Configuration example: SIP in Transparent Mode
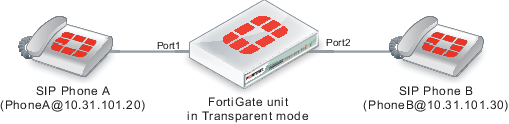
The figure below shows an example SIP network consisting of a FortiGate operating in Transparent mode between two SIP phones. Since the FortiGate is operating in Transparent mode both phones are on the same network and the FortiGate and the SIP ALG does not perform NAT. Even though the SIP ALG is not performing NAT you can use this configuration to apply SIP security features to the SIP traffic.
The FortiGate requires two security policies that accept SIP packets. One to allow SIP Phone A to start a session with SIP Phone B and one to allow SIP Phone B to start a session with SIP Phone A.
SIP network with FortiGate in Transparent mode
General configuration steps
The following general configuration steps are required for this SIP configuration. This example uses the default VoIP profile. The example also includes security policies that specifically allow SIP sessions using UDP port 5060 from Phone A to Phone B and from Phone B to Phone A. In most cases you would have more than two phones so would use more general security policies. Also, you can set the security service to ALLto allow traffic other than SIP on UDP port 5060.
- Add firewall addresses for Phone A and Phone B.
- Add a security policy that accepts SIP sessions initiated by Phone A and includes the default VoIP profile.
- Add a security policy that accepts SIP sessions initiated by Phone B and includes the default VoIP profile.
Configuration steps - GUI
|
|
Before you begin this procedure you may have to go to System > Feature Visibility and turn on VoIP. |
To add firewall addresses for the SIP phones
- Go to Policy & Objects > Addresses.
- Add the following addresses for Phone A and Phone B:
| Category | Address |
| Name | Phone_A |
| Type | IP/Netmask |
| Subnet / IP Range | 10.31.101.20/255.255.255.255 |
| Interface | port1 |
| Category | Address |
| Name | Phone_B |
| Type | IP/Netmask |
| Subnet / IP Range | 10.31.101.30/255.255.255.255 |
| Interface | port2 |
To add security policies to apply the SIP ALG to SIP sessions
- Go to Policy & Objects > IPv4 Policy.
- Add a security policy to allow Phone A to send SIP request messages to Phone B:
| Incoming Interface | port1 |
| Outgoing Interface | port2 |
| Source | Phone_A |
| Destination Address | Phone_B |
| Schedule | always |
| Service | SIP |
| Action | ACCEPT |
- Turn on VoIP and select the default VoIP profile.
- Select OK.
- Add a security policy to allow Phone B to send SIP request messages to Phone A:
| Incoming Interface | port2 |
| Outgoing Interface | port1 |
| Source | Phone_B |
| Destination Address | Phone_A |
| Schedule | always |
| Service | SIP |
| Action | ACCEPT |
- Turn on VoIP and select the default VoIP profile.
- Select OK.
Configuration steps - CLI
To add firewall addresses for Phone A and Phone B and security policies to apply the SIP ALG to SIP sessions
- Enter the following command to add firewall addresses for Phone A and Phone B.
config firewall address
edit Phone_A
set associated-interface port1
set type ipmask
set subnet 10.31.101.20 255.255.255.255
next
edit Phone_B
set associated-interface port2
set type ipmask
set subnet 10.31.101.30 255.255.255.255
end
- Enter the following command to add security policies to allow Phone A to send SIP request messages to Phone B and Phone B to send SIP request messages to Phone A.
config firewall policy
edit 0
set srcintf port1
set dstintf port2
set srcaddr Phone_A
set dstaddr Phone_B
set action accept
set schedule always
set service SIP
set utm-status enable
set voip-profile default
next
edit 0
set srcintf port2
set dstintf port1
set srcaddr Phone_B
set dstaddr Phone_A
set action accept
set schedule always
set service SIP
set utm-status enable
set voip-profile default
end

