
Activating a FortiToken on the FortiGate
Once one or more FortiTokens have been added to the FortiGate unit, they must be activated before being available to be associated with accounts. The process of activation involves the FortiGate querying FortiGuard servers about the validity of each FortiToken. The serial number and information is encrypted before it is sent for added security.
|
|
A FortiGate unit requires a connection to FortiGuard servers to activate a FortiToken. |
To activate a FortiToken on the FortiGate unit - web-based manager:
- Go to User & Device > FortiTokens.
- Select one or more FortiTokens with a status of Available.
- Right-click the FortiToken entry and select Activate.
- Select Refresh.
The status of selected FortiTokens will change to Activated.
The selected FortiTokens are now available for use with user and admin accounts.
To activate a FortiToken on the FortiGate unit - CLI:
config user fortitoken
edit <token_serial_num>
set status activate
next
end
Associating FortiTokens with accounts
The final step before using the FortiTokens to authenticate logons is associating a FortiToken with an account. The accounts can be local user or administrator accounts.
To add a FortiToken to a local user account - web-based manager:
- Ensure that your FortiToken serial number has been added to the FortiGate successfully, and its status is Available.
- Go to User & Device > User Definition, and edit the user account.
- Enter the user's Email Address.
- Enable Two-factor Authentication.
- Select the user's FortiToken serial number from the Token list.
- Select OK.
|
|
For mobile token, click on Send Activation Code to be sent to the email address configured previously. The user will use this code to activate his mobile token. An Email Service has to be set under System > Advanced in order to send the activation code. |
To add a FortiToken to a local user account - CLI:
config user local
edit <username>
set type password
set passwd "myPassword"
set two-factor fortitoken
set fortitoken <serial_number>
set email-to "username@example.com"
set status enable
next
end
To add a FortiToken to an administrator account - web-based manager:
- Ensure that your FortiToken serial number has been added to the FortiGate successfully, and its status is Available.
- Go to System > Administrators, and edit the admin account.
This account is assumed to be configured except for two-factor authentication. - Enter admin's Email Address.
- Enable Two-factor Authentication.
- Select the user's FortiToken serial number from the Token list.
- Select OK.
|
|
For mobile token, click on Send Activation Code to be sent to the email address configured previously. The admin will use this code to activate his mobile token. An Email Service has to be set under System > Advanced in order to send the activation code. |
To add a FortiToken to an administrator account - CLI:
config system admin
edit <username>
set password "myPassword"
set two-factor fortitoken
set fortitoken <serial_number>
set email-to "username@example.com"
next
end
The fortitoken keyword will not be visible until fortitoken is selected for the two-factor option.
|
|
Before a new FortiToken can be used, it may need to be synchronized due to clock drift. |
FortiToken maintenance
Once FortiTokens are entered into the FortiGate unit, there are only two tasks to maintain them — changing the status,
To change the status of a FortiToken between activated and locked - CLI:
config user fortitoken
edit <token_serial_num>
set status lock
next
end
Any user attempting to login using this FortiToken will not be able to authenticate.
To list the drift on all FortiTokens configured on this FortiGate unit - CLI:
# diag fortitoken info
FORTITOKEN DRIFT STATUS
FTK2000BHV1KRZCC 0 token already activated, and seed won't be returned
FTK2001C5YCRRVEE 0 token already activated, and seed won't be returned
FTKMOB4B94972FBA 0 provisioned
FTKMOB4BA4BE9B84 0 new
Total activated token: 0
Total global activated token: 0
Token server status: reachable
This command lists the serial number and drift for each FortiToken configured on this FortiGate unit. This command is useful to check if it is necessary to synchronize the FortiGate and any particular FortiTokens.
FortiToken Mobile Push
A command under config system ftm-push allows you to configure the FortiToken Mobile Push services server IP address and port number. The Push service is provided by Apple (APNS) and Google (GCM) for iPhone and Android smartphones respectively. This will help to avoid tokens becoming locked after an already enabled two-factor authentication user has been disabled.
CLI syntax
config system ftm-push
set server-ip <ip-address>
set server-port [1-65535] Default is 4433.
end
Note that the server-ip is the public IP address of the FortiGate interface that the FTM will call back to; it is the IP address used by the FortiGate for incoming FTM calls.
If an SSL VPN user authenticates with their token, then logs out and attempts to reauthenticate again within a minute, a new message will display showing "Please wait x seconds to login again." This replaces a previous error/permission denied message.
The "x" value will depend on the calculation of how much time is left in the current time step.
CLI syntax
config system interface
edit <name>
set allowaccess ftm
next
end
|
|
FortiGate supports when the FortiAuthenticator initiates FTM Push notifications, for when users are attempting to authenticate through a VPN and/or RADIUS (with FortiAuthenticator as the RADIUS server). |
Monitoring users
To monitor user activity in the web-based manager, go to Monitor > Firewall User Monitor. The list of users who are logged on is displayed with some information about them such as their user group, security policy ID, how long they have been logged on, their IP address, traffic volume, and their authentication method as one of FSSO, NTLM, or firewall (FW-auth).
