Lightweight Directory Access Protocol (LDAP) is an application protocol for accessing and maintaining distributed directory information services over a network. When using LDAP, authentication clients may send “Bind” messages to servers for authentication. Depending on the circumstances, clients may send different kinds of “Bind” messages.
In a server load-balancing client authentication or admin authentication scenario, FortiADC sends binding request to the LDAP server for client authentication. Once a client is successfully authenticated, he or she can then access the LDAP server based on his or her privileges. There are three bind types: simple, anonymous, and regular.
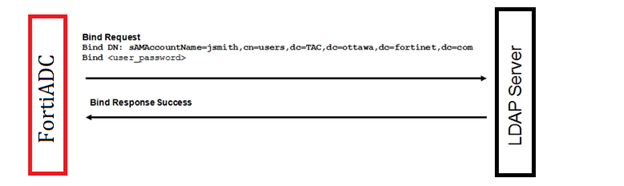
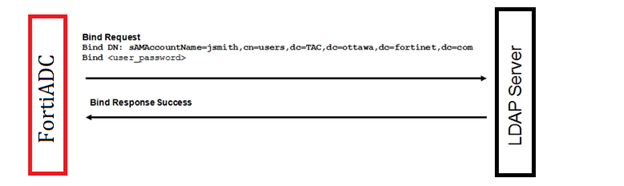
Simple bind means binding with a client's full name. All clients must be located in the same branch specified with the DN.
Anonymous bind should be used only if the LDAP server allows it. The LDAP server searches for the client in the entire sub-branches, starting from the specified DN. This bind has two steps: First, FortiADC sends the binding request to specify the search entry point. Then, it sends a search request with the specified scope and filter to the LDAP server to find the given client.
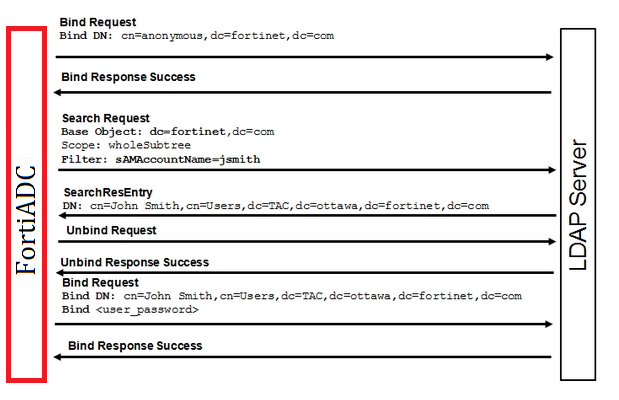
Regular bind can be used when anonymous binding is not allowed on the LDAP server. Regular bind is similar to anonymous bind. The difference is in the initial step. Unlike anonymous bind, regular bind requires that FortiADC get the access privileges on the LDAP server with the specified User DN in the first step. After it has obtained the authorization, FortiADC can then move on to the second step as it does in anonymous bind.

LDAP over SSL (LDAPS) and startTLS are used to encrypt LDAP messages in the authentication process.
LDAPS is a mechanism for establishing an encrypted SSL/TLS connection for LDAP. It requires the use of a separate port, commonly 636. StartTLS extended operation is LDAPv3 standard mechanism for enabling TLS (SSL) data confidentiality protection. The mechanism uses an LDAPv3 extended operation to establish an encrypted SSL/TLS connection within an already established LDAP connection.
You can use an LDAP authentication server to authenticate administrator or destination server user log-ins.
Before you begin:
| Settings | Guidelines |
|---|---|
|
Name |
Configuration name. Valid characters are After you initially save the configuration, you cannot edit the name. |
|
Server |
IP address for the server. |
|
Port |
Port number for the server. The commonly used port for LDAP is 389. |
|
Common Name Identifier |
Common name (cn) attribute for the LDAP record. For example: |
|
Distinguished Name |
Distinguished name (dn) attribute for the LDAP record. The dn uniquely identifies a user in the LDAP directory. For example: |
|
Bind Type |
|
|
User DN |
Available only when Bind Type is "Regular". In that case, enter the user DN. |
|
Password |
Available only when Bind Type is "Regular". In that case, enter the user password. |
|
Secure Connection |
|
|
CA Profile |
This field becomes available only when Secure Connection is set to LDAPS or STARTTLS, regardless of the Bind type being selected. In that case, you can either select a CA that has already been provisioned to secure the connection. You may also leave the field blank if you do not want to secure the connection. |