From this screen you can de-authenticate all users who are logged on. The de-authenticate button is at the top left of this screen.
To see information about banned users go to Monitor > Quarantine Monitor. Displayed information about users who have been banned includes what application the triggered the ban (Application Protocol), the reason for the ban (Cause or rule), Created, and when the ban expires.
Filtering the list of users
When there are many users logged on, it can be difficult to locate a specific user or multiple users to analyze. Applying filters to the list allows you to organize the user list to meet your needs, or only display some the users that meet your current requirements.
Select settings bottom at the top right of the screen to adjust columns that are displayed for users, including what order they are displayed in. This can be very helpful in locating information you are looking for.
Each column heading has a grey filter icon. Click on the filter icon to configure a filter for the data displayed in that column. Each column has similar options including a field to enter the filtering information, a check box to select the negative of the text in the field, and the options to add more fields, apply the filter, clear all filters, or cancel without saving. To enter multiple terms in the field, separate each of them with a comma. To filter entries that contain a specific prefix, use an * (asterisk).
For example, to create a filter to display only users with an IP address of 10.11.101.x who authenticated using one of security policies five through eight, and who belong to the user group Accounting.
- Go to Monitor > Quarantine Monitor.
- Enter
10.11.101.* and select Apply. - Select the filter icon beside Policy ID.
- Enter
5-8and select Apply. - Select the filter icon beside User Group.
- Enter
Accountingand select Apply.
User groups
A user group is a list of user identities. An identity can be:
- a local user account (username/password stored on the FortiGate unit
- a remote user account (password stored on a RADIUS, LDAP, or TACACS+ server)
- a PKI user account with digital client authentication certificate stored on the FortiGate unit
- a RADIUS, LDAP, or TACACS+ server, optionally specifying particular user groups on that server
- a user group defined on an FSSO server.
Security policies and some types of VPN configurations allow access to specified user groups only. This restricted access enforces Role Based Access Control (RBAC) to your organization’s network and its resources. Users must be in a group and that group must be part of the security policy.
In most cases, the FortiGate unit authenticates users by requesting their username and password. The FortiGate unit checks local user accounts first. If a match is not found, the FortiGate unit checks the RADIUS, LDAP, or TACACS+ servers that belong to the user group. Authentication succeeds when a matching username and password are found. If the user belongs to multiple groups on a server, those groups will be matched as well.
|
|
FortiOS does not allow username overlaps between RADIUS, LDAP, or TACACS+ servers. |
There are four types of FortiGate user groups: Firewall, FSSO, Guest, and RADIUS single sign-on (RSSO) user groups.
Firewall user groups
Firewall user groups are used locally as part of authentication. When a security policy allows access only to specified user groups, users must authenticate. If the user authenticates successfully and is a member of one of the permitted groups, the session is allowed to proceed.
This section includes:
SSL VPN access
SSL VPN settings include a list of the firewall user groups that can access the SSL VPN and the SSL VPN portal that each group will use. When the user connects to the FortiGate unit via HTTPS on the SSL VPN port (default 10443), the FortiGate unit requests a username and password.
SSL VPN access also requires a security policy where the destination is the SSL interface.
IPsec VPN access
A firewall user group can provide access for dialup users of an IPsec VPN. In this case, the IPsec VPN phase 1 configuration uses the Accept peer ID in dialup group peer option. The user’s VPN client is configured with the username as peer ID and the password as pre-shared key. The user can connect successfully to the IPsec VPN only if the username is a member of the allowed user group and the password matches the one stored on the FortiGate unit.
|
|
A user group cannot be used as a dialup group if any member of the group is authenticated using an external authentication server. |
Configuring a firewall user group
A user group can contain:
- local users, whether authenticated by the FortiGate unit or an authentication server
- PKI users
- authentication servers, optionally specifying particular user groups on the server
To create a Firewall user group - web-based manager:
- Go to User & Device > User Groups and select Create New.
- Enter a name for the user group.
- In Type, select Firewall.
- Add user names to to the Members list.
- Add authentication servers to the Remote groups list.
By default all user accounts on the authentication server are members of this FortiGate user group. To include only specific user groups from the authentication server, deselect Any and enter the group name in the appropriate format for the type of server. For example, an LDAP server requires LDAP format, such as: cn=users,dn=office,dn=example,dn=com
Remote servers must already be configured in User & Device. - Select OK.
To create a firewall user group - CLI example:
In this example, the members of accounting_group are User1 and all of the members of rad_accounting_group on myRADIUS external RADIUS server.
config user group
edit accounting_group
set group-type firewall
set member User1 myRADIUS
config match
edit 0
set server-name myRADIUS
set group-name rad_accounting_group
end
end
|
|
Normal firewall authentication by external servers might not work if the list of group memberships is larger than 8000 bytes. Group names beyond this limit are ignored. |
server_name is the name of the RADIUS, LDAP, or TACACS+ server, but it must be a member of this group first and must also be a configured remote server on the FortiGate unit.
group_name is the name of the group on the RADIUS, LDAP, or TACACS+ server such as “engineering” or “cn=users,dc=test,dc=com”.
Before using group matching with TACACS+, you must first enable authentication. For example if you have a configured TACACS+ server called myTACS, use the following CLI commands.
config user tacacs+
edit myTACS
set authorization enable
next
end
User group timeouts
User groups can have timeout values per group in addition to FortiGate-wide timeouts. There are essentially three different types of timeouts that are configurable for user authentication on the FortiGate unit — idle timeout, hard timeout, and session timeout. These are in addition to any external timeouts such as those associated with RADIUS servers.
If VDOMs are enabled, the global level user setting authtimeout is the default all VDOMs inherit. If VDOMs are not enabled, user settings authtimeout is the default. The default timeout value is used when the authtimeout keyword for a user group is set to zero.
Each type of timeout will be demonstrated using the existing user group example_group. Timeout units are minutes. A value of zero indicates the global timeout is used.
Membership in multiple groups
When a user belongs to multiple groups in RADIUS groups, the group auth-timeout values are ignored. Instead the global timeout value is used. The default value is 5 minutes, but it can be set from 1 to 43200 minutes (30 days).
config user setting
set auth-timeout-type idle-timeout
set auth-timeout 300
end
Idle timeout
The default type of timeout is idle timeout. When a user initiates a session, it starts a timer. As long as data is transferred in this session, the timer continually resets. If data flow stops, the timer is allowed to advance until it reaches its limit. At that time the user has been idle for too long, and the user is forced to re-authenticate before traffic is allowed to continue in that session.
To configure user group authentication idle timeout - CLI:
config user settings
set auth-timeout-type idle-timeout
end
config user group
edit example_group
set authtimeout 5 //range is 0-43200 minutes (0 = use global authtimeout value)
next
end
Hard timeout
Where the idle timeout is reset with traffic, the hard timeout is absolute. From the time the first session a user establishes starts, the hard timeout counter starts. When the timeout is reached, all the sessions for that user must be re-authenticated. This timeout is not affected by any event.
To configure user group authentication hard timeout - CLI:
config user settings
set auth-timeout-type hard-timeout
end
config user group
edit example_group
set authtimeout 43200 //range is 0-43200 minutes (0 = use global authtimeout value)
next
end
Session timeout
The session timeout works much like the hard timeout in that its an absolute timer that can not be affected by events. However, when the timeout is reached existing sessions may continue but new sessions are not allowed until re-authentication takes place.
To configure a user group authentication new session hard timeout - CLI:
config user setting
set auth-timeout-type new-session
end
config user group
edit example_group
set authtimeout 30 //range is 0-43200 minutes (0 = use global authtimeout value)
next
end
SSO user groups
SSO user groups are part of FSSO authentication and contain only Windows or Novell network users. No other user types are permitted as members. Information about the Windows or Novell user groups and the logon activities of their members is provided by the Fortinet Single Sign On (FSSO) which is installed on the network domain controllers.
You can specify FSSO user groups in security policies in the same way as you specify firewall user groups. FSSO user groups cannot have SSL VPN or dialup IPsec VPN access.
For information about configuring FSSO user groups, see Creating FSSO user groups. For complete information about installing and configuring FSSO, see Agent-based FSSO.
Configuring peer user groups
Peer user groups can only be configured using the CLI. Peers are digital certificate holders defined using the config user peer command. The peer groups you define here are used in dialup IPsec VPN configurations that accept RSA certificate authentication from members of a peer certificate group.
To create a peer group - CLI
config user peergrp
edit vpn_peergrp1
set member pki_user1 pki_user2 pki_user3
end
Viewing, editing, and deleting user groups
To view the list of FortiGate user groups, go to User & Device > User Groups.
Editing a user group
When editing a user group in the CLI you must set the type of group this will be — either a firewall group, a Fortinet Single Sign-On Service group (FSSO), a Radius based Single Sign-On Service group (RSSO), or a guest group. Once the type of group is set, and members are added you cannot change the group type without removing the members.
In the web-based manager, if you change the type of the group any members will be removed automatically.
To edit a user group - web-based manager
- Go to User & Device > User Groups.
- Select the user group that you want to edit.
- Select the Edit button.
- Modify the user group as needed.
- Select OK.
To edit a user group - CLI
This example adds user3 to Group1. Note that you must re-specify the full list of users:
config user group
edit Group1
set group-type firewall
set member user2 user4 user3
end
Deleting a user group
Before you delete a user group, you must ensure there are no objects referring to, it such as security policies. If there are, you must remove those references before you are able to delete the user group.
To remove a user group - web‑based manager
- Go to User & Device > User Groups.
- Select the user group that you want to remove.
- Select the Delete button.
- Select OK.
To remove a user group - CLI
config user group
delete Group2
end
SSL renegotiation in firewall authentication
The auth-ssl-allow-renegotiation option is available under config user setting to allow/forbid SSL renegotiation in firewall authentication. The default value is disable, where a session would be terminated by authd once renegotiation is detected and this login would be recorded as a failure. Other behavior follows regular authentication settings.
To enable SSL renegotiation - CLI
config user setting
set auth-ssl-allow-renegotiation enable
end